A new backdoor connected with a malware downloader named Wslink has been found out, with the instrument most likely used by the notorious North Korea-aligned Lazarus Group, new conclusions reveal.
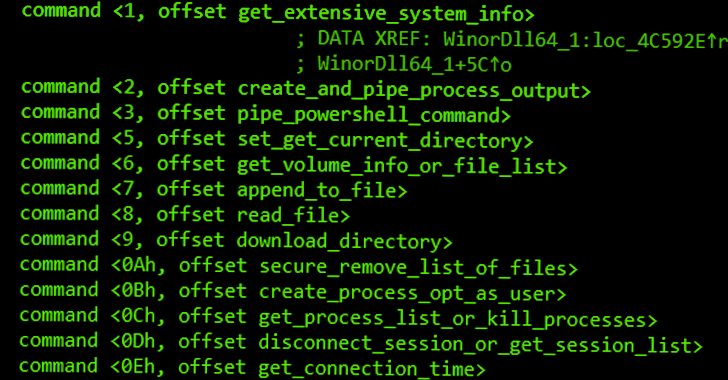
The payload, dubbed WinorDLL64 by ESET, is a thoroughly-showcased implant that can exfiltrate, overwrite, and delete documents execute PowerShell instructions and get extensive details about the underlying equipment.
Its other functions comprise listing lively periods, generating and terminating procedures, enumerating drives, and compressing directories.
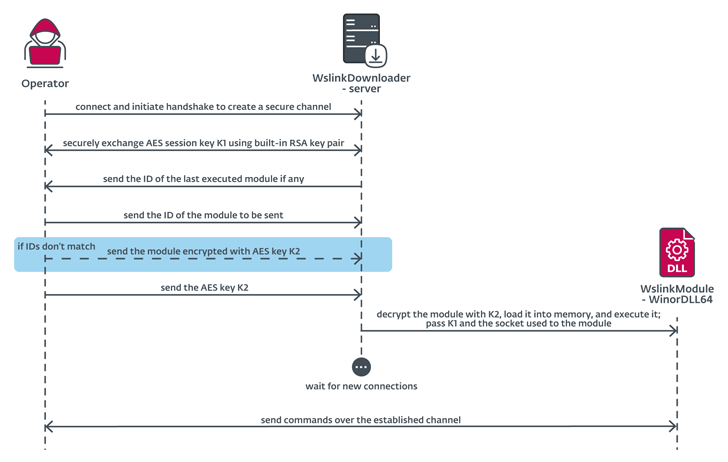
Wslink was initial documented by the Slovak cybersecurity organization in Oct 2021, describing it as a “simple nevertheless exceptional” malware loader which is able of executing acquired modules in memory.
“The Wslink payload can be leveraged later for lateral motion, due to its distinct desire in network periods,” ESET researcher Vladislav Hrčka reported. “The Wslink loader listens on a port specified in the configuration and can provide additional connecting clientele, and even load a variety of payloads.”
Intrusions leveraging the malware are mentioned to be hugely specific owing to the point that only a handful of detections have been noticed to day in Central Europe, North America, and the Center East.
In March 2022, ESET elaborated on the malware’s use of an “highly developed multi-layered virtual machine” obfuscator to evade detection and resist reverse engineering.
The inbound links to Lazarus Group stem from overlaps in conduct and code to that of prior strategies – Procedure GhostSecret and Bankshot – which have been attributed to the highly developed persistent menace.
This involves similarities with the GhostSecret samples comprehensive by McAfee in 2018, which come with a “facts-gathering and implant-installation ingredient” that operates as a support, mirroring the similar actions of Wslink.
ESET explained the payload was uploaded to the VirusTotal malware database from South Korea, where some of the victims are located, introducing credence to the Lazarus involvement.
The conclusions are at the time again demonstrative of the wide arsenal of hacking resources utilized by the Lazarus Team to infiltrate its targets.
“Wslink’s payload is focused to supplying suggests for file manipulation, execution of further code, and getting in depth information about the fundamental process that maybe can be leveraged later for lateral movement,” ESET mentioned.
Identified this report appealing? Adhere to us on Twitter and LinkedIn to read much more exceptional written content we put up.
Some parts of this article are sourced from:
thehackernews.com

 New S1deload Malware Hijacking Users’ Social Media Accounts and Mining Cryptocurrency
New S1deload Malware Hijacking Users’ Social Media Accounts and Mining Cryptocurrency