A new strain of Android malware has been noticed in the wild targeting on-line banking and cryptocurrency wallet shoppers in Spain and Italy, just months just after a coordinated regulation enforcement procedure dismantled FluBot.
The information and facts thieving trojan, codenamed MaliBot by F5 Labs, is as element-prosperous as its counterparts, allowing for it to steal qualifications and cookies, bypass multi-issue authentication (MFA) codes, and abuse Android’s Accessibility Support to observe the victim’s unit display screen.
MaliBot is identified to generally disguise by itself as cryptocurrency mining applications such as Mining X or The CryptoApp that are dispersed via fraudulent web-sites made to draw in opportunity people into downloading them.
It also requires a further leaf out of the cellular banking trojan playbook in that it employs smishing as a distribution vector to proliferate the malware by accessing an infected smartphone’s contacts and sending SMS messages that contains backlinks to the malware.
“MaliBot’s command-and-manage (C2) is in Russia and seems to use the exact same servers that had been applied to distribute the Sality malware,” F5 Labs researcher Dor Nizar claimed. “It is a seriously modified re-working of the SOVA malware, with diverse operation, targets, C2 servers, domains, and packing strategies.”

SOVA (which means “Owl” in Russian), which was very first detected in August 2021, is noteworthy for its skill to conduct overlay attacks, which perform by exhibiting a fraudulent website page using WebView with a url offered by the C2 server should really a target open up a banking application involved in its lively target listing.
Some of the banking companies qualified by MaliBot applying this approach include things like UniCredit, Santander, CaixaBank, and CartaBCC.
Accessibility Company is a track record provider running in Android products to support people with disabilities. It has extensive been leveraged by adware and trojans to seize the system contents and intercept qualifications entered by unsuspecting users on other applications.

Apart from staying capable to siphon passwords and cookies of the victim’s Google account, the malware is designed to swipe 2FA codes from the Google Authenticator app as very well as exfiltrate delicate data these as whole balances and seed phrases from Binance and Have confidence in Wallet apps.
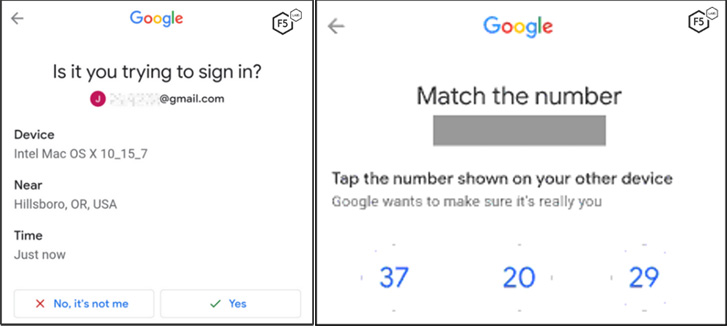
What’s more, Malibot is capable of weaponizing its accessibility to the Accessibility API to defeat Google’s two-variable authentication (2FA) procedures, this sort of as Google prompts, even in scenarios in which an attempt is manufactured to signal in to the accounts making use of the stolen qualifications from a previously not known system.
“The flexibility of the malware and the handle it presents attackers around the system indicate that it could, in principle, be utilised for a broader variety of attacks than stealing credentials and cryptocurrency,” the researchers mentioned.
“In simple fact, any application which tends to make use of WebView is liable to having the users’ qualifications and cookies stolen.”
Found this posting attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to study more exceptional articles we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Critical Flaw in Cisco Secure Email and Web Manager Lets Attackers Bypass Authentication
Critical Flaw in Cisco Secure Email and Web Manager Lets Attackers Bypass Authentication