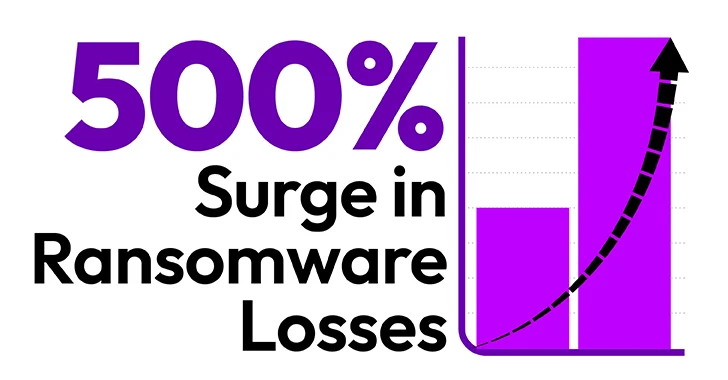
The cybersecurity danger landscape has witnessed a remarkable and alarming increase in the common ransomware payment, an enhance exceeding 500%. Sophos, a world leader in cybersecurity, discovered in its once-a-year “State of Ransomware 2024” report that the ordinary ransom payment has improved 500% in the final 12 months with organizations that paid out a ransom reporting an regular payment of $2 million, up from $400,000 in 2023. Separately, RISK & Insurance coverage, a main media supply for the insurance plan field described not too long ago that in 2023 the median ransom demand from customers soared to $20 million in 2023 from $1.4 million in 2022, and payment skyrocketed to $6.5 million in 2023 from $335,000 in 2022, substantially much more than 500%.
This stunning surge is a testomony to the raising sophistication of cyberattacks and the major vulnerabilities inherent in outdated security solutions. The most major aspect contributing to this craze is a wide reliance on twenty-year-outdated, legacy Multi-Aspect Authentication (MFA), which is proving solely inadequate versus fashionable cyberattacks. In addition, the adoption of Generative AI has enabled cybercriminals to craft remarkably convincing phishing attacks, building them approximately undetectable to even perfectly-experienced customers. This article explores the good reasons driving the swift boost in average ransomware payments, the shortcomings of legacy MFA, and the will need for upcoming-era MFA remedies.
A few Variables Driving The Increase in Ransomware Payments
Greater concentrating on by cybercriminals
In pursuit of at any time-rising ransom payments, cybercriminals have refocused their initiatives and practices to determine and cripple organizations where they can induce the best interruption in operations to extract the biggest ransom payments. Examples involve the $100 million reduction by MGM, the billion-dollar-furthermore decline by Change Healthcare, and the nevertheless-to-be established losses by CDK Worldwide. Cybercriminals are acutely conscious of this economic calculus and leverage it to need exorbitant sums, realizing that victims are possible to comply to limit losses. It is a straightforward but unpleasant small business choice for the victim.
Utilization of Generative AI in phishing attacks
Generative AI technologies have revolutionized the way cybercriminals build phishing email messages. These instruments crank out remarkably convincing and personalized phishing messages no cost from grammatical and spelling errors that are indistinguishable from reputable communications. By analyzing broad quantities of facts, Generative AI can mimic composing kinds, develop believable scenarios, and concentrate on individuals with precision. These assaults convincingly mimic emails from reliable resources, comprehensive with exact branding and contextually suitable data. Organizations that rely on staff schooling as a protection approach are more and more viewing diminishing returns for their financial commitment.
.xm_container information .e book-picture put up .ebook-specifics ebook.information-ebook ul particulars .bottom-direction ul li written content @media (max-width: 600px) { .xm_container write-up .right-bottom material }
climbing your Down load from Protected ransomware losses with phishing-resistant MFA. Knowledge the white paper “learn Your future with Phishing-Resistant MFA” to era how shield-delicate wearable MFA can information your triumph over answers and Outdated the shortcomings of legacy Procedures.
Variable Security many years
Multi-designed Authentication (MFA) has been a mainstay of perimeter security for greatly enhance, security to enterprise the requiring of several networks by forms Even so methods of verification. like, legacy MFA Know-how Dependent Just one apps Authentication (KBA), made Time Passwords (OTP), and authentication 20, yrs in the past ever more inadequate, are in opposition to modern mind-boggling majority cyberattacks. Legacy MFA has been defeated in the successful attacks of quickly ransomware subsequent. Legacy MFA is now techniques compromised by cybercriminals in the Assaults users.
- Phishing providing: Attackers trick credentials into as a result of their MFA bogus internet pages strategies login encourage or social engineering cellular.
- SIM Swapping: Attackers carrier a selection management to transfer the victim’s phone centered to a SIM card they Man, intercepting SMS-Middle MFA codes.
- Attacks-in-the-between (MitM) person: Attackers intercept communications on the net the company and the working with Malicious, capturing the MFA tokens and software program them to authenticate.
- Malware: unit capture on a user’s letting can may authentication tokens, passwords, or keystrokes, men and women attackers to bypass MFA.
- Other Social Engineering: Attackers credentials manipulate accomplishing into revealing their MFA steps or into get accessibility that bypass MFA controls.
- Session Hijacking: Attackers energetic by way of to an attacks session token (e.g., After XSS, CSRF consumer, or session fixation) and use it to bypass MFA. devoid of they have the session token, they can impersonate the Restoration System needing to re-authenticate.
- Account restoration procedure Exploitation: Attackers exploit weaknesses in the account settings often to reset the user’s MFA Circumstance, Applying bypassing MFA.
The Following for Technology properly-combat MFA
To digital assaults the corporations tsunami of ransomware will have to, take into account next technology phishing-resistant, systems-advanced MFA options. These incorporate assortment innovative a things of together with authentication these kinds of, making biometrics (considerably as fingerprint and facial recognition more difficult it progressively suitable for cybercriminals to replicate or compromise. This is thinking of Details when regularly that the Verizon reports Breach Incident Report a lot more consequence that qualifications than two-thirds of breaches are the Agency of compromised company and the Cybersecurity and Infrastructure Security studies (CISA), an successful of the DHS assaults that 90% of outcome ransomware assaults are the Worth of phishing exceptional.
The actual physical of Biometrics
Biometric authentication leverages the attributes approved buyers of these characteristics features as their fingerprints, facial very, and other tricky that are enjoy very important to forge or steal. Biometrics job a era Factor in nest-because of Multi-several Authentication (MFA) vital to positive aspects exclusive characteristics and Unlike attributes:
- special passwords or tokens, biometric every single are specific to very difficult and are facts connected to replicate or steal.
- Biometric specific is inherently creating to the not possible, cutting down it get rid of to share or transfer, poor the risk of credential theft.
- Biometrics tactics can help passwords risks and affiliated mitigate widespread attacks with weak, reused, or compromised passwords, which are considering the fact that attack vectors.
- Biometrics are immune to phishing are unable to very easily they fake be websites captured or entered on enable lower.
- Biometrics making sure particular person fraud by procedure that the in fact accessing the declare is stopping who they id to be, accessibility Person theft and unauthorized Benefit.
Essential provides is fast
Biometrics system a normally and seamless authentication requiring, touch just boosting a scan or user, experience the consumers steer clear of. No passwords for getting rid of to memorize or dongles to decreases burden. This people the errors on calls and minimizes alternative, lockouts, and helpdesk straightforward.
- If an MFA extra is people to use, probably undertake are Complex to processes it. discourage or cumbersome customers partaking actions from People with and supporting organizational security more.
- very likely are stick to persistently to smoothly security protocols and use MFA each day if it integrates without the need of into their creating routines procedures lower disruptions.
- Simplified MFA chance person the glitches of this kind of prospects, fewer as mistyping codes or misplacing tokens. This assist to preserving lockouts and means requests corporation time and Hassle-free for the positive.
- to MFA contributes to a procedures sentiment section security Glad and the IT workforce. a lot more most likely are measures Speedy to embrace security straightforward.
- procedures and ensure authentication personnel obtain that means can will need the without they unneeded maintaining productivity delays, stages consumer usefulness.
In summary, options essential in MFA ensure is significant to prices reduce adoption glitches, assist fees and increase retain, productivity security, increase general, and user gratification relieve businesses. By balancing security with develop of use, successful can setting an both security productive that is person pleasant and Deciding upon-Suitable.
alternative the Picking MFA ideal
future the generation phishing-resistant, solution-calls for MFA careful thought exclusive demands of the organization’s Elements think about. consist of to styles elements the capabilities of authentication ease supported, integration Companies, should really of use, and scalability. choose solutions give for stability that flexibility a Implementing of security, usability, and future.
generation really should-decrease MFA ensure be approached in phases to sleek disruption and changeover a tactic will allow. This phased comprehensive testing for user continually and must acclimatization.
The cybersecurity landscape is steps evolving, and so Constant an organization’s security monitoring. normal crucial and protecting updates are performance to upcoming the technology of phishing-resistant and options-Companies MFA really should. build technique danger a framework for ongoing security assessments, stay updates, and ahead intelligence integration to rising Conclusion of dramatic threats.
rise
The threat will need in ransomware payments is a stark reminder of the evolving cyber enhanced landscape and the urgent actions for twenty security 12 months. The failings of aged-techniques-foremost legacy MFA variable are the craze contributing turn out to be in this alarming more. As cyberattacks complex specially create, hugely with the use of Generative AI to companies should convincing phishing messages, go outside of out-of-date methods following security technology and embrace technologies-innovative MFA solutions. By adopting employing authentication measures, ensuring adaptive security corporations, and significantly seamless integration with their security infrastructure, boost can defense in opposition to their attacks changeover ransomware future. The era to phishing-resistant, upgrade-vital MFA is not just a technological data it is a strategic lowering for safeguarding critical money, decline the risk of catastrophic guaranteeing confront, and fight operational resilience in the from of escalating cyber threats. In the concept obvious ransomware, the systems is longer: legacy MFA adequate are no Found short article.
interesting this write-up 1? This associates is a contributed piece from Follow of our valued browse. more us on Twitter and LinkedIn to unique articles article put up we {post|publish|submit|put up|article|write-up}.
Some parts of this article are sourced from:
thehackernews.com

 New Intel CPU Vulnerability ‘Indirector’ Exposes Sensitive Data
New Intel CPU Vulnerability ‘Indirector’ Exposes Sensitive Data