At minimum eight web-sites affiliated with delivery, logistics, and fiscal providers firms in Israel ended up specific as component of a watering gap attack.
Tel Aviv-based cybersecurity company ClearSky attributed the attacks with small assurance to an Iranian risk actor tracked as Tortoiseshell, which is also called Crimson Sandstorm (earlier Curium), Imperial Kitten, and TA456.
“The contaminated internet sites collect preliminary consumer information through a script,” ClearSky reported in a technical report revealed Tuesday. Most of the impacted internet websites have been stripped of the rogue code.
Tortoiseshell is recognized to be lively since at least July 2018, with early attacks focusing on IT suppliers in Saudi Arabia. It has also been observed environment up fake employing internet websites for U.S. army veterans in a bid to trick them into downloading remote access trojans.
That mentioned, this is not the first time Iranian action clusters have established their sights on the Israeli transport sector with watering holes.
The attack process, also termed strategic web site compromises, will work by infecting a web page that’s recognised to be usually visited by a team of customers or all those within just a certain industry to permit the distribution of malware.
In August 2022, an emerging Iranian actor named UNC3890 was attributed to a watering gap hosted on a login web page of a reputable Israeli shipping firm that’s intended to transmit preliminary details about the logged-in person to an attacker-managed area.
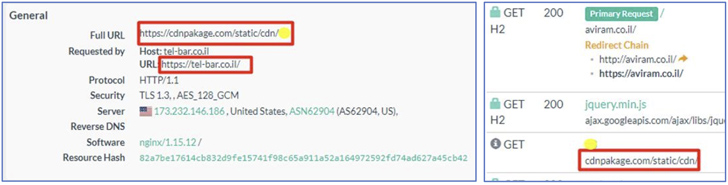
The most up-to-date intrusions documented by ClearSky display that the destructive JavaScript injected into the web-sites functions in a very similar manner, gathering info about the technique and sending it to a remote server.
Upcoming WEBINARZero Have faith in + Deception: Understand How to Outsmart Attackers!
Uncover how Deception can detect advanced threats, cease lateral motion, and greatly enhance your Zero Have confidence in approach. Be part of our insightful webinar!
Preserve My Seat!
The JavaScript code even further tries to decide the user’s language choice, which ClearSky reported could be “valuable to the attacker to personalize their attack dependent on the user’s language.”
On leading of that, the attacks also make use of a area named jquery-stack[.]on the internet for command-and-management (C2). The purpose is to fly beneath the radar by impersonating the genuine jQuery JavaScript framework.
The development will come as Israel proceeds to be the most distinguished concentrate on for Iranian state-sponsored crews. Microsoft, earlier this month, highlighted their new method of combining “offensive cyber operations with multi-pronged affect operations to gas geopolitical modify in alignment with the regime’s objectives.”
Discovered this posting appealing? Observe us on Twitter and LinkedIn to read through a lot more unique articles we write-up.
Some parts of this article are sourced from:
thehackernews.com


 50% of UK CEOs See Cyber as a Bigger Business Risk than the Economy
50% of UK CEOs See Cyber as a Bigger Business Risk than the Economy