An active botnet comprising hundreds of hundreds of hijacked techniques unfold throughout 30 nations around the world is exploiting “dozens of acknowledged vulnerabilities” to target greatly-employed articles management systems (CMS).
The “KashmirBlack” campaign, which is considered to have started all around November 2019, aims for preferred CMS platforms these types of as WordPress, Joomla!, PrestaShop, Magneto, Drupal, Vbulletin, OsCommerence, OpenCart, and Yeager.
“Its nicely-intended infrastructure can make it straightforward to broaden and insert new exploits or payloads devoid of a great deal hard work, and it employs advanced approaches to camouflage itself, keep undetected, and secure its operation,” Imperva researchers reported in a two-portion evaluation.
The cybersecurity firm’s 6-month-extended investigation into the botnet reveals a intricate operation managed by a person command-and-manage (C2) server and additional than 60 surrogate servers that converse with the bots to send new targets, permitting it to grow the dimension of the botnet through brute power assaults and installation of backdoors.
The main reason of KashmirBlack is to abuse means of compromised devices for Monero cryptocurrency mining and redirect a website’s legit traffic to spam pages. But it has also been leveraged to carry out defacement assaults.
Irrespective of the motive, the exploitation tries start off with earning use of PHPUnit RCE vulnerability (CVE-2017-9841) to infect shoppers with upcoming-stage destructive payloads that connect with the C2 server.
Primarily based on the attack signature it located throughout as soon as this sort of defacements, Imperva scientists said they thought the botnet was the work of a hacker named Exect1337, a member of the Indonesian hacker crew PhantomGhost.
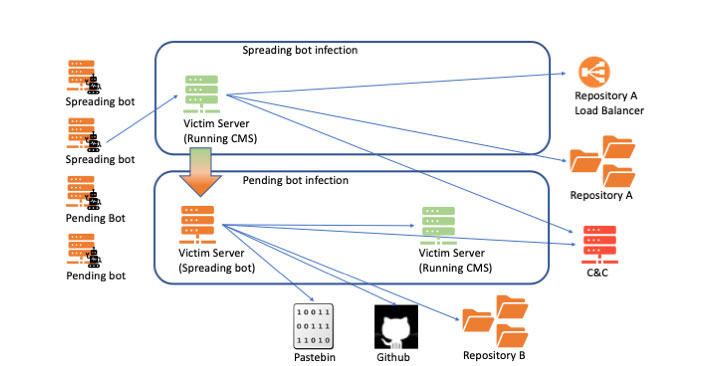
KashmirBlack’s infrastructure is sophisticated and includes a selection of relocating pieces, together with two independent repositories — a single to host exploits and payloads, and the other to keep the malicious script for communication with the C2 server.
The bots them selves are both specified as a ‘spreading bot,’ a sufferer server that communicates with the C2 to obtain commands to infect new victims, or a ‘pending bot,’ a newly compromised sufferer whose function in the botnet is still to be outlined.
Even though CVE-2017-9841 is used to turn a sufferer into a spreading bot, productive exploitation of 15 distinct flaws in CMS systems leads to a target internet site getting to be a new pending bot in the botnet. A individual WebDAV file add vulnerability has been employed by the KashmirBlack operators to final result in defacement.
But just as the botnet grew in size and extra bots commenced fetching payloads from the repositories, the infrastructure was tweaked to make it a lot more scalable by including a load balancer entity that returns the handle of 1 of the redundant repositories that have been recently setup.
The most recent evolution of KashmirBlack is perhaps the most insidious a person. Very last thirty day period, the researchers discovered the botnet working with Dropbox as a replacement for its C2 infrastructure, abusing the cloud storage service’s API to fetch attack recommendations and upload attack studies from the spreading bots.
“Moving to Dropbox will allow the botnet to conceal illegitimate prison activity driving legit web services,” Imperva claimed. “It is nevertheless a different action towards camouflaging the botnet traffic, securing the C&C operation and, most importantly, making it challenging to trace the botnet back again to the hacker at the rear of the procedure.”
Discovered this post fascinating? Abide by THN on Fb, Twitter and LinkedIn to study extra special written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Should a conscious robot get the same rights as a human?
Should a conscious robot get the same rights as a human?