The details uncovered in a general public cloud bucket bundled PII, church-donation information and facts, shots and users’ make contact with lists.
The Christian religion app Pray.com has leaked non-public information for up to 10 million persons, in accordance to researchers.
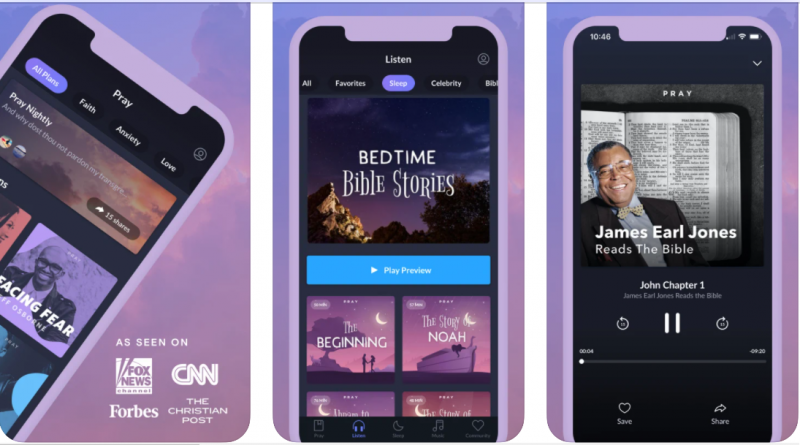
The app gives “daily prayer and Bible tales to inspire, teach and aid you sleep” on a subscription foundation. Subscriptions operate anywhere from $50 to $120. It provides a host of audio material, together with providers from televangelists like Joel Osteen, and spiritual recordings utilizing movie star voices like Kristin Bell and James Earl Jones.
It has been downloaded by much more than 1 million persons on Google Play, and ranks as the #24 way of life app in the Apple Application keep.
vpnMentor analysts identified a number of open up, publicly accessible cloud databases (Amazon Web Solutions S3 buckets, in this case) belonging to Pray.com, containing 1.9 million files – about 262 GB worth of data. Most of this was interior facts, but a single of the buckets contained concerning data, the researchers reported. 80,000 files contained several individual identifiable details (PII) for tens of hundreds of thousands of persons – and not just from Pray.com users.
These incorporated shots uploaded by the app’s consumers (profile pics and avatars for Pray.com’s non-public “Communities” social network), which include those people of minors. And, the data files integrated CSV data files from church buildings that use the app to converse with their congregations, the investigation identified. These files contained lists of the church’s attendees, with info for each and every churchgoer that involved names, house and email addresses, phone figures and marital status.
The app also says that it facilitates church donations – buyers can donate right by means of the application to any church that is portion of the Pray.com ecosystem. The donations ended up also logged in the bucket, alongside with the donation amount of money, the donor’s PII, and Pray.com’s cost for processing the donation. On the other hand, lacking ended up any documents of donations remaining forwarded to churches.
“The very long lists of donations processed by Pray.com would give cybercriminals invaluable insight into the funds of application people and an prospect to get in touch with them appearing as the application, querying a preceding donation,” scientists said.
Most damningly, the cloud database provided entire phone publications from customers. When a individual joins the Communities social network, the application asks if it can invite pals to join. If a consumer suggests of course, the app uploads the user’s entire ‘phonebook’ from their system, made up of all contacts and related facts.
Scientists explained that a lot of of these phonebooks contained hundreds of specific contacts, each 1 revealing that person’s PII data, which include names, phone quantities, email, residence and enterprise addresses, and other particulars, like company names and spouse and children ties. Some of the entries integrated login details for non-public accounts.
“The folks whose facts Pray.com experienced saved in these phonebook documents were being not application buyers,” in accordance to vpnMentor’s evaluation this 7 days. “They were only men and women whose make contact with particulars had been saved on a Pray.com user’s system. In total, we think Pray.com saved up to 10 million peoples’ non-public data without the need of their direct permission – and without the need of its buyers knowing they ended up enabling it to come about.”
Cloud Complexity
Interestingly, a very little in excess of 80,000 information ended up created private, only accessible to people today with the proper security permissions. Nonetheless, these files had been being exposed by way of a second Amazon service, vpnMentor found, demonstrating the complexity that cloud configurations can entail.
“Through even more investigation, we acquired that Pray.com had guarded some data files, placing them as non-public on the buckets to limit access,” they discussed. “However, at the exact same time, Pray.com had integrated its S3 buckets with one more AWS service, the AWS CloudFront content material delivery network (CDN). Cloudfront allows app builders to cache content on proxy servers hosted by AWS all around the earth – and nearer to an app’s customers – instead than load people data files from the app’s servers. As a result, any documents on the S3 buckets could be indirectly viewed and accessed via the CDN, no matter of their particular person security settings.”
They added, “Pray.com’s builders unintentionally created a backdoor that gave comprehensive obtain to all the files they had tried to secure.”
Chris DeRamus, vice president of technology for the Cloud Security Exercise at Quick7, observed that firms need to have to be conscious that the self-provider character of cloud opens them up to elevated risk.
“Unprotected S3 buckets and databases are a common prevalence, and a single that attackers carry on to exploit. In actuality, out of 196 breaches triggered by cloud misconfigurations in 2018 and 2019, S3 bucket misconfigurations accounted for 16 per cent of those breaches,” he stated through email. “Organizations really should choose the acceptable security measures, such as security automation, to guarantee that information is guarded at all times. If risk is not regarded and tackled to begin with, companies can face fines, authorized fees, and in the long run their viability.”
The database was learned on Oct. 6, but it was not designed non-public in spite of several tries to speak to Pray.com about the trouble, in accordance to vpnMentor. Right after the scientists contacted Amazon specifically, the contact files have been taken out from the open up bucket on Nov. 17.
Though it’s unknown how lengthy the information were being exposed, some of the knowledge dated again to 2016, scientists mentioned.
“By not preserving its users’ info – though also aggressively harvesting the facts of their mates and family – Pray.com has exposed thousands and thousands of persons to a variety of risks [like phishing, identity theft and account takeover],” in accordance to vpnMentor. “The implications for the app’s customers, and the normal general public, need to not be understated.”
Some parts of this article are sourced from:
threatpost.com

 How These 9 Startups are Thriving in the Covid-19 Economy
How These 9 Startups are Thriving in the Covid-19 Economy