An Android spyware software has been noticed masquerading as a “Procedure Supervisor” provider to stealthily siphon sensitive information stored in the infected gadgets.
Interestingly, the app — that has the offer identify “com.remote.app” — establishes contact with a distant command-and-command server, 82.146.35[.]240, which has been previously identified as infrastructure belonging to the Russia-centered hacking group recognised as Turla.
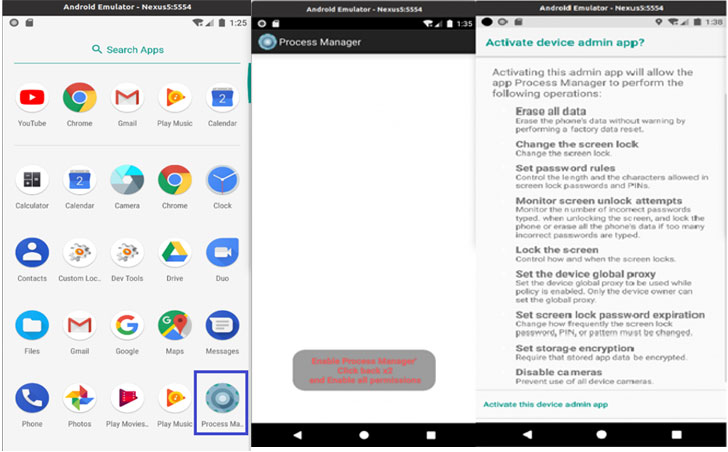
“When the application is operate, a warning appears about the permissions granted to the application,” Lab52 researchers stated. “These consist of monitor unlock makes an attempt, lock the display, established the product worldwide proxy, set display screen lock password expiration, set storage encryption and disable cameras.”
After the app is “activated,” the malware eliminates its gear-formed icon from the residence screen and operates in the track record, abusing its large permissions to accessibility the device’s contacts and call logs, observe its place, send and examine messages, accessibility exterior storage, snap shots, and document audio.
The gathered information is captured in a JSON format and subsequently transmitted to the aforementioned remote server. In spite of the overlap in the C2 server utilized, Lab52 explained it does not have enough proof to attribute the malware to the Turla group.
Also mysterious at this stage is the specific original obtain vector employed for distributing the adware and intended targets of the campaign.
That said, the rogue Android app also attempts to down load a reputable application called Roz Dhan (that means “Every day Prosperity” in Hindi) that has above 10 million installations and permits people to receive money benefits for completing surveys and questionnaires.
“The application, [which] is on Google Participate in and is utilized to get paid income, has a referral method that is abused by the malware,” the researchers reported. “The attacker installs it on the unit and makes a earnings.”
Identified this short article appealing? Abide by THN on Facebook, Twitter and LinkedIn to read far more distinctive written content we put up.
Some parts of this article are sourced from:
thehackernews.com



