Telecommunication vendors in the Center East are the topic of new cyber attacks that commenced in the 1st quarter of 2023.
The intrusion established has been attributed to a Chinese cyber espionage actor involved with a long-running marketing campaign dubbed Procedure Soft Mobile based on tooling overlaps.
“The first attack stage involves infiltrating Internet-struggling with Microsoft Trade servers to deploy web shells utilized for command execution,” scientists from SentinelOne and QGroup said in a new technological report shared with The Hacker News.
“The moment a foothold is proven, the attackers conduct a range of reconnaissance, credential theft, lateral movement, and info exfiltration actions.”
Procedure Gentle Cell, according to Cybereason, refers to destructive things to do undertaken by China-affiliated actors targeting telecommunications companies considering that at the very least 2012.
The Tender Cell danger actor, also tracked by Microsoft as Gallium, is recognised to concentrate on unpatched internet-struggling with products and services and use resources like Mimikatz to receive qualifications that makes it possible for for lateral movement throughout the targeted networks.
Also put to use by the adversarial collective is a “hard-to-detect” backdoor codenamed PingPull in its espionage attacks directed in opposition to businesses functioning in Southeast Asia, Europe, Africa, and the Center East.
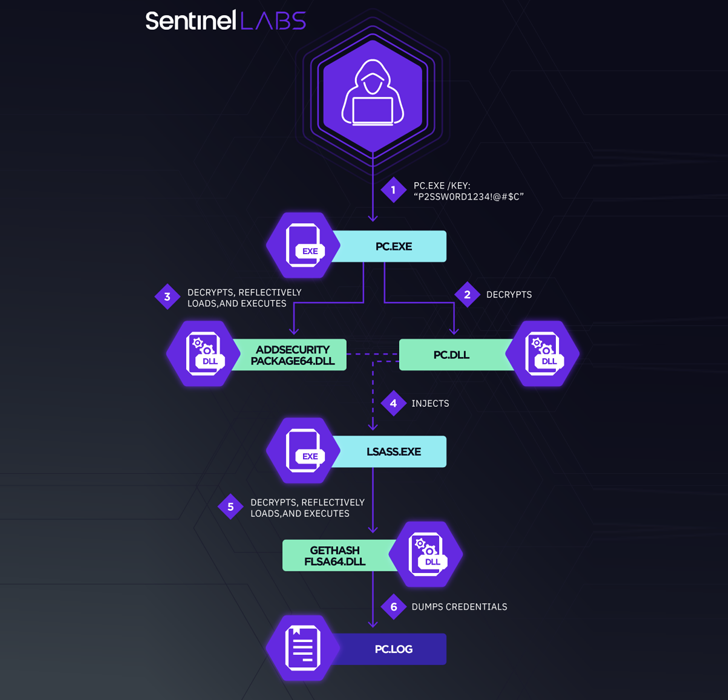
Central to the most current marketing campaign is the deployment of a customized variant of Mimikatz referred to as mim221, which packs in new anti-detection options.
“The use of distinctive-purpose modules that employ a variety of state-of-the-art approaches demonstrates the threat actors’ devotion to advancing its toolset to highest stealth,” the researchers explained, introducing it “highlights the continuous routine maintenance and even further improvement of the Chinese espionage malware arsenal.”
Prior analysis into Gallium implies tactical similarities [PDF] with a number of Chinese nation-condition groups these as APT10 (aka Bronze Riverside, Potassium, or Stone Panda), APT27 (aka Bronze Union, Emissary Panda, or Lucky Mouse), and APT41 (aka Barium, Bronze Atlas, or Wicked Panda).
WEBINARDiscover the Hidden Hazards of Third-Social gathering SaaS Apps
Are you conscious of the threats affiliated with third-celebration app entry to your firm’s SaaS applications? Be part of our webinar to understand about the types of permissions remaining granted and how to minimize risk.
RESERVE YOUR SEAT
This once all over again points to signals of closed-resource software-sharing amongst Chinese condition-sponsored risk actors, not to mention the risk of a “electronic quartermaster” accountable for protecting and distributing the toolset.
The findings arrive amid revelations that different other hacking groups, including BackdoorDiplomacy and WIP26, have set their sights on telecom provider providers in the Middle East region.
“Chinese cyber espionage menace actors are identified to have a strategic curiosity in the Middle East,” the scientists concluded.
“These threat actors will almost unquestionably carry on exploring and upgrading their resources with new methods for evading detection, including integrating and modifying publicly available code.”
Uncovered this short article fascinating? Comply with us on Twitter and LinkedIn to read additional special information we article.
Some parts of this article are sourced from:
thehackernews.com


 Like users, app developers are fleeing Twitter for Mastodon
Like users, app developers are fleeing Twitter for Mastodon