A team of researchers currently unveiled earlier undisclosed capabilities of an Android adware implant formulated by a sanctioned Iranian menace actor that could permit attackers spy on personal chats from common fast messaging apps, force Wi-Fi connections, and automobile-reply phone calls from unique figures for uses of eavesdropping on conversations.
In September, the US Section of the Treasury imposed sanctions on APT39 (aka Chafer, ITG07, or Remix Kitten) — an Iranian danger actor backed by the country’s Ministry of Intelligence and Security (MOIS) — for carrying out malware strategies targeting Iranian dissidents, journalists, and worldwide businesses in the telecom and travel sectors.
Coinciding with the sanctions, the Federal Bureau of Investigation (FBI) unveiled a community threat examination report describing many resources utilised by Rana Intelligence Computing Firm, which operated as a entrance for the malicious cyber things to do done by the APT39 team.
Formally linking the operations of APT39 to Rana, the FBI in depth 8 individual and distinctive sets of earlier undisclosed malware utilized by the group to carry out their laptop intrusion and reconnaissance things to do, like an Android spyware app identified as “optimizer.apk” with info-stealing and distant accessibility capabilities.
“The APK implant had details stealing and remote access functionality which gained root access on an Android machine without having the user’s awareness,” the agency stated.
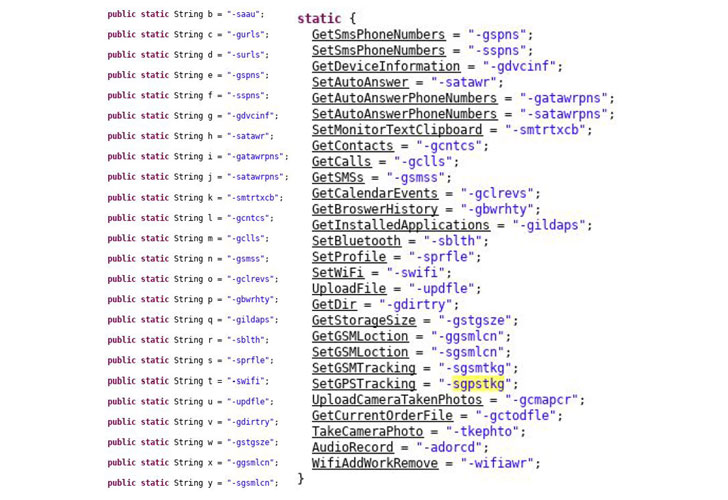
“The main capabilities include things like retrieving HTTP GET requests from the C2 server, acquiring unit facts, compressing and AES-encrypting the collected info, and sending it by way of HTTP Article requests to the malicious C2 server.”
ReversingLabs, in a freshly printed report these days, dug further into this implant (“com.android.providers.optimizer”) utilizing a preceding unobfuscated edition of the malware described in the FBI Flash report.
According to researcher Karlo Zanki, not only did the implant have permissions to document audio and consider shots for government surveillance applications, but it also contained a aspect to add a customized Wi-Fi entry issue and drive a compromised gadget to link to it.
“This characteristic was most likely released to keep away from probable detection owing to uncommon details website traffic use on the target’s cell account,” Zanki mentioned in an analysis.
Also of notice was the capability to immediately solution calls from precise phone numbers, thereby allowing for the risk actor to tap on discussions on-need.
Moreover that includes aid for getting commands sent by means of SMS messages, the most recent variant of “optimizer” malware referenced by the FBI abused accessibility companies to entry contents of prompt messaging purposes this sort of as WhatsApp, Instagram, Telegram, Viber, Skype, and an unofficial Iran-primarily based Telegram customer known as Talaeii.
It truly is value noting that Telegram had previously issued “unsafe” warnings to end users of Talaeii and Hotgram in December 2018 subsequent disclosure from the Center for Human Rights in Iran (CHRI) citing security problems.
“When targeting individuals, menace actors normally want to observe their interaction and movement,” Zanki concluded. “Cellular phones are most suited for these plans since of the computing electric power contained in your pocket, and the simple fact that most individuals have them all the time.”
“Considering that the Android platform maintains the most important component of the worldwide smartphone sector share, it follows that it is also the main focus on of cell malware.”
Found this posting attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to examine additional special information we post.
Some parts of this article are sourced from:
thehackernews.com


 HMRC Reported 11 “Serious” Personal Data Incidents to ICO this Financial Year
HMRC Reported 11 “Serious” Personal Data Incidents to ICO this Financial Year