Chromium-based web browsers are the goal of a new malware identified as Rilide that masquerades alone as a seemingly authentic extension to harvest sensitive data and siphon cryptocurrency.
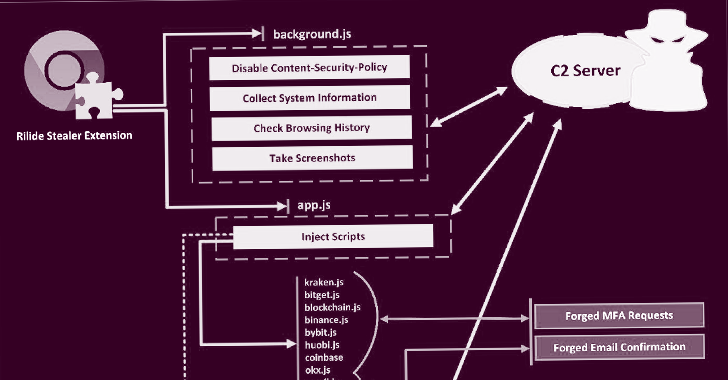
“Rilide malware is disguised as a legitimate Google Drive extension and enables menace actors to have out a wide spectrum of malicious pursuits, which includes checking
browsing background, using screenshots, and injecting malicious scripts to withdraw funds from numerous cryptocurrency exchanges,” Trustwave SpiderLabs Research claimed in a report shared with The Hacker Information.
What is actually additional, the stealer malware can exhibit cast dialogs to deceive buyers into entering a two-issue authentication code to withdraw digital belongings.
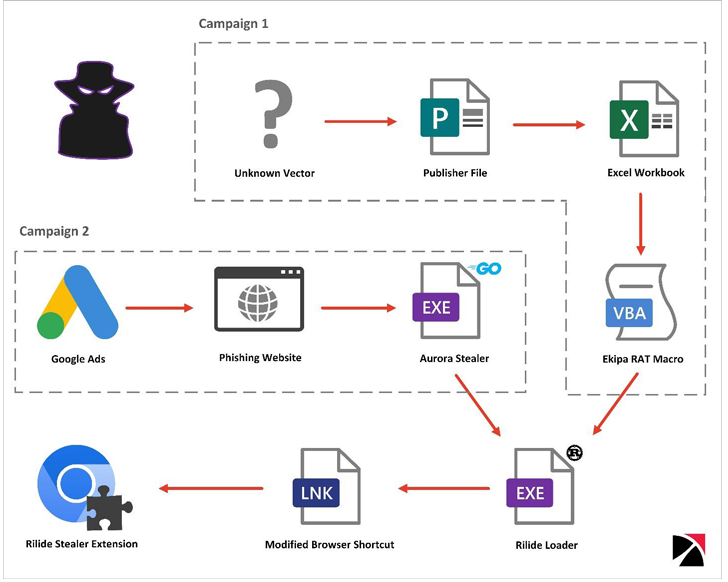
Trustwave reported it discovered two distinct strategies involving Ekipa RAT and Aurora Stealer that led to the set up of the malicious browser extension.
While Ekipa RAT is dispersed by means of booby-trapped Microsoft Publisher documents, rogue Google Ads act as the delivery vector for Aurora Stealer – a method that’s come to be more and more common in recent months.
Each the attack chains aid the execution of a Rust-based loader that, in switch, modifies the browser’s LNK shortcut file and tends to make use of the “–load-extension” command line change to start the include-on.
The actual origins of Rilide is mysterious, but Trustwave explained it was capable to uncover an underground discussion board publish designed in March 2022 by a threat actor marketing the sale of a botnet with similar functionalities.
A part of the malware’s source code has since found its way to the message boards following what seems to be an unresolved payment dispute.
THN WEBINARBecome an Incident Response Pro!
Unlock the techniques to bulletproof incident reaction – Master the 6-Section course of action with Asaf Perlman, Cynet’s IR Leader!
Never Miss Out – Help save Your Seat!
Just one notable function carried out in the leaked supply code is the ability to swap cryptocurrency wallet addresses in the clipboard with an actor-controlled address hard-coded in the sample.
On top of that, a command-and-handle (C2) address specified in the Rilide code has manufactured it achievable to discover different GitHub repositories belonging to a person named gulantin that have loaders for the extension.
“The Rilide stealer is a prime instance of the escalating sophistication of destructive browser extensions and the hazards they pose,” Trustwave concluded.
“Although the upcoming enforcement of manifest v3 may possibly make it extra challenging for risk actors to run, it is unlikely to resolve the issue solely as most of the functionalities leveraged by Rilide will continue to be offered.”
Observed this write-up fascinating? Follow us on Twitter and LinkedIn to browse much more distinctive content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Crypto Firms Are Likely Target for 3CX Attacks
Crypto Firms Are Likely Target for 3CX Attacks