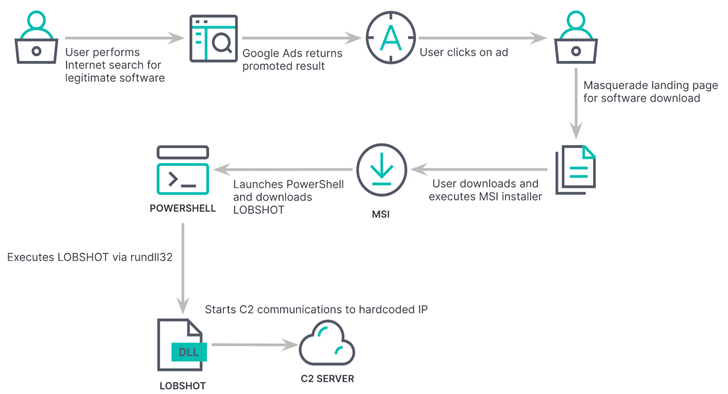
In but a further occasion of how risk actors are abusing Google Advertisements to serve malware, a menace actor has been noticed leveraging the procedure to deliver a new Windows-primarily based financial trojan and information and facts stealer named LOBSHOT.
“LOBSHOT proceeds to obtain victims although remaining underneath the radar,” Elastic Security Labs researcher Daniel Stepanic said in an assessment published last 7 days.
“One of LOBSHOT’s core abilities is all over its hVNC (Concealed Digital Network Computing) element. These forms of modules allow for for direct and unobserved access to the machine.”
The American-Dutch enterprise attributed the malware strain to a menace actor recognised as TA505 primarily based on infrastructure traditionally connected to the group. TA505 is a economically determined e-crime syndicate that overlaps with action clusters tracked underneath the names Evil Corp, FIN11, and Indrik Spider.

The latest improvement is sizeable due to the fact it really is a signal that TA505, which is affiliated with the Dridex banking trojan, is as soon as all over again increasing its malware arsenal to perpetrate info theft and economical fraud.
LOBSHOT, with early samples dating back to July 2022, is distributed by indicates of rogue Google ads for respectable tools like AnyDesk that are hosted on a network of lookalike landing pages maintained by the operators.
The malware incorporates dynamic import resolution (i.e., resolving the names of necessary Windows APIs at runtime), anti-emulation checks, and string obfuscation to evade detection by security computer software.
At the time put in, it helps make Windows Registry improvements to set up persistence and siphons details from around 50 cryptocurrency wallet extensions existing in web browsers like Google Chrome, Microsoft Edge, and Mozilla Firefox.
LOBSHOT’s other noteworthy characteristics revolve about its means to remotely accessibility the compromised host through an hVNC module and stealthily carry out actions on it with no attracting the victim’s notice.
“Threat teams are continuing to leverage malvertising strategies to masquerade authentic software program with backdoors like LOBSHOT,” Stepanic stated.
“These forms of malware seem to be compact, but end up packing considerable performance which assists threat actors transfer promptly throughout the initial access levels with entirely interactive remote command capabilities.”
Impending WEBINARLearn to Prevent Ransomware with Serious-Time Security
Be a part of our webinar and discover how to prevent ransomware attacks in their tracks with serious-time MFA and services account security.
Save My Seat!
The findings also underscore how an growing number of adversaries are adopting malvertising and search motor optimization (Search engine optimisation) poisoning as a system to redirect users to faux internet sites and down load trojanized installers of well-known software package.
In accordance to information from eSentire, the danger actors at the rear of GootLoader have been connected to a string of assaults focusing on law companies and company lawful departments in the U.S., Canada, the U.K., and Australia.
GootLoader, active considering the fact that 2018 and which functions as an preliminary entry-as-a-provider procedure for ransomware assaults, hire Search engine marketing poisoning to entice victims browsing for agreements and contracts to contaminated WordPress blogs that issue to one-way links that contains the malware.
Aside from applying geofencing to target victims in find regions, the attack chain is created such that the malware can only be downloaded after for each working day from the hijacked websites in order to elude discovery by incident responders.
GootLoader’s use of the IP tackle process to display currently hacked victims, eSentire found, could be used against it to preemptively block the finish users’ IP addresses and protect against companies from probable bacterial infections.
Uncovered this write-up fascinating? Observe us on Twitter and LinkedIn to go through additional exceptional information we post.
Some parts of this article are sourced from:
thehackernews.com


 North Korea’s ScarCruft Deploys RokRAT Malware via LNK File Infection Chains
North Korea’s ScarCruft Deploys RokRAT Malware via LNK File Infection Chains