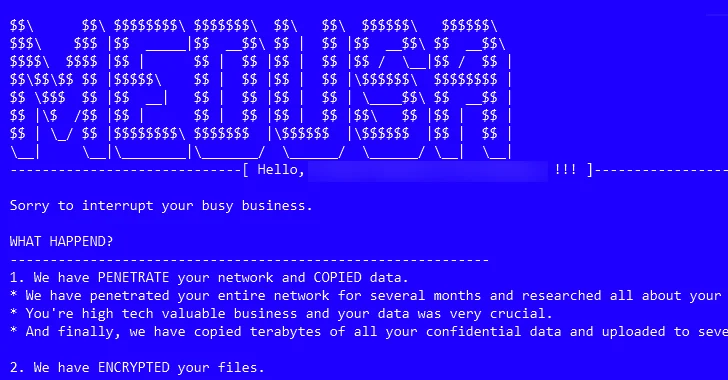
The risk actors connected with the Medusa ransomware have ramped up their things to do adhering to the debut of a focused data leak web site on the dark web in February 2023 to publish sensitive information of victims who are unwilling to concur to their needs.
“As aspect of their multi-extortion approach, this team will supply victims with multiple possibilities when their info is posted on their leak site, these as time extension, information deletion or obtain of all the facts,” Palo Alto Networks Unit 42 scientists Anthony Galiette and Doel Santos said in a report shared with The Hacker News.
“All of these options have a selling price tag based on the organization impacted by this group.”
Medusa (not to be perplexed with Medusa Locker) refers to a ransomware household that appeared in late 2022 just before coming into prominence in 2023. It is really known for opportunistically targeting a broad array of industries such as large technology, instruction, producing, health care, and retail.
As a lot of as 74 businesses, mostly in the U.S., the U.K., France, Italy, Spain, and India, are estimated to have been impacted by the ransomware in 2023.

Ransomware attacks orchestrated by the group start with the exploitation of internet-facing assets or purposes with identified unpatched vulnerabilities and hijacking of reputable accounts, typically using original entry brokers to acquire a foothold to concentrate on networks.
In 1 instance noticed by the cybersecurity company, a Microsoft Exchange Server was exploited to upload a web shell, which was then utilised as a conduit to put in and execute the ConnectWise remote monitoring and administration (RMM) software package.
A noteworthy aspect of the bacterial infections is the reliance on dwelling-off-the-land (LotL) tactics to blend in with legit action and sidestep detection. Also observed is the use of a pair of kernel motorists to terminate a difficult-coded record of security products and solutions.
The initial obtain phase is followed by discovery and reconnaissance of the compromised network, with the actors in the long run launching the ransomware to enumerate and encrypt all data files preserve for these with the extensions .dll, .exe, .lnk, and .medusa (the extension specified to the encrypted documents).
For each and every compromised sufferer, Medusa’s leak internet site displays details about the corporations, ransom demanded, the volume of time left before the stolen info is introduced publicly, and the selection of views in a bid to exert stress on the organization.

The actors also offer distinctive choices to the sufferer, all of which require some type of extortion to delete or obtain the pilfered data and seek out a time extension to avoid the info from getting released.
As ransomware carries on to be a rampant menace, focusing on tech corporations, health care, critical infrastructure, and anything in between, the menace actors guiding it are having far more brazen with their ways, heading past publicly naming and shaming organizations by resorting to threats of bodily violence and even dedicated public relations channels.
“Ransomware has improved lots of facets of the danger landscape, but a important latest advancement is its increasing commoditization and professionalization,” Sophos scientists mentioned last month, contacting ransomware gangs “significantly media-savvy.”

Medusa, per Device 42, not only has a media crew to probably take care of their branding endeavours, but also leverages a public Telegram channel named “details guidance,” in which files of compromised companies are shared and can be accessed more than the clearnet. The channel was set up in July 2021.
“The emergence of the Medusa ransomware in late 2022 and its notoriety in 2023 marks a major growth in the ransomware landscape,” the researchers reported. “This operation showcases sophisticated propagation methods, leveraging the two program vulnerabilities and original accessibility brokers, when adeptly keeping away from detection via living-off-the-land tactics.”
The improvement arrives as Arctic Wolf Labs publicized two cases in which victims of Akira and Royal ransomware gangs had been targeted by destructive third-events posing as security scientists for secondary extortion makes an attempt.
“Risk actors spun a narrative of trying to help victim organizations, supplying to hack into the server infrastructure of the primary ransomware teams involved to delete exfiltrated details,” security researchers Stefan Hostetler and Steven Campbell claimed, noting the threat actor sought about 5 bitcoin in exchange for the service.
It also follows a new advisory from the Finnish Nationwide Cyber Security Centre (NCSC-FI) about a spike in Akira ransomware incidents in the place towards the conclude of 2023 by exploiting a security flaw in Cisco VPN appliances (CVE-2023-20269, CVSS score: 5.) to breach domestic entities.
Observed this post attention-grabbing? Adhere to us on Twitter and LinkedIn to go through additional unique written content we post.
Some parts of this article are sourced from:
thehackernews.com

 Urgent: GitLab Releases Patch for Critical Vulnerabilities – Update ASAP
Urgent: GitLab Releases Patch for Critical Vulnerabilities – Update ASAP