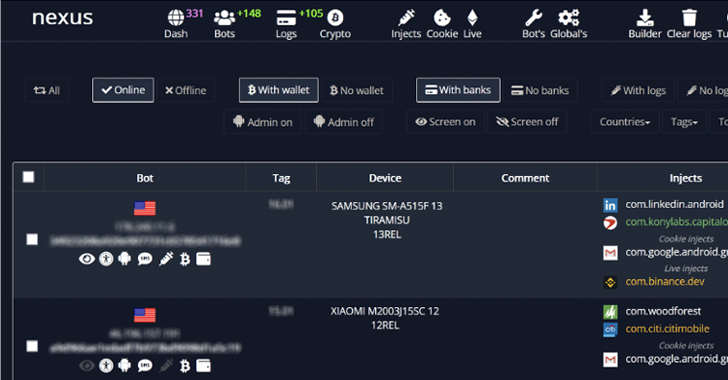
An rising Android banking trojan dubbed Nexus has previously been adopted by various threat actors to goal 450 fiscal apps and conduct fraud.
“Nexus appears to be in its early phases of development,” Italian cybersecurity business Cleafy mentioned in a report released this 7 days.
“Nexus supplies all the key attributes to accomplish ATO attacks (Account Takeover) from banking portals and cryptocurrency providers, these types of as qualifications stealing and SMS interception.”
The trojan, which appeared in a variety of hacking community forums at the start out of the yr, is advertised as a subscription assistance to its clientele for a month-to-month price of $3,000. Particulars of the malware were being to start with documented by Cyble before this thirty day period.
On the other hand, there are indications that the malware could have been utilised in real-planet assaults as early as June 2022, at minimum six months just before its official announcement on darknet portals.
It is also stated to overlap with an additional banking trojan dubbed SOVA, reusing pieces of its resource code and incorporating a ransomware module that appears to be below energetic enhancement.
A issue worthy of mentioning right here is that Nexus is the identical malware that Cleafy in the beginning categorized as a new variant of SOVA (dubbed v5) in August 2022.

Apparently, the Nexus authors have laid out specific rules that prohibit the use of its malware in Azerbaijan, Armenia, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Russia, Tajikistan, Uzbekistan, Ukraine, and Indonesia.
The malware, like other banking trojans, is made up of functions to take in excess of accounts associated to banking and cryptocurrency providers by doing overlay attacks and keylogging to steal users’ credentials.
WEBINARDiscover the Hidden Hazards of Third-Celebration SaaS Applications
Are you informed of the hazards associated with 3rd-celebration app accessibility to your company’s SaaS applications? Sign up for our webinar to find out about the varieties of permissions being granted and how to reduce risk.
RESERVE YOUR SEAT
On top of that, it really is able of examining two-variable authentication (2FA) codes from SMS messages and the Google Authenticator app by way of the abuse of Android’s accessibility solutions.
Some new additions to the checklist of functionalities is its capability to take away been given SMS messages, activate or prevent the 2FA stealer module, and update itself by periodically pinging a command-and-control (C2) server.
“The [Malware-as-a-Service] model will allow criminals to monetize their malware a lot more effectively by supplying a all set-designed infrastructure to their shoppers, who can then use the malware to attack their targets,” the researchers mentioned.
Discovered this posting intriguing? Adhere to us on Twitter and LinkedIn to read more special information we submit.
Some parts of this article are sourced from:
thehackernews.com

 Malicious ChatGPT Chrome Extension Hijacks Facebook Accounts
Malicious ChatGPT Chrome Extension Hijacks Facebook Accounts