A “by-structure flaw” uncovered in Microsoft Azure could be exploited by attackers to obtain accessibility to storage accounts, move laterally in the setting, and even execute distant code.
“It is possible to abuse and leverage Microsoft Storage Accounts by manipulating Azure Features to steal obtain-tokens of greater privilege identities, go laterally, possibly accessibility critical company property, and execute distant code (RCE),” Orca stated in a new report shared with The Hacker News.
The exploitation path that underpins this attack is a mechanism termed Shared Crucial authorization, which is enabled by default on storage accounts.
According to Microsoft, Azure generates two 512-little bit storage account entry keys when making a storage account. These keys can be made use of to authorize entry to details through Shared Crucial authorization, or by using SAS tokens that are signed with the shared key.
“Storage account access keys supply full access to the configuration of a storage account, as well as the info,” Microsoft notes in its documentation. “Accessibility to the shared critical grants a consumer complete accessibility to a storage account’s configuration and its knowledge.”
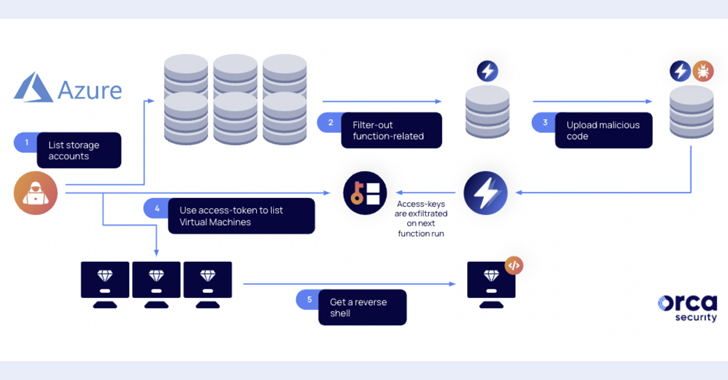
The cloud security organization said these obtain tokens can be stolen by manipulating Azure Features, perhaps enabling a threat actor with access to an account with Storage Account Contributor function to escalate privileges and just take over units.
Especially, ought to a managed id be applied to invoke the Purpose app, it could be abused to execute any command. This, in convert, is designed probable owing to the truth that a dedicated storage account is created when deploying an Azure Perform application.
“After an attacker locates the storage account of a Perform application that is assigned with a sturdy managed identification, it can operate code on its behalf and as a result get a membership privilege escalation (PE),” Orca researcher Roi Nisimi said.
Future WEBINARLearn to Safe the Identity Perimeter – Confirmed Strategies
Enhance your organization security with our upcoming professional-led cybersecurity webinar: Explore Identity Perimeter methods!
Really don’t Skip Out – Preserve Your Seat!
In other text, by exfiltrating the access-token of the Azure Perform app’s assigned managed identification to a distant server, a risk actor can elevate privileges, shift laterally, obtain new assets, and execute a reverse shell on digital machines.
“By overriding perform files in storage accounts, an attacker can steal and exfiltrate a better-privileged id and use it to shift laterally, exploit and compromise victims’ most beneficial crown jewels,” Nisimi stated.
As mitigations, it can be advised that companies contemplate disabling Azure Shared Key authorization and making use of Azure Energetic Listing authentication as an alternative. In a coordinated disclosure, Microsoft mentioned it “plans to update how Features consumer equipment operate with storage accounts.”
“This incorporates modifications to better assist eventualities utilizing identification. Soon after identity-primarily based connections for AzureWebJobsStorage are generally offered and the new encounters are validated, identity will turn into the default manner for AzureWebJobsStorage, which is meant to move away from shared important authorization,” the tech big even further additional.
The findings get there months just after Microsoft patched a misconfiguration issue impacting Azure Lively Listing that created it doable to tamper with Bing lookup effects and a mirrored XSS vulnerability in Azure Service Cloth Explorer (SFX) that could lead to unauthenticated remote code execution.
Located this write-up appealing? Abide by us on Twitter and LinkedIn to browse extra exclusive material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Latitude Financial Refuses to Pay Ransom
Latitude Financial Refuses to Pay Ransom