Attackers exploiting an array of Google Services, such as Sorts, Firebase, Docs and more to strengthen phishing and BEC campaigns.
A spike in modern phishing and business email compromise (BEC) assaults can be traced back again to criminals mastering how to exploit Google Products and services, according to research from Armorblox.
Social distancing has pushed full businesses into the arms of the Google ecosystem searching for a trustworthy, basic way to digitize the regular office. Armorblox co-founder and head of engineering Arjun Sambamoorthy just printed a report detailing how now-ubiquitous providers like Google Forms, Google Docs and other individuals are becoming utilized by destructive actors to give their spoofing tries a fake veneer of legitimacy, both equally to security filters and victims.
“Open APIs, extensible integrations and developer-pleasant equipment imply that overall virtual offices — full with virtual workflows — can exist in a Google ecosystem,” Sambamoorthy wrote. “Unfortunately, Google’s open up and democratized mother nature is being exploited by cybercriminals to defraud folks and companies of income and sensitive facts.”
The report offers several particular illustrations of how Google Expert services aid attackers with their techniques.
Google Kinds
1 campaign employed a Google Variety and an American Convey logo to try and get victims to enter delicate information.
“Hosting the phishing web page on a Google Form helps the initial email evade any security filters that block known lousy back links or domains,” in accordance to Sambamoorthy. “Since Google’s domain is inherently dependable, and Google varieties are utilized for various legit factors, no email security filter would realistically block this url on ‘day zero.’”

The American Convey scam. Source: Armorblox.
An additional attack Sambamoorthy observed made use of a fictious letter from a childless widow searching for an individual to whom she could bequeath her fortune. The website link in the email sales opportunities to a Google Form with a blank query discipline. In this instance, the Google Variety will help attackers with the social engineering method, the report explained.
“Many persons will really feel the email is suspicious following likely through the material and browsing this dummy variety,” he continued. “But some people will post the only solution allowed by the type, or they will send a reply to the address offered in the email. This permits attackers to shortlist the most naive and emotionally susceptible email recipients, who will be primary targets for abide by-up email messages from the childless widow.
Google Firebase, Google Web sites & Google Docs
Google’s cell platform Firebase was utilized in a further scheme to host a phishing page, which authorized it to sneak by way of email filters for the identical motive – mainly because Firebase is trusted.
In a Google-providers-powered payroll diversion fraud rip-off that Sambamoorthy highlighted, a fraud email link despatched recipients to a Google Doc file to “confirm” their payment information.
And in but one more attack, an email was sent to victims, purportedly from their own IT staff, asking them to assessment a secure concept on Microsoft Teams from a colleague. The url led to web web page with a bogus Office 365 login portal hosted on Google Web pages.
“The malice of the page’s intent was hidden at the rear of the legitimacy of the page’s domain,” Sambamoorthy included. “This web page would go most eye exams all through chaotic mornings (which is when the email was despatched out), with individuals happily assuming it to be a reputable Microsoft webpage.”
Hijacking Google Services: A Trend
The capability for destructive actors to leverage Google Expert services for their activities is beginning to emerge as a whole-fledged pattern.
At the beginning of November, scientists found 265 Google Varieties impersonating brands like AT&T, Citibank and Capitol A single and even authorities agencies like the Inner Income Services and the Mexican Governing administration employed in phishing assaults.
The forms were removed by Google immediately after scientists from Zimperium claimed them.
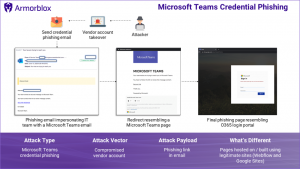
The Groups phish. Source: Armorblox.
Just days before, scammers were located to be making use of a legitimate Google Generate collaboration to trick victims into clicking on malicious inbound links.
Even Google Calendar has been abused in the previous, in a advanced cyberattack that targeted cellular Gmail end users by means of fraudulent, unsolicited conference notifications.
For its part, Google stresses the business is using just about every evaluate to hold malicious actors off their platforms.
“We are deeply fully commited to protecting our end users from phishing abuse across our solutions, and are continuously doing work on further measures to block these types of assaults as solutions evolve,” a Google spokesperson told Threatpost by email.
The statement added that Google’s abuse coverage prohibits phishing and emphasised that the business is intense in combating abuse.
“We use proactive actions to avert this abuse and customers can report abuse on our platforms,” the assertion stated. “Google has solid measures in position to detect and block phishing abuse on our solutions.”
Sambamoorthy advised Threatpost that the security responsibility does not relaxation on Google by itself and that companies should not depend solely on Google’s security protections for their sensitive information.
“Google faces a fundamental problem due to the fact what helps make their products and services free and uncomplicated to use also lowers the bar for cybercriminals to establish and start efficient phishing attacks,” he stated. “It’s critical to keep in mind that Google is not an email security business — their key responsibility is to produce a functioning, performant email support.”
Sambamoorthy claimed two-aspect authentication (2FA) and preserving strong passwords with a password manager are the very best strategies for users to guard themselves. In addition to individuals best techniques, the report advisable “rigorous eye tests” of e-mail “related to cash and details.”
Companies, he mentioned, really should build standard security guidelines and set up mechanisms which are able to adapt to new and evolving threats.
“Security has an important ‘process’ component, so corporations ought to guarantee they have the appropriate controls, checks, and balances in area to protect end users and facts,” Sambamoorthy stated. “Since these attack styles are often evolving, businesses must make investments in security systems that have developed-in feedback mechanisms. These mechanisms should really discover from new assaults and refine detection algorithms with time ”
Some parts of this article are sourced from:
threatpost.com


 Logitech's latest wireless esports mouse is its lightest yet
Logitech's latest wireless esports mouse is its lightest yet