Malware investigation is an crucial part of security researcher’s do the job. But doing the job with malicious samples can be perilous — it necessitates specialised instruments to report their action, and a protected atmosphere to avoid unintended hurt.
However, manual lab setup and configuration can establish to be a laborious and time-consuming method.
In this post, we will glimpse at 4 means to make a reverse engineering lab, focus on how to help you save time, and, likely, boost the detection rate utilizing a cloud services, and a encouraged checklist of applications for a thorough setup.
What is a malware assessment lab?
In essence, a malware assessment lab delivers a risk-free, isolated space for analyzing malware.
The setup can selection from a uncomplicated virtual equipment employing VirtualBox to a a lot more intricate network of interconnected equipment and real networking components.
But in this post, we’ll look at making a lab tailor-made for static analysis, so what we will will need is a safe surroundings wherever we can run disassemblers, edit binary documents and debug.
There are a pair of ways we can go about producing it:
1 — Virtualization
Most likely the most basic way to create a secure and isolated surroundings is by using a virtual machine.
A well-known solution is Digital Box, open up-source application from Oracle. If you are on Linux, to install it, just use the command sudo apt put in virtualbox. VMWare is another popular decision — it’s a business method, but there is a no cost tier.
Established up is straightforward — obtain and install the computer software, build a virtual machine, configure the configurations to make sure it would not have network obtain or shared folders with the host, and then boot it with an .ISO file of your picked out functioning program.
But this method has some negatives: you will have to establish tailor made detection rules for identifying suspicious or malicious entities, independently research rising techniques, maintain configurations, and ascertain logging procedures making use of available resources. This elevated focus on maintenance and configuration detracts from the time spent on assessment.
Pros
- No cost or obtainable at a lower price tag
- The setup is uncomplicated
- Presents an isolated environment if configured the right way
Negatives
- The general performance will take a strike
- Restricted scalability bottlenecked by your CPU
- The malware could escape to the host
- Needs to manually configure detection procedures
2 — Committed components
In circumstance you have an previous laptop lying around or you have the indicates to get one particular or create a Laptop, this is unquestionably an selection. You never have to crack the bank both — the 11-13th era of Intel processors make even spending plan devices additional than a practical option.
The principal upside of opting for a actual physical computer system is greater overall performance and bigger security due to the fact you can make certain the machine is definitely isolated from all equipment and networks.
Pros:
- Most performant alternative
- Entirely isolated ecosystem
- Can be endlessly customized
Cons:
- Significant-close components is expensive
- Requires software and hardware servicing
- Needs to be configured to perform
3 — A cloud lab
Producing a malware lab in the cloud basically isn’t really as challenging as it could possibly audio. Also — it is totally free! All you require is an account at AWS, or any equivalent cloud assistance service provider, and a device to join to it. The set up might be a little more sophisticated than a regional virtual equipment, but there are quite a few tutorials that you can use as a guidebook.
If you pick to function with AWSs, search for Kali in the market to established up a Kali Linux Digital Equipment. To use the GUI, you can make a VNC server and hook up to your lab with a instrument like VNC Viewer.
A person of the downsides of this approach is that it can be no cost till it just isn’t. If you exceed the boundaries of the absolutely free tier, your cloud bill could balloon immediately.
From time to time, cloud suppliers may well also limit malware execution, posing lawful dangers. Furthermore, cloud equipment demand assist, burdening IT operations. Even though suited for novice unbiased researchers, this method offers drawbacks in company options. Crucially, it lacks the skill to counteract malware’s VM detection and bypass anti-evasion methods.
Pros:
- Scalability
- No hardware routine maintenance
- Isolated from your network for greater security
Cons:
- Prospective lawful hazards.
- Hard set up
- Desires to be configured to work
- Latency decreases the high quality of get the job done
- Highly developed setups are pricey
- Vulnerable to anti-avastin strategies
4 — Sandbox-as-a-Provider
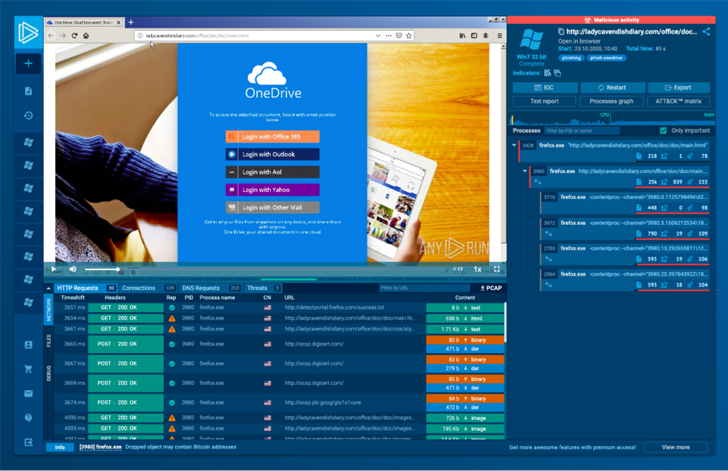
One important edge of cloud-based mostly sandbox services is their developed-in resilience towards VM detection. This lowers the likelihood of a malware sample recognizing it’s in a virtual equipment and halting its execution, a function that calls for guide configuration in other sandboxes.
Also, in a company like this, detection guidelines are created by professionals utilizing wide malware and menace intel databases. As a consequence, the computer software can enrich analysis outcomes with approaches and IOCs, yielding more in depth output compared to uncooked knowledge from cloud or on-prem VMs.
Furthermore, cloud-dependent sandbox products and services streamline atmosphere configurations. For instance, as an alternative of generating separate snapshots in a VM, ANY.RUN’s cloud assistance enables straightforward surroundings setup by means of a person-pleasant menu each individual time a lab is initiated.
Execs
- Will save time
- Ease of use
- Protected and totally isolated from your network
- Hardened against VM detection
- Uncomplicated configuration of the execution natural environment
Cons
- Just isn’t optimized to do the job with your toolset
- Sure answers on the marketplace may be laggy
- Virtual equipment scenarios are time-constrained
Employing an on the net, interactive sandbox this sort of as ANY.Operate alternatively of a lab presents advantage and speed. It can assistance automate sections of static evaluation, like extracting malware configurations.
If you’d like to test ANY.Operate for on your own, they are currently working a special promo for Hacker News audience:
Styles of program for reverse engineering
Here are some important instruments that will assist to you reverse-engineer malware:
- Disassemblers. Disassemblers are a will have to-have for reverse engineering. They allow for you to change device language into assembly code that is uncomplicated for human beings to recognize, so you can acquire insight into how malware functions. IDA Pro, Ghidra, and Binary Ninja are all well known disassemblers. To operate Ghidra on Linux, to start with, set up JDK and download Ghidra alone to your machine. No installation is essential, just execute these commands within the Ghidra directory: chmod +x ghirdRun and ./ghirdaRun.
- Decompilers. Decompilers are identical to disassemblers, in that they can change equipment code into resource code. It can be beneficial for understanding the malware’s architecture and figuring out precise features or modules. Preferred decompilers incorporate IDA Pro, Ghidra, and Hex-Rays.
- Debuggers. Debuggers support programmers locate errors and troubleshoot them by allowing them go by way of the code line by line, established breakpoints, and notice the way the malware features. Numerous of the most frequently made use of debuggers are OllyDbg, x64dbg, and WinDbg. x64dbg is 1 of the most well known selections appropriate now: it is really absolutely free and out there to down load from x64dbg.com
- HEX editors. Hex editors are practical for receiving a nearer glimpse at binary information, knowing how they’re organized, spotting individual values, and manipulating the file as a way of observing how the virus responds. Prevalent hex editors consist of HxD and Hex Workshop.
- Network investigation resources. Sure malware necessitates an on line link in purchase to work. Network examination plans like Wireshark can help you detect and take a look at the targeted visitors sent and received by that malware.
Necessary malware examination applications
It is up to the analyst to determine what computer software to put in, but, in our view, the checklist of critical applications appears like this:
- Detect It Straightforward. For analyzing varieties of documents
- Approach Hacker. Assists you observe system resources, debug application and detect malware
- Procedure Observe. A Checking device for Windows that shows serious-time file method, Registry, and process/thread activity
- Wireshark. For analyzing network activity
- x64dbg and Ghidra. Demanded for both equally static and dynamic investigation.
Oh, and if you want to get a lab which is been pre-configured, you can use a specialized distribution package like Remnux, which arrives with most of all those systems currently mounted.
There is also FLARE VM — a collection of program installation scripts for Windows-centered devices that allows you to simply established up and maintain a reverse engineering setting on a digital device.
Wrapping up
We have mentioned 4 different approaches for making an assessment lab: employing virtualization, creating a devoted equipment, deploying a cloud lab, or subscribing to a sandbox-as-a-services.
Each of these ways arrives with its own established of added benefits and negatives, and the suitable preference is dependent on what you are trying to attain and the methods available to you.
Luckily, most of these choices are absolutely totally free, so just test them all out and see what functions very best!
Located this short article intriguing? Adhere to us on Twitter and LinkedIn to study extra distinctive written content we article.
Some parts of this article are sourced from:
thehackernews.com


 ChatGPT Vulnerability May Have Exposed Users’ Payment Information
ChatGPT Vulnerability May Have Exposed Users’ Payment Information