A lot more than a dozen security flaws have been disclosed in E11, a wise intercom product made by Chinese firm Akuvox.
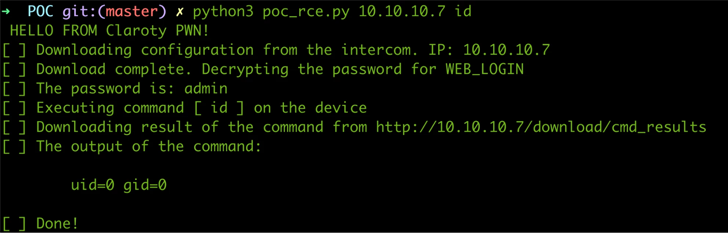
“The vulnerabilities could allow for attackers to execute code remotely in buy to activate and command the device’s digital camera and microphone, steal movie and photographs, or acquire a network foothold,” Claroty security researcher Vera Mens mentioned in a complex write-up.
Akuvox E11 is described by the corporation on its site as a “SIP [Session Initiation Protocol] video clip doorphone specially created for villas, houses, and residences.”
The product listing, having said that, has been taken down from the site, exhibiting an mistake message: “Website page does not exist.” A snapshot captured by Google reveals that the web site was are living as just lately as March 12, 2023, 05:59:51 GMT.
The assaults can manifest both through distant code execution in the local space network (LAN) or remote activation of the E11’s digital camera and microphone, allowing the adversary to collect and exfiltrate multimedia recordings.
A third attack vector requires gain of an external, insecure file transfer protocol (FTP) server to down load saved illustrations or photos and facts.
The most intense of the issues are as follows –
- CVE-2023-0344 (CVSS score: 9.1) – Akuvox E11 seems to be utilizing a custom made variation of dropbear SSH server. This server makes it possible for an insecure solution that by default is not in the formal dropbear SSH server.
- CVE-2023-0345 (CVSS rating: 9.8) – The Akuvox E11 secure shell (SSH) server is enabled by default and can be accessed by the root person. This password cannot be modified by the user.
- CVE-2023-0352 (CVSS score: 9.1) – The Akuvox E11 password recovery webpage can be accessed with out authentication, and an attacker could down load the gadget vital file. An attacker could then use this webpage to reset the password back to the default.
- CVE-2023-0354 (CVSS score: 9.1) – The Akuvox E11 web server can be accessed devoid of any consumer authentication, and this could permit an attacker to access delicate information, as properly as make and download packet captures with identified default URLs.
A the vast majority of the 13 security issues stay unpatched to day, with the industrial and IoT security company noting that Akuvox has considering the fact that dealt with the FTP server permissions issue by disabling the “the skill to checklist its content material so malicious actors could not enumerate data files any longer.”
WEBINARDiscover the Hidden Hazards of Third-Occasion SaaS Apps
Are you mindful of the hazards connected with third-celebration app entry to your firm’s SaaS apps? Be a part of our webinar to master about the kinds of permissions currently being granted and how to decrease risk.
RESERVE YOUR SEAT
The results have also prompted the U.S. Cybersecurity and Infrastructure Security Company (CISA) to launch an Industrial Regulate Techniques (ICS) advisory of its individual final 7 days.
“Prosperous exploitation of these vulnerabilities could bring about reduction of delicate info, unauthorized obtain, and grant total administrative control to an attacker,” the agency cautioned.
In the absence of patches, organizations utilizing the doorphone are advised to disconnect it from the internet until the vulnerabilities are mounted to mitigate opportunity distant assaults.
It truly is also recommended to change the default password made use of to secure the web interface and “section and isolate the Akuvox gadget from the rest of the organization network” to avert lateral movement assaults.
The enhancement will come as Wago released patches for a number of of its programmable logic controllers (PLCs) to address 4 vulnerabilities (CVE-2022-45137, CVE-2022-45138, CVE-2022-45139, and CVE-2022-45140) two of which could be exploited to achieve complete process compromise.
Located this short article exciting? Adhere to us on Twitter and LinkedIn to browse a lot more exceptional information we post.
Some parts of this article are sourced from:
thehackernews.com


 KamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets
KamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets