An Iranian country-point out menace actor has been joined to a new wave of phishing attacks concentrating on Israel which is created to deploy an updated model of a backdoor known as PowerLess.
Cybersecurity company Check Issue is monitoring the activity cluster less than its legendary creature cope with Educated Manticore, which reveals “solid overlaps” with a hacking crew acknowledged as APT35, Charming Kitten, Cobalt Illusion, ITG18, Mint Sandstorm (previously Phosphorus), TA453, and Yellow Garuda.
“Like numerous other actors, Educated Manticore has adopted modern traits and began utilizing ISO pictures and probably other archive documents to initiate infection chains,” the Israeli organization reported in a technological report revealed nowadays.
Energetic considering that at the very least 2011, APT35 has solid a extensive net of targets by leveraging fake social media personas, spear-phishing tactics, and N-working day vulnerabilities in internet-exposed purposes to obtain first entry and drop different payloads, such as ransomware.
The growth is an indication that the adversary is consistently refining and retooling its malware arsenal to increase their performance and resist examination endeavours, though also adopting increased methods to evade detection.
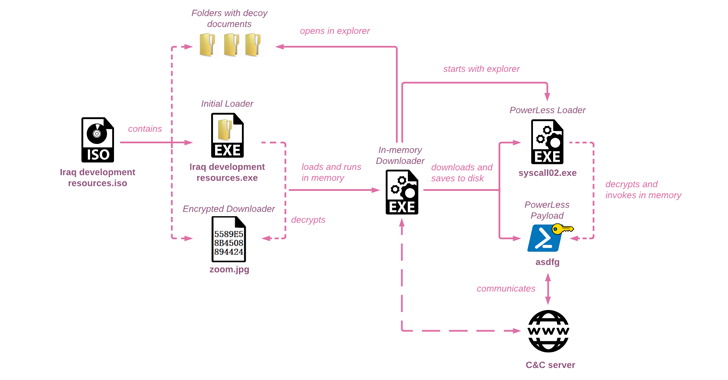
The attack chain documented by Check Place commences with an ISO disk picture file that tends to make use of Iraq-themed lures to fall a customized in-memory downloader that ultimately launches the PowerLess implant.
The ISO file functions as a conduit to display a decoy document prepared in Arabic, English, and Hebrew, and purports to characteristic educational material about Iraq from a legit non-gain entity termed the Arab Science and Technology Foundation (ASTF), indicating that the investigation local community may possibly have been the target of the marketing campaign.
The PowerLess backdoor, previously spotlighted by Cybereason in February 2022, will come with capabilities to steal details from web browsers and apps like Telegram, acquire screenshots, record audio, and log keystrokes.
“Although the new PowerLess payload continues to be identical, its loading mechanisms have considerably improved, adopting techniques hardly ever found in the wild, this kind of as utilizing .NET binary files made in mixed manner with assembly code,” Check Position explained.
“PowerLess [command-and-control] communication to the server is Base64-encoded and encrypted right after acquiring a key from the server. To mislead scientists, the menace actor actively adds 3 random letters at the beginning of the encoded blob.”
Future WEBINARZero Have confidence in + Deception: Find out How to Outsmart Attackers!
Find how Deception can detect sophisticated threats, end lateral movement, and boost your Zero Belief tactic. Join our insightful webinar!
Conserve My Seat!
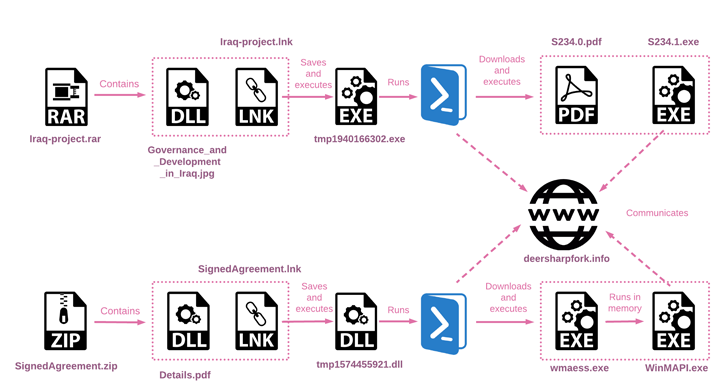
The cybersecurity firm claimed it also found two other archive data files utilized as part of a distinct intrusion established that shares overlaps with the aforementioned attack sequence owing to the use of the same Iraq-themed PDF file.
Even more examination has uncovered that the infection chains arising from these two archive information culminate in the execution of a PowerShell script which is engineered to download two data files from a remote server and run them.
“Educated Manticore continues to evolve, refining previously noticed toolsets and delivering mechanisms,” Test Issue explained, including “the actor adopts well-liked developments to steer clear of detection” and keeps “acquiring customized toolsets using state-of-the-art techniques.”
“For the reason that it is an updated version of formerly reported malware, […] it is important to notice that it may only depict the early stages of infection, with sizeable fractions of article-an infection activity nevertheless to be witnessed in the wild.”
Located this post fascinating? Stick to us on Twitter and LinkedIn to read extra unique content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 #RSAC: US DoJ Prioritizes Victim Support in Cybercrime Crackdown
#RSAC: US DoJ Prioritizes Victim Support in Cybercrime Crackdown