Banking and logistics industries are underneath the onslaught of a reworked variant of a malware identified as Chaes.
“It has undergone significant overhauls: from remaining rewritten completely in Python, which resulted in lower detection rates by conventional protection programs, to a extensive redesign and an enhanced interaction protocol,” Morphisec reported in a new comprehensive complex create-up shared with The Hacker News.
Chaes, which first emerged in 2020, is recognized to focus on e-commerce shoppers in Latin The us, specially Brazil, to steal delicate financial info.
A subsequent evaluation from Avast in early 2022 observed that the risk actors powering the operation, who get in touch with by themselves Lucifer, experienced breached a lot more than 800 WordPress web-sites to produce Chaes to consumers of Banco do Brasil, Loja Integrada, Mercado Bitcoin, Mercado Livre, and Mercado Pago.
Further updates had been detected in December 2022, when Brazilian cybersecurity business Tempest Security Intelligence uncovered the malware’s use of Windows Administration Instrumentation (WMI) in its infection chain to aid the collection of method metadata, such as BIOS, processor, disk dimensions, and memory data.

The most up-to-date iteration of the malware, dubbed Chae$ 4 in reference to debug log messages current in the supply code, packs in “significant transformations and enhancements,” including an expanded catalog of expert services targeted for credential theft as perfectly as clipper functionalities.
Inspite of the changes in the malware architecture, the all round supply mechanism has remained the same in attacks that were discovered in January 2023.
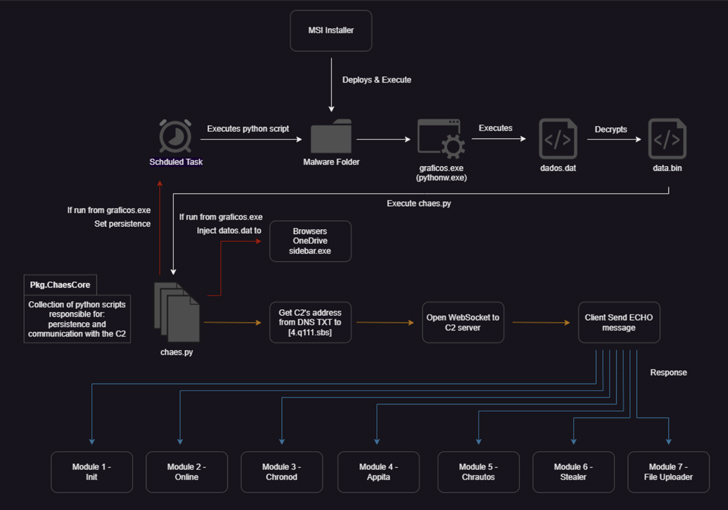
Potential victims landing on one particular of the compromised internet sites are greeted by a pop-up information asking them to down load an installer for Java Runtime or an antivirus solution, triggering the deployment of a destructive MSI file that, in flip, launches a primary orchestrator module recognised as ChaesCore.
The element is accountable for creating a interaction channel with the command-and-manage (C2) server from where it fetches extra modules that guidance article-compromise action and details theft –
- Init, which gathers comprehensive data about the system
- Online, which acts as a beacon to transmit a concept back again to the attacker that the malware is operating on the device
- Chronod, which steals login qualifications entered in web browsers and intercept BTC, ETH, and PIX payment transfers
- Appita, a module with similar features as that of Chronod but specifically developed to target Itaú Unibanco’s desktop application (“itauaplicativo.exe”)
- Chrautos, an up-to-date version of Chronod and Appita that focuses on gathering info from Mercado Libre, Mercado Pago, and WhatsApp
- Stealer, an enhanced variant of Chrolog which plunders credit rating card details, cookies, autofill, and other data saved in web browsers, and
- File Uploader, which uploads knowledge relevant to MetaMask’s Chrome extension
Persistence on the host is accomplished by suggests of a scheduled task, when C2 communications entail the use of WebSockets, with the implant managing in an infinite loop to await more guidance from the remote server.
The focusing on of cryptocurrency transfers and fast payments via Brazils’ PIX platform is a noteworthy addition that underscores the menace actors’ economical motivations.
Approaching WEBINARDetect, Respond, Guard: ITDR and SSPM for Entire SaaS Security
Explore how Id Danger Detection & Response (ITDR) identifies and mitigates threats with the support of SSPM. Learn how to protected your company SaaS purposes and safeguard your knowledge, even right after a breach.
Supercharge Your Expertise
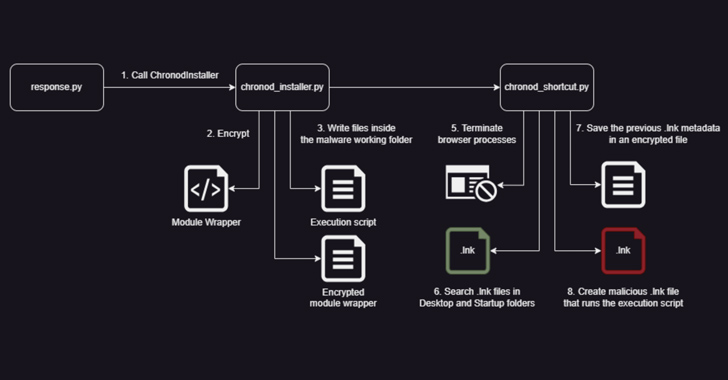
“The Chronod module introduces an additional component employed in the framework, a component referred to as Module Packer,” Morphisec discussed. “This element provides the module its own persistence and migration mechanisms, working considerably like the ChaesCore’s just one.”
This method consists of altering all shortcut documents (LNK) connected with web browsers (e.g., Google Chrome, Microsoft Edge, Brave, and Avast Secure Browser) to execute the Chronod module in its place of the precise browser.
“The malware takes advantage of Google’s DevTools Protocol to hook up to the present browser instance,” the corporation claimed. “This protocol lets direct communication with the inner browser’s performance above WebSockets.”
“The wide range of capabilities exposed by this protocol enables the attacker to run scripts, intercept network requests, read Article bodies right before remaining encrypted, and substantially additional.”
Uncovered this article appealing? Observe us on Twitter and LinkedIn to examine far more exceptional articles we put up.
Some parts of this article are sourced from:
thehackernews.com

 Way Too Vulnerable: Join this Webinar to Understand and Strengthen Identity Attack Surface
Way Too Vulnerable: Join this Webinar to Understand and Strengthen Identity Attack Surface