As a vCISO, you are responsible for your client’s cybersecurity strategy and risk governance. This incorporates multiple disciplines, from research to execution to reporting. Recently, we published a comprehensive playbook for vCISOs, “Your First 100 Days as a vCISO – 5 Steps to Success”, which covers all the phases entailed in launching a successful vCISO engagement, along with recommended actions to take, and step-by-step examples.
Following the success of the playbook and the requests that have come in from the MSP/MSSP community, we decided to drill down into specific parts of vCISO reporting and provide more color and examples. In this article, we focus on how to create compelling narratives within a report, which has a significant impact on the overall MSP/MSSP value proposition.
This article brings the highlights of a recent guided workshop we held, covering what makes a successful report and how it can be used to enhance engagement with your cyber security clients.
The workshop was delivered in partnership with Jesse Miller, co-author of the First 100 Days playbook, and founder of PowerPSA Consulting and the PowerGRYD. Jesse is a long-time CISO/vCISO and infosec strategist who has made it his mission to help service providers crack the code for premium vCISO profits. You can watch the entire webinar, with more details and real-world examples here.
The Hidden Value in Reporting
According to Miller, “It’s one thing to do a great job, it’s quite another for your client to see it that way.” This is where reporting should focus. A tight reporting process is the cherry on top of a connected journey for the client in a successful vCISO program.
However, as Miller reveals, reporting is not primarily for the purpose of demonstrating the activities the vCISO performs for the client, which is a common misconception. Rather, the real value lies in making the client the hero of their security journey. Therefore, vCISO reports should focus on the client and their organization’s goals, not the vCISO’s activities. The ultimate goal of any report is to enable a business strategy discussion that revolves around security.
vCISO Reporting Benefits
Drilling down into the aforementioned purpose, vCISO reporting provides multiple benefits for both the vCISO and the client:
For the vCISO –
- Ensuring the vCISO is aligned with client expectations
- Ensuring the client understands their security and compliance posture
- Creating a shared vision between the vCISO and the client
- Build consensus on an improvement path (rather than solely pushing recommendations one-sidedly)
- Anchoring initiatives into business outcomes
- Driving retention and sales
For the client –
- Controlling their security destiny
- Designing their security journey based on business outcomes and allowing them to own the risk associated with their decisions and actions
- Simplified decision-making
- Noise reduction
- Bandwidth and scale
- Getting easy buttons and resources for tactical execution
- Ensuring they perceive the high ROI being provided for their vCISO investment
4 Essential Sections of a vCISO Report
To uncover all the benefits listed above, it is recommended to create a report that covers four sections:
- Section 1: General Recap – The summary, top-level metrics and any “hot stove” items.
- Section 2: Tactical Review – How controls perform, data “stories” and setting the stage for the recommendations and initiatives to come in the following sections.
- Section 3: Strategic Review – A roadmap review, holding a business-led discussion, recommendations and mapping the RCT (Resource, Commitment, Time) for the next steps.
- Section 4: Future Initiatives – Current work in progress, protecting from risk and building up the sales funnel.
Now let’s dive into each one.
Section 1: General Recap
The first section of the report provides an overview and summary, teasers for the rest of the report and high-level metrics. It is also where “hot-stove” items can be addressed. For example, informing about an attacker foothold and answering any open questions.
By providing a brief initial section focused on the outcomes, vCISOs can concisely share the story they are telling. It also allows Executives and Business Leaders to join the first part of the report for an overview, leaving the practitioners to dig into the granular details later on.
For example, in this sample report by Cynomi, we can see the first part of the general recap, showing the posture score, together with a brief explanation about what it means and alluding to the risk.
Section 2: Tactical Review
The second section allows telling stories with the data. Since there’s a wide range of data that can be pulled into the reports, it’s important to ensure the right data is used. This will allow the creating of the right story.
Remember, the idea is to make the client the hero, showing them how they get what they want for the business from their security program.
For example, a highly technical audience can get into the granular details of the security programs. However, a high level decision maker will not be able to understand the story from the same data. Therefore, it’s recommended to automate the gathering of data, and then collate and prune the data for the type of client that’s being presented to.
This section can also show progress and recommendations tailored for various decision makers, security incidents and how to address them, recommended actions to support business processes (like M&As), and more.
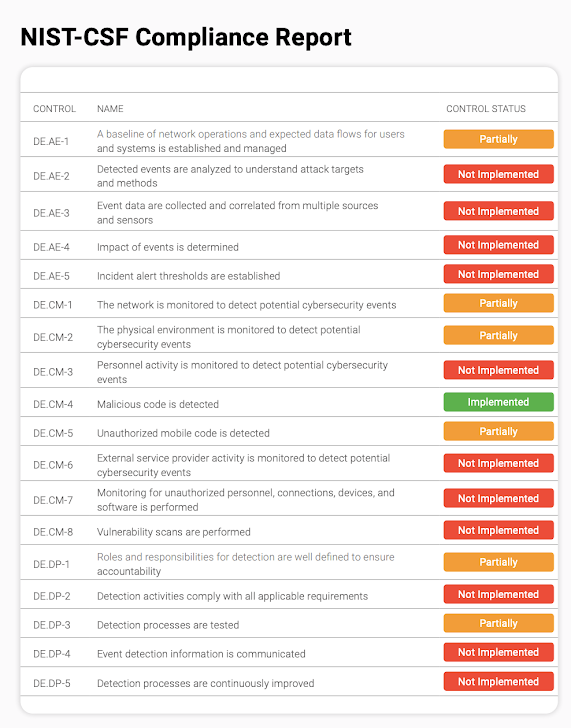
For example, in this section from a sample report by Cynomi, the vCISO can drill down into the status of the various policies and domains that need to be better secured. Later on, the report also shows the scan results that are the evidence for this analysis.

Section 3: Strategic Review
The strategic review section is intended to create a prioritized security journey. To build this story, it’s important to link the risk assessment, the security roadmap and the recommendations. This means creating a system where the high-level risk assessment finds delinquencies in security controls, like vulnerability management, malware control, or incident response. Then, the recommendation report should clearly state which solutions need to be deployed and the roadmap should list priorities, i.e. creating a journey.
Pro tips:
- Don’t spread FUD. Rather, go with a “compliment sandwich” approach, starting and ending with positive feedback.
- Before asking clients to spend money, show them how recommendations and actions save them money and support the business.
- Use the RCT (Resources, Cost, Time) mapping to help clients make a decision.
For example, in this Cynomi report, the vCISO can show the state of meeting compliance and leverage this for the recommendations and roadmap.
Section 4: Future Initiatives
In the end, it’s time to discuss future initiatives. Since clients do not have endless resources, this section helps queue up work and prioritize it based on a business-led consensus.
This section also helps protect both the client and vCISO from risk. For example, showing progress month over month helps show auditors and regulatory bodies the client is performing due care. This protects both the vCISO and the client.
Finally, this section creates accountability among customers. With the vCISO clearly showing the business outcomes of accepting proposed recommendations, the client can make a business decision, and own the risk for that decision.
What’s Next?
Reporting is part of a holistic vCISO approach that creates trust with the client. Making the client the hero shows them you have their best interests at heart. When this is verifed through reporting, it drives vCISO scale and growth, making your business successful.
For more explanations and examples, watch the entire workshop here.
For more pro tips and proven practices for vCISO, read the guide “Your First 100 Days as a vCISO – 5 Steps to Success”.
For daily insights on how to supercharge your vCISO profits, follow Jesse Miller on LinkedIn or join the PowerGRYD community.
Found this article interesting? This article is a contributed piece from one of our valued partners. Follow us on Twitter and LinkedIn to read more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com


 SocGholish Malware Exploits BOINC Project for Covert Cyberattacks
SocGholish Malware Exploits BOINC Project for Covert Cyberattacks