The North Korea-joined threat actor identified as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been noticed shifting its techniques, leveraging Compiled HTML Help (CHM) data files as vectors to supply malware for harvesting sensitive details.
Kimsuky, energetic due to the fact at least 2012, is identified to goal entities situated in South Korea as effectively as North The usa, Asia, and Europe.
According to Rapid7, attack chains have leveraged weaponized Microsoft Business paperwork, ISO information, and Windows shortcut (LNK) information, with the group also using CHM data files to deploy malware on compromised hosts.
The cybersecurity company has attributed the action to Kimsuky with moderate self confidence, citing very similar tradecraft observed in the earlier.

“Though at first made for aid documentation, CHM files have also been exploited for destructive functions, these types of as distributing malware, due to the fact they can execute JavaScript when opened,” the business said.
The CHM file is propagated in just an ISO, VHD, ZIP, or RAR file, opening which executes a Visible Fundamental Script (VBScript) to established up persistence and attain out to a remote server to fetch a upcoming-stage payload accountable for gathering and exfiltrating sensitive facts.
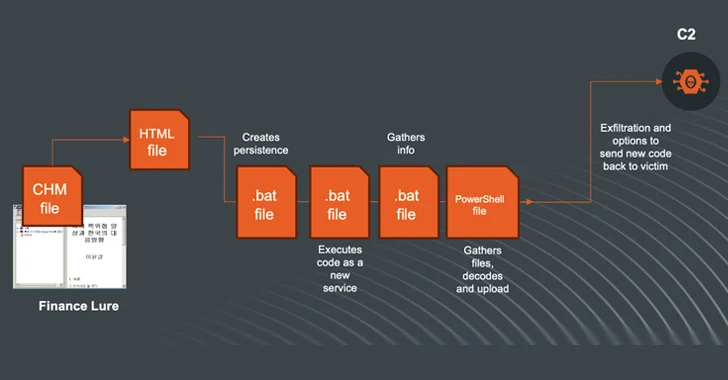
Quick7 explained the attacks as ongoing and evolving, focusing on corporations centered in South Korea. It also determined an alternate infection sequence that employs a CHM file as a commencing point to fall batch files tasked with harvesting the facts and a PowerShell script to hook up to the C2 server and transfer the facts.
“The modus operandi and reusing of code and applications are exhibiting that the menace actor is actively making use of and refining/reshaping its approaches and strategies to assemble intelligence from victims,” it reported.
The progress will come as Broadcom-owned Symantec exposed that the Kimsuky actors are distributing malware impersonating an application from a authentic Korean general public entity.
“At the time compromised, the dropper installs an Endoor backdoor malware,” Symantec explained. “This threat enables attackers to accumulate sensitive data from the sufferer or install additional malware.”
It is really worth noting that the Golang-based Endoor, along with Troll Stealer (aka TrollAgent), has been a short while ago deployed in connection with cyber attacks that goal buyers downloading security packages from a Korean building-connected association’s web-site.

The conclusions also arrive amid a probe initiated by the United Nations into 58 suspected cyber assaults carried out by North Korean country-state actors in between 2017 and 2023 that netted $3 billion in illegal revenues to assistance it further create its nuclear weapons system.
“The higher volume of cyber attacks by hacking groups subordinate to the Reconnaissance Normal Bureau reportedly continued,” the report explained. “Trends include concentrating on protection corporations and offer chains and, increasingly, sharing infrastructure and resources.”
The Reconnaissance Typical Bureau (RGB) is North Korea’s main international intelligence assistance, comprising the danger clusters widely tracked as the Lazarus Group – and its subordinate features, Andariel and BlueNoroff – and Kimsuky.
“Kimsuky has revealed fascination in working with generative artificial intelligence, like significant language designs, most likely for coding or writing phishing e-mails,” the report further more added. “Kimsuky has been noticed applying ChatGPT.”
Observed this report fascinating? Follow us on Twitter and LinkedIn to browse extra exceptional content material we submit.
Some parts of this article are sourced from:
thehackernews.com

 German Police Seize ‘Nemesis Market’ in Major International Darknet Raid
German Police Seize ‘Nemesis Market’ in Major International Darknet Raid