The Iranian nation-state team recognised as MuddyWater has been observed carrying out destructive attacks on hybrid environments less than the guise of a ransomware procedure.
That is in accordance to new findings from the Microsoft Threat Intelligence staff, which uncovered the threat actor concentrating on both on-premises and cloud infrastructures in partnership with a different emerging action cluster dubbed DEV-1084.
“Even though the risk actors attempted to masquerade the action as a common ransomware campaign, the unrecoverable actions demonstrate destruction and disruption were being the final targets of the operation,” the tech big exposed Friday.
MuddyWater is the title assigned to an Iran-primarily based actor that the U.S. govt has publicly connected to the country’s Ministry of Intelligence and Security (MOIS). It is been identified to be energetic considering that at the very least 2017.
It can be also tracked by the cybersecurity neighborhood below different names, like Boggy Serpens, Cobalt Ulster, Earth Vetala, ITG17, Mercury, Seedworm, Static Kitten, TEMP.Zagros, and Yellow Nix.
Attacks mounted by the group have mainly singled out Center Japanese nations, with intrusions noticed about the earlier yr leveraging the Log4Shell flaw to breach Israeli entities.
The newest findings from Microsoft expose the risk actor almost certainly worked with each other with DEV-1084 to pull off the attack, the latter of which conducted the damaging steps after MuddyWater effectively gained a foothold on to the target natural environment.
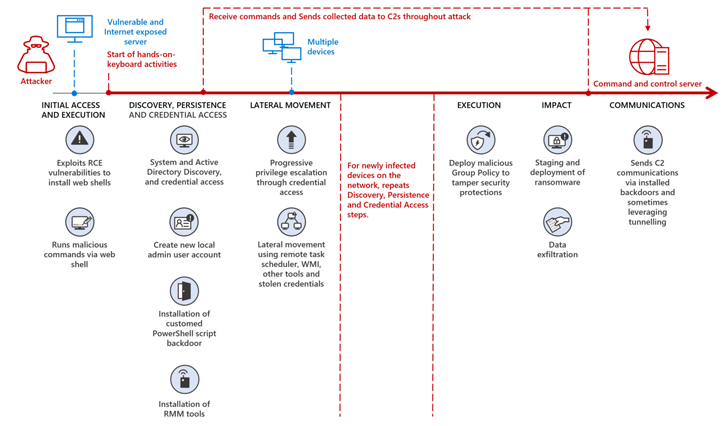
“Mercury possible exploited known vulnerabilities in unpatched apps for original obtain just before handing off accessibility to DEV-1084 to perform intensive reconnaissance and discovery, create persistence, and move laterally in the course of the network, frequently waiting weeks and from time to time months in advance of progressing to the future stage,” Microsoft claimed.
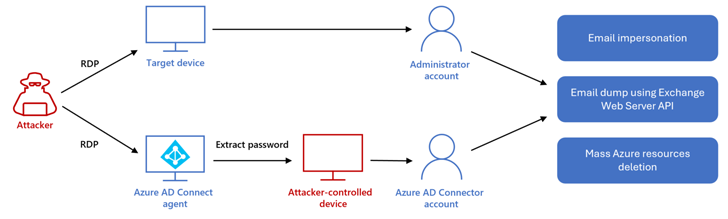
In the exercise detected by Redmond, DEV-1084 subsequently abused very privileged compromised credentials to complete encryption of on-premise products and substantial-scale deletion of cloud resources, such as server farms, digital machines, storage accounts, and digital networks.
Furthermore, the threat actors gained total access to email inboxes through Trade Web Companies, working with it to accomplish “countless numbers of look for activities” and impersonate an unnamed significant-position employee to mail messages to both equally inner and exterior recipients.
All these steps are steps are approximated to have transpired in excess of a roughly three-hour timeframe beginning at 12:38 a.m. (when the attacker logged into the Microsoft Azure environment by means of compromised qualifications) and ending at 3:21 a.m. (when the attacker despatched e-mail to other get-togethers immediately after the successful cloud disruption).
It can be worth noting right here that DEV-1084 refers to the exact risk actor that assumed the “DarkBit” persona as portion of a ransomware and extortion attack aimed at Technion, a leading investigate college in Israel, in February. The Israel Nationwide Cyber Directorate, previous month, attributed the attack to MuddyWater.
Future WEBINARLearn to Safe the Identity Perimeter – Verified Approaches
Make improvements to your small business security with our future specialist-led cybersecurity webinar: Discover Id Perimeter techniques!
Don’t Pass up Out – Help you save Your Seat!
“DEV-1084 […] presented alone as a felony actor intrigued in extortion, very likely as an endeavor to obfuscate Iran’s connection to and strategic enthusiasm for the attack,” Microsoft additional.
The one-way links between Mercury and DEV-1084 originate from infrastructure, IP address, and tooling overlaps, with the latter noticed working with a reverse tunneling utility identified as Ligolo, a staple MuddyWater artifact.
That explained, there is not sufficient proof to figure out if DEV-1084 operates independently of MuddyWater and collaborates with other Iranian actors, or if it is really a sub-staff that is only summoned when there is a need to carry out a destructive attack.
Cisco Talos, early last yr, described MuddyWater as a “conglomerate” comprising quite a few lesser clusters instead than a one, cohesive group. The emergence of DEV-1084 indicates a nod in this route.
“Whilst these teams appear to be to work independently, they are all inspired by the exact same elements that align with Iranian countrywide security targets, like espionage, mental theft, and destructive or disruptive operations primarily based on the victims they concentrate on,” Talos observed in March 2022.
Found this article fascinating? Follow us on Twitter and LinkedIn to read much more exceptional material we submit.
Some parts of this article are sourced from:
thehackernews.com


 Apple Releases Updates to Address Zero-Day Flaws in iOS, iPadOS, macOS, and Safari
Apple Releases Updates to Address Zero-Day Flaws in iOS, iPadOS, macOS, and Safari