Cybersecurity scientists have uncovered weaknesses in a application implementation of the Border Gateway Protocol (BGP) that could be weaponized to attain a denial-of-support (DoS) affliction on susceptible BGP friends.
The three vulnerabilities reside in variation 8.4 of FRRouting, a well-known open up resource internet routing protocol suite for Linux and Unix platforms. It is really at present applied by various suppliers like NVIDIA Cumulus, DENT, and SONiC, posing offer chain hazards.
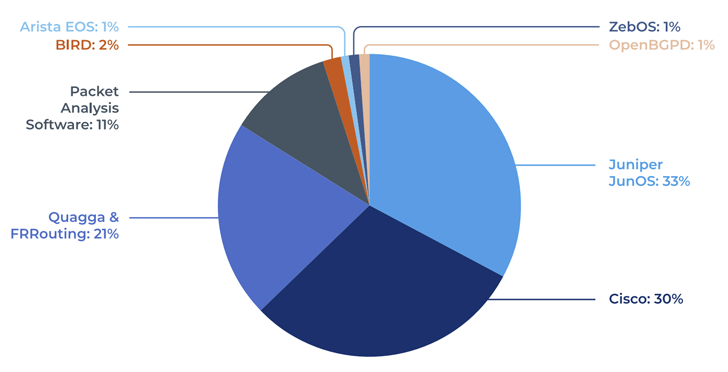
The discovery is the final result of an investigation of seven unique implementations of BGP carried out by Forescout Vedere Labs: FRRouting, Hen, OpenBGPd, Mikrotik RouterOS, Juniper JunOS, Cisco IOS, and Arista EOS.
BGP is a gateway protocol that’s designed to trade routing and reachability data among autonomous techniques. It is really made use of to discover the most productive routes for offering internet traffic.

The checklist of 3 flaws is as follows –
- CVE-2022-40302 (CVSS rating: 6.5) – Out-of-bounds browse when processing a malformed BGP Open concept with an Extended Optional Parameters Duration possibility.
- CVE-2022-40318 (CVSS score: 6.5) – Out-of-bounds read through when processing a malformed BGP Open message with an Extended Optional Parameters Duration selection.
- CVE-2022-43681 (CVSS score: 6.5) – Out-of-bounds browse when processing a malformed BGP Open up information that abruptly ends with the alternative size octet.
The issues “could be exploited by attackers to realize a DoS affliction on vulnerable BGP friends, thus dropping all BGP periods and routing tables and rendering the peer unresponsive,” the enterprise reported in a report shared with The Hacker News.
“The DoS problem may be extended indefinitely by consistently sending malformed packets. The primary root induce is the identical vulnerable code pattern copied into a number of capabilities related to various phases of parsing Open up messages.”
A threat actor could spoof a legitimate IP address of a dependable BGP peer or exploit other flaws and misconfigurations to compromise a genuine peer and then issue a specially-crafted unsolicited BGP Open message.
This is reached by taking gain of the fact that “FRRouting starts to procedure Open messages (e.g., decapsulating optional parameters) ahead of it gets a chance to verify the BGP Identifier and ASN fields of the originating router.”
Impending WEBINARLearn to Cease Ransomware with Real-Time Security
Be a part of our webinar and study how to stop ransomware assaults in their tracks with authentic-time MFA and provider account defense.
Conserve My Seat!
Forescout has also produced accessible an open up resource software identified as bgp_boofuzzer that lets organizations to check the security of the BGP suites made use of internally as properly as discover new flaws in BGP implementations.
“Modern day BGP implementations even now have reduced-hanging fruits that can be abused by attackers,” Forescout explained. “To mitigate the risk of susceptible BGP implementations, […] the most effective advice is to patch network infrastructure units as typically as doable.”
The conclusions arrive months immediately after ESET identified that secondhand routers previously made use of in enterprise networking environments harbored delicate facts, which includes company qualifications, VPN aspects, cryptographic keys, and other crucial shopper data.
“In the wrong hands, the information gleaned from the devices – which includes purchaser data, router-to-router authentication keys, software lists, and much much more – is enough to start a cyberattack,” the Slovak cybersecurity organization mentioned.
Found this short article exciting? Adhere to us on Twitter and LinkedIn to go through extra distinctive content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 BouldSpy Android Spyware: Iranian Government’s Alleged Tool for Spying on Minority Groups
BouldSpy Android Spyware: Iranian Government’s Alleged Tool for Spying on Minority Groups