A novel credential-stealing malware termed Zaraza bot is staying presented for sale on Telegram even though also making use of the preferred messaging support as a command-and-regulate (C2).
“Zaraza bot targets a huge amount of web browsers and is being actively dispersed on a Russian Telegram hacker channel preferred with threat actors,” cybersecurity business Uptycs explained in a report published previous week.
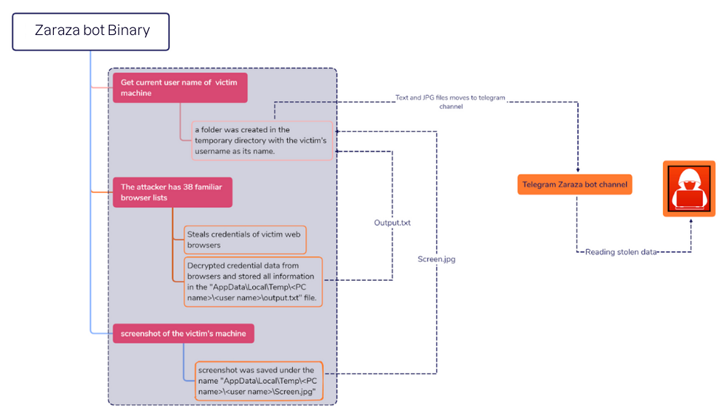
“At the time the malware infects a victim’s computer, it retrieves delicate information and sends it to a Telegram server the place the attackers can obtain it immediately.”
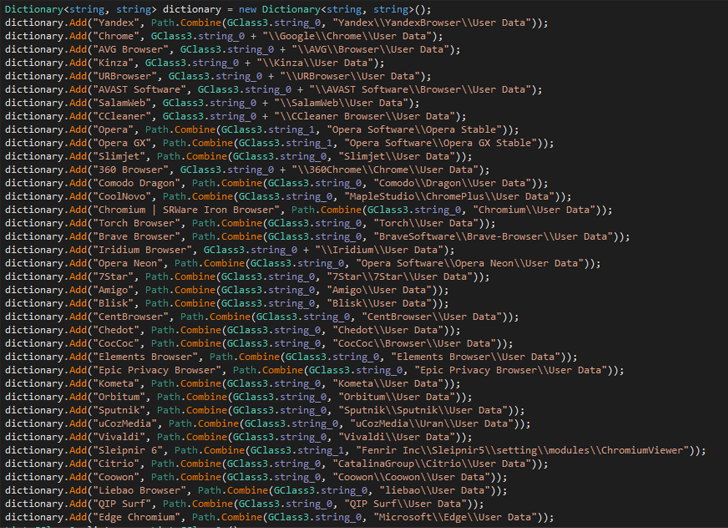
A 64-little bit binary file compiled employing C#, Zaraza bot is created to focus on as lots of as 38 unique web browsers, such as Google Chrome, Microsoft Edge, Opera, AVG Browser, Courageous, Vivaldi, and Yandex. It is really also outfitted to capture screenshots of the active window.
It truly is the most recent example of malware that is able of capturing login credentials connected with online bank accounts, cryptocurrency wallets, email accounts, and other web sites considered of value to the operators.
Stolen qualifications pose a major risk as they not only allow for danger actors to attain unauthorized access to victims’ accounts, but also conduct identity theft and economical fraud.
Evidence gathered by Uptycs factors to Zaraza bot staying available as a professional tool for other cybercriminals for a membership. It’s at present not crystal clear how the malware is propagated, but details stealers have commonly leveraged many strategies these as malvertising and social engineering in the previous.
The findings come as eSentire’s Danger Reaction Unit (TRU) disclosed a GuLoader (aka CloudEyE) campaign concentrating on the economic sector by means of phishing emails by using tax-themed lures to deliver information stealers and remote entry trojans (RATs) like Remcos RAT.
Forthcoming WEBINARMaster the Artwork of Dark Web Intelligence Gathering
Master the art of extracting menace intelligence from the dark web – Be part of this qualified-led webinar!
Save My Seat!
The growth also follows a spike in malvertising and research motor poisoning tactics to distribute a increasing amount of malware households by engaging people browsing for authentic apps into downloading pretend installers that contains stealer payloads.
Russian cybersecurity business Kaspersky, in a new examination, exposed the use of trojanized cracked software program downloaded from BitTorrent or OneDrive to deploy CueMiner, a .NET-dependent downloader that functions as a conduit to installer a cryptocurrency miner known as SilentCryptoMiner.
To mitigate hazards stemming from stealer malware, it really is proposed that users empower two-variable authentication (2FA) and implement software and operating devices updates as and when they grow to be readily available.
Identified this post appealing? Follow us on Twitter and LinkedIn to study extra exclusive material we put up.
Some parts of this article are sourced from:
thehackernews.com


 It’s all in the wrist: Energy-efficient robot hand learns how not to drop the ball
It’s all in the wrist: Energy-efficient robot hand learns how not to drop the ball