Facebook has patched a bug in its extensively mounted Messenger app for Android that could have allowed a distant attacker to simply call unsuspecting targets and listen to them prior to even they picked up the audio get in touch with.
The flaw was identified and claimed to Fb by Natalie Silvanovich of Google’s Challenge Zero bug-looking team last month on October 6 with a 90-day deadline, and impacts edition 284…16.119 (and just before) of Fb Messenger for Android.
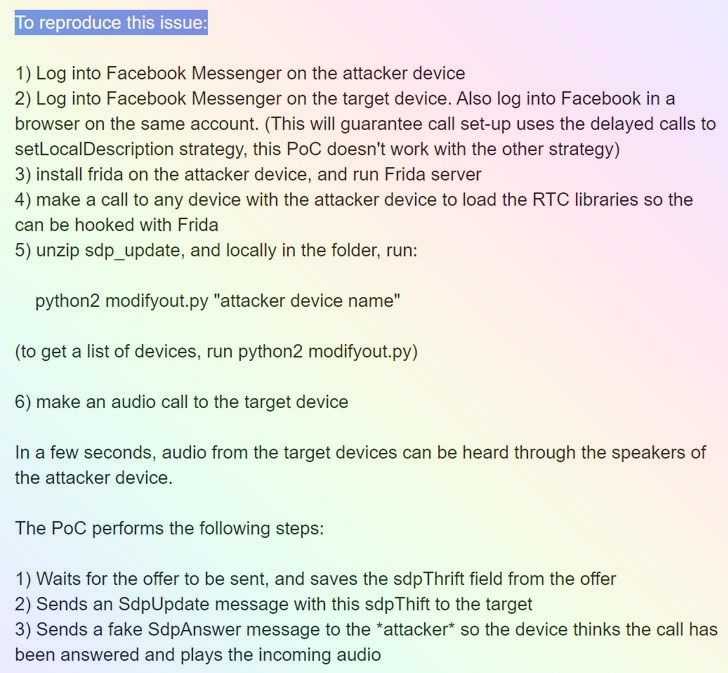
In a nutshell, the vulnerability could have granted an attacker who is logged into the app to concurrently initiate a phone and send out a specially crafted information to a target who is signed in to the two the application as well as one more Messenger customer these types of as the web browser.
“It would then trigger a situation where, when the unit is ringing, the caller would get started obtaining audio possibly until finally the man or woman being known as answers or the phone occasions out,” Facebook’s Security Engineering Manager Dan Gurfinkel mentioned.
According to a technological produce-up by Silvanovich, the flaw resides in WebRTC’s Session Description Protocol (SDP) — which defines a standardized format for the trade of streaming media amongst two endpoints — permitting an attacker to ship a distinctive variety of information identified as “SdpUpdate” that would lead to the phone to link to the callee’s unit right before staying answered.
Audio and online video calls by means of WebRTC commonly does not transmit audio right up until the receiver has clicked the acknowledge button, but if this “SdpUpdate” concept is despatched to the other conclusion system while it is ringing, “it will result in it to commence transmitting audio straight away, which could allow for an attacker to check the callee’s environment.”
In some techniques, the vulnerability bears similarity to a privacy-eroding flaw that was described in Apple’s FaceTime team chats aspect last calendar year that designed it possible for end users to initiate a FaceTime movie call and eavesdrop on targets by introducing their own number as a third person in a group chat even just before the man or woman on the other conclusion accepted the incoming simply call.
The gaffe was considered so critical that Apple pulled the plug on FaceTime team chats completely right before it resolved the issue in a subsequent iOS update.
But contrary to the FaceTime bug, exploiting the issue is just not that simple. The caller would have to presently have the permissions to contact a unique man or woman — in other words and phrases, the caller and the callee would have to be Fb mates to pull this off.
What is more, the attack also necessitates that the poor actor takes advantage of reverse engineering resources like Frida to manipulate their individual Messenger software to power it to send out the personalized “SdpUpdate” concept.
Silvanovich was awarded a $60,000 bug bounty for reporting the issue, one amongst Facebook’s a few best bug bounties to date, which the Google researcher reported she was donating to a non-revenue named GiveWell.
This not the 1st time Silvanovich has identified critical flaws in messaging apps, who has formerly unearthed a quantity of issues in WhatApp, iMessage, WeChat, Signal, and Reliance JioChat, some of which have located the “callee unit to deliver audio without person conversation.”
Found this short article interesting? Follow THN on Fb, Twitter and LinkedIn to examine more distinctive content material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Chinese Cloud Hopper Attackers Use Zerologon in New Campaign
Chinese Cloud Hopper Attackers Use Zerologon in New Campaign