Menace actors are utilizing a formerly undocumented “defense evasion device” dubbed AuKill that is built to disable endpoint detection and reaction (EDR) software program by implies of a Bring Your Possess Vulnerable Driver (BYOVD) attack.
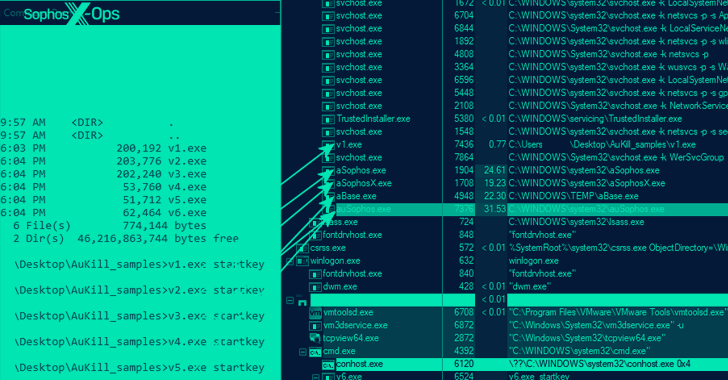
“The AuKill resource abuses an outdated variation of the driver made use of by edition 16.32 of the Microsoft utility, Procedure Explorer, to disable EDR processes ahead of deploying either a backdoor or ransomware on the focus on technique,” Sophos researcher Andreas Klopsch stated in a report revealed last week.
Incidents analyzed by the cybersecurity organization demonstrate the use of AuKill due to the fact the commence of 2023 to deploy a variety of ransomware strains this sort of as Medusa Locker and LockBit. Six different versions of the malware have been discovered to date. The oldest AuKill sample characteristics a November 2022 compilation timestamp.
The BYOVD procedure depends on danger actors misusing a authentic, but out-of-day and exploitable, driver signed by Microsoft (or making use of a stolen or leaked certification) to get elevated privileges and switch off security mechanisms.
By making use of authentic, exploitable motorists, the idea is to bypass a important Windows safeguard recognized as Driver Signature Enforcement that assures kernel-manner drivers have been signed by a legitimate code signing authority prior to they are authorized to operate.
“The AuKill software demands administrative privileges to get the job done, but it can not give the attacker those privileges,” Sophos scientists observed. “The threat actors using AuKill took edge of present privileges throughout the assaults, when they obtained them through other means.”
This is not the very first time the Microsoft-signed Approach Explorer driver has been weaponized in attacks. In November 2022, Sophos also specific LockBit affiliates’ use of an open up resource instrument referred to as Backstab that abused outdated versions of the driver to terminate safeguarded anti-malware procedures.
Then before this calendar year, a malvertising marketing campaign was noticed utilizing the very same driver to distribute a .NET loader named MalVirt to deploy the FormBook info-stealing malware.
The improvement arrives as the AhnLab Security Unexpected emergency reaction Centre (ASEC) uncovered that inadequately managed MS-SQL servers are remaining weaponized to set up the Trigona ransomware, which shares overlaps with yet another pressure referred to as CryLock.
It also follows findings that the Engage in ransomware (aka PlayCrypt) actors have been noticed employing customized details harvesting applications that make it possible to enumerate all end users and personal computers on a compromised network and duplicate data files from the Volume Shadow Duplicate Company (VSS).
Grixba, a .NET-dependent data stealer, is intended to scan a machine for security programs, backup program, and distant administration resources, and exfiltrate the gathered knowledge in the form of CSV data files that are then compressed into ZIP archives.
Also utilised by the cybercriminal gang, tracked by Symantec as Balloonfly, is a VSS Copying Instrument prepared in .NET that can make use of the AlphaVSS framework to listing information and folders in a VSS snapshot and duplicate them to a destination directory prior to encryption.
Impending WEBINARZero Have faith in + Deception: Find out How to Outsmart Attackers!
Find out how Deception can detect innovative threats, cease lateral movement, and greatly enhance your Zero Believe in approach. Sign up for our insightful webinar!
Help save My Seat!
Play ransomware is notable for not only using intermittent encryption to velocity up the course of action, but also for the truth that it is really not operated on a ransomware-as-a-service (RaaS) design. Proof collected so considerably factors to Balloonfly carrying out the ransomware attacks as perfectly as creating the malware on their own.
Grixba and VSS Copying Software are the newest in a extensive list of proprietary equipment such as Exmatter, Exbyte, and PowerShell-based mostly scripts that are utilized by ransomware actors to set up a lot more handle over their operations, whilst also including additional levels of complexity to persist in compromised environments and evade detection.
A further strategy significantly adopted by fiscally-inspired groups is the use of the Go programming language to develop cross-system malware and resist examination and reverse engineering efforts.
Without a doubt, a report from Cyble last week documented a new GoLang ransomware identified as CrossLock that employs the double-extortion technique to increase the likelihood of payment from its victims, along with having methods to sidestep event tracing for Windows (ETW).
“This performance can allow the malware to avoid detection by security programs that rely on function logs,” Cyble mentioned. “CrossLock Ransomware also performs quite a few actions to decrease the likelihood of knowledge recovery though concurrently growing the attack’s usefulness.”
Observed this report attention-grabbing? Comply with us on Twitter and LinkedIn to read through more unique material we article.
Some parts of this article are sourced from:
thehackernews.com

 Study: 84% of Companies Use Breached SaaS Applications – Here’s How to Fix it for Free!
Study: 84% of Companies Use Breached SaaS Applications – Here’s How to Fix it for Free!