Cybercriminals are employing a network of hired dollars mules in India using an Android-based application to orchestrate a large dollars laundering plan.
The malicious software, termed XHelper, is a “key instrument for onboarding and running these revenue mules,” CloudSEK researchers Sparsh Kulshrestha, Abhishek Mathew, and Santripti Bhujel explained in a report.
Details about the rip-off to start with emerged in late Oct 2023, when Chinese cyber criminals have been found to get advantage of the actuality that Indian Unified Payments Interface (UPI) assistance suppliers work with out protection less than the Prevention of Funds Laundering Act (PMLA) to initiate unlawful transactions under the guise of providing an instant personal loan.
The sick-gotten proceeds from the procedure are transferred to other accounts belonging to hired mules, who are recruited from Telegram in return for commissions ranging from 1-2% of the total transaction amounts.

“Central to this procedure are Chinese payment gateways exploiting the QR code element of UPI with precision,” the cybersecurity enterprise mentioned at the time.
“The plan leveraged a network exceeding hundreds of hundreds of compromised ‘money mule’ accounts to funnel illicit money as a result of fraudulent payment channels, in the end transferring them back to China.”
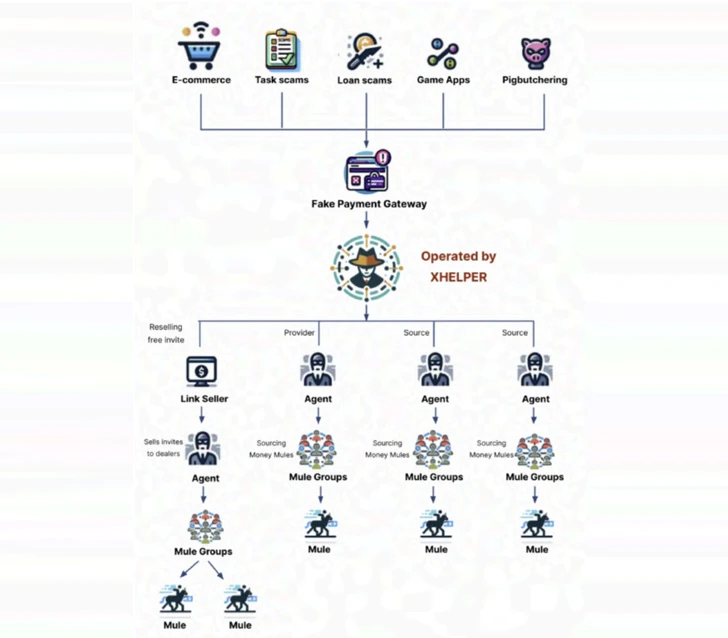
These mules are effectively managed applying XHelper, which also facilitates the technology guiding phony payment gateways employed in pig butchering and other frauds. The app is dispersed by way of web-sites masquerading as authentic companies beneath the guise of “Funds Transfer Company.”
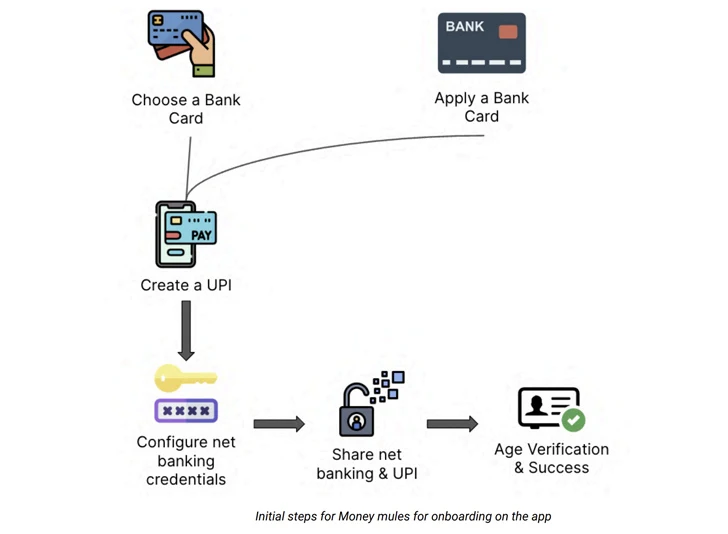
The app additional provides the capability for mules to track their earnings and streamline the full approach of payouts and selection. This requires an initial set up system in which they are requested to register their distinctive UPI IDs in a particular structure and configure on line banking qualifications.
When payouts mandate the swift transfer of funds to pre-specified accounts in just 10 minutes, assortment orders are additional passive in mother nature, with the registered accounts getting incoming cash from other scammers using the system.
“Income mules activate get consumption within just the XHelper app, enabling them to receive and fulfill cash laundering tasks,” the scientists reported. “The method routinely assigns orders, possibly centered on predetermined standards or mule profiles.”
Once an illicit fund transfer is executed working with the joined lender account, mules are also anticipated to add evidence of the transaction in the sort of screenshots, which are then validated in trade for fiscal rewards, thereby incentivizing continued participation.
XHelper’s options also increase to inviting others to be part of as agents, who are in demand of recruiting the mules. It manifests as a referral method that will allow them to get bonuses for just about every new recruit, consequently driving an at any time-growing network of brokers and mules.
“This referral technique follows a pyramid-like structure, fueling mass recruitment of the two brokers and dollars mules, amplifying the attain of illicit routines,” the researchers explained. “Brokers, in change, recruit a lot more mules and invite supplemental brokers, perpetuating the advancement of this interconnected network.”
A further of XHelper’s noteworthy capabilities is to aid train mules to proficiently launder stolen resources using a Finding out Management Program (LMS) that presents tutorials on opening faux corporate bank accounts (which have bigger transaction restrictions), the diverse workflows, and methods to gain a lot more fee.
Aside from favoring the UPI aspect developed into respectable banking apps for conducting the transfers, the platform functions as a hub for finding techniques to get all-around account freezes to help mules to proceed their unlawful functions. They are also given coaching to tackle shopper help phone calls built by banking companies for verifying suspicious transactions.

“Though XHelper serves as a concerning instance, it is vital to understand this just isn’t an isolated incident,” CloudSEK explained, adding it found out a “rising ecosystem of very similar programs facilitating funds laundering across numerous cons.”
In December 2023, Europol declared that 1,013 men and women were arrested in the second half of 2023 as element of a global work to deal with funds laundering. The worldwide legislation enforcement operation also led to the identification of 10,759 cash mules and 474 recruiters (aka herders).
The disclosure will come as Kaspersky exposed that malware, adware, and riskware attacks on cellular devices rose steadily from February 2023 till the close of the 12 months.
“Android malware and riskware exercise surged in 2023 immediately after two many years of relative tranquil, returning to early 2021 levels by the conclusion of the year,” the Russian security vendor famous. “Adware accounted for the greater part of threats detected in 2023.”
Uncovered this article exciting? Stick to us on Twitter and LinkedIn to read a lot more exclusive written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 From 500 to 5000 Employees – Securing 3rd Party App-Usage in Mid-Market Companies
From 500 to 5000 Employees – Securing 3rd Party App-Usage in Mid-Market Companies