An analysis of a nascent ransomware strain called RansomHub has revealed it to be an updated and rebranded version of Knight ransomware, itself an evolution of another ransomware known as Cyclops.
Knight (aka Cyclops 2.0) ransomware first arrived in May 2023, employing double extortion tactics to steal and encrypt victims’ data for financial gain. It’s operational across multiple platforms, including Windows, Linux, macOS, ESXi, and Android.
Advertised and sold on the RAMP cybercrime forum, attacks involving the ransomware have been found to leverage phishing and spear-phishing campaigns as a distribution vector in the form of malicious attachments.
The ransomware-as-a-service (RaaS) operation has since shut down as of late February 2024, when its source code was put up for sale, raising the possibility that it may have changed hands to a different actor, who subsequently decided to update and relaunch it under the RansomHub brand.
RansomHub, which posted its first victim that same month, has been linked to a series of ransomware attacks in recent weeks, counting that of Change Healthcare, Christie’s, and Frontier Communications. It has also vowed to refrain from targeting entities in the Commonwealth of Independent States (CIS) countries, Cuba, North Korea, and China.

“Both payloads are written in Go and most variants of each family are obfuscated with Gobfuscate,” Symantec, part of Broadcom, said in a report shared with The Hacker News. “The degree of code overlap between the two families is significant, making it very difficult to differentiate between them.”
Both share identical help menus on the command-line, with RansomHub adding a new “sleep” option that makes it dormant for a specified time period (in minutes) before execution. Similar sleep commands have been observed in Chaos/Yashma and Trigona ransomware families.
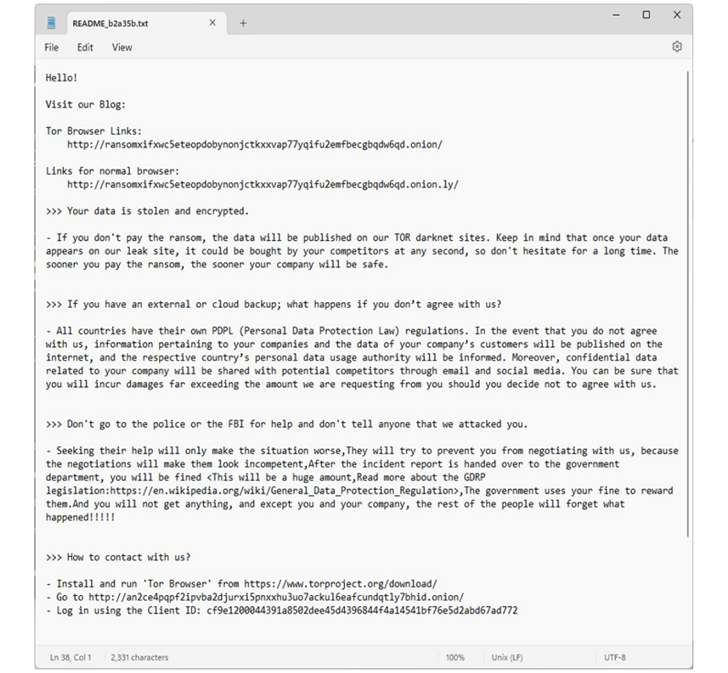
The overlaps between Knight and RansomHub also extend to the obfuscation technique used to encode strings, the ransom notes dropped after encrypting files, and their ability to restart a host in safe mode before starting encryption.
The only main difference is the set of commands executed via cmd.exe, although the “way and order in which they are called relative to other operations is the same,” Symantec said.
RansomHub attacks have been observed leveraging known security flaws (e.g., ZeroLogon) to obtain initial access and drop remote desktop software such as Atera and Splashtop prior to ransomware deployment.
According to statistics shared by Malwarebytes, the ransomware family has been linked to 26 confirmed attacks in the month of April 2024 alone, putting it behind Play, Hunters International, Black Basta, and LockBit.
Google-owned Mandiant, in a report published this week, revealed that RansomHub is attempting to recruit affiliates that have been impacted by recent shutdowns or exit scams such as that of LockBit and BlackCat.
“One former Noberus affiliate known as Notchy is now reportedly working with RansomHub,” Symantec said In addition to this, tools previously associated with another Noberus affiliate known as Scattered Spider, were used in a recent RansomHub attack.
“The speed at which RansomHub has established its business suggests that the group may consist of veteran operators with experience and contacts in the cyber underground.”
The development comes amid an increase in ransomware activity in 2023 compared to a “slight dip” in 2022, even as approximately one-third of 50 new families observed in the year have been found to be variants of previously identified ransomware families, indicating the increasing prevalence of code reuse, actor overlaps, and rebrands.
“In almost one third of incidents, ransomware was deployed within 48 hours of initial attacker access,” Mandiant researchers said. “Seventy-six percent (76%) of ransomware deployments took place outside of work hours, with the majority occurring in the early morning.”

These attacks are also characterized by the use of commercially available and legitimate remote desktop tools to facilitate the intrusion operations as opposed to relying on Cobalt Strike.
“The observed increasing reliance on legitimate tools likely reflects efforts by attackers to conceal their operations from detection mechanisms and reduce the time and resources required to develop and maintain custom tools,” Mandiant said.
The rebound in ransomware attacks follows the emergence of new ransomware variants like BlackSuit, Fog, and ShrinkLocker, the latter of which has been observed deploying a Visual Basic Script (VBScript) that takes advantage of Microsoft’s native BitLocker utility for unauthorized file encryption in extortion attacks targeting Mexico, Indonesia, and Jordan.
ShrinkLocker is so named for its ability to create a new boot partition by shrinking the size of each available non-boot partition by 100 MB, turning the unallocated space into a new primary partition, and using it to reinstall the boot files in order to enable recovery.
“This threat actor has an extensive understanding of the VBScript language, and Windows internals and utilities, such as WMI, diskpart, and bcdboot,” Kaspersky said in its analysis of ShrinkLocker, noting that they likely “already had full control of the target system when the script was executed.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com


 Zyxel Releases Patches for Firmware Vulnerabilities in EoL NAS Models
Zyxel Releases Patches for Firmware Vulnerabilities in EoL NAS Models