The danger actors behind the ransomware attack on Taiwanese Computer system maker MSI final thirty day period have leaked the firm’s personal code signing keys on their dark web page.
“Verified, Intel OEM personal vital leaked, leading to an effect on the total ecosystem,” Alex Matrosov, founder and CEO of firmware security business Binarly, mentioned in a tweet more than the weekend.
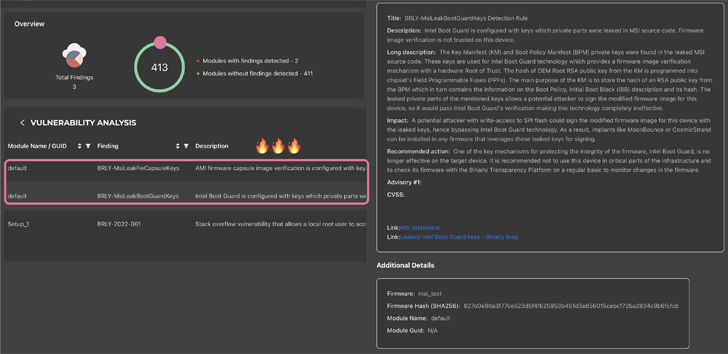
“It appears that Intel Boot Guard may possibly not be powerful on selected gadgets dependent on the 11th Tiger Lake, 12th Adler Lake, and 13th Raptor Lake.”

Current in the leaked details are firmware impression signing keys linked with 57 PCs and private signing keys for Intel Boot Guard made use of on 116 MSI solutions. The Boot Guard keys from MSI are thought to effects quite a few device suppliers, including Intel, Lenovo and Supermicro.
Intel Boot Guard is a hardware-primarily based security technology that is built to secure computers towards executing tampered UEFI firmware.
The development will come a thirty day period soon after MSI fell target to a double extortion ransomware attack perpetrated by a new ransomware gang known as Dollars Message.
MSI, in a regulatory submitting at the time, reported, “the impacted methods have progressively resumed normal operations, with no sizeable affect on monetary organization.” It, nonetheless, urged consumers to get hold of firmware/BIOS updates only from its formal internet site and chorus from downloading files from other resources.
The leak of the keys poses major hazards as threat actors could use them to sign destructive updates and other payloads and deploy them on qualified techniques devoid of elevating any purple flags.
Future WEBINARLearn to Prevent Ransomware with True-Time Security
Be part of our webinar and master how to halt ransomware assaults in their tracks with genuine-time MFA and services account defense.
Help you save My Seat!
It also follows a further advisory from MSI recommending customers to be on the lookout for fraudulent e-mail targeting the on the internet gaming neighborhood that promises to be from the organization beneath the pretext of a opportunity collaboration.
This is not the initially time UEFI firmware code has entered the general public area. In October 2022, Intel acknowledged the leak of Alder Lake BIOS supply code by a third social gathering, which also involved the non-public signing crucial applied for Boot Guard.
Found this article appealing? Comply with us on Twitter and LinkedIn to read extra exceptional content material we post.
Some parts of this article are sourced from:
thehackernews.com


 Western Digital Confirms Customer Data Stolen by Hackers in March Breach
Western Digital Confirms Customer Data Stolen by Hackers in March Breach