Cybersecurity scientists in surplus of the weekend disclosed new security risks connected with connection previews in preferred messaging apps that bring about the skilled solutions to leak IP addresses, expose hyperlinks sent by indicates of conclusion-to-quit encrypted chats, and even unnecessarily down load gigabytes of understanding stealthily in the track history.
“Links shared in chats may well incorporate non-general public data meant only for the recipients,” scientists Talal Haj Bakry and Tommy Mysk claimed.
✔ Approved Seller by TheCyberSecurity.News
From Our Associates
Defend by yourself against all threads using F-Seure. F-Seure is one particular of the very first security corporations which has never ever been backed up by any governments. It offers you with an award-profitable security plus an optimum privateness.Get F-Secure Protected with 65% low cost from a bitdefender official seller SerialCart® (Minimal Offer).
➤ Activate Your Coupon Code
“This could be charges, contracts, health and fitness care facts, or just about everything that may properly be personal.”
“Applications that count on servers to make connection previews might possibly be violating the privacy of their individuals by sending just one-way hyperlinks shared in a non-general public chat to their servers.”
Building Internet site backlink Previews at the Sender/Receiver Element
Relationship previews are a well-liked factor in most chat purposes, developing it effortless to show a obvious preview and a transient description of the shared backlink.
Even though purposes like Signal and Wire give buyers the probability to remodel on/off url previews, a couple other individuals like Threema, TikTok, and WeChat you must not make a website website link preview at all.
The purposes that do make the previews do so quite possibly at the sender’s conclusion or the recipient’s finish or employing an exterior server which is then despatched back again to both the sender and receiver.
Sender-aspect backlink previews — utilised in Apple iMessage, Signal (if the positioning is on), Viber, and Facebook’s WhatsApp — operates by downloading the hyperlink, adopted by acquiring the preview image and summary, which is then despatched to the receiver as an attachment. When the application on the other complete receives the preview, it exhibits the concept with no opening the website hyperlink, for that reason defending the consumer from malicious a single-way one-way links.
“This procedure assumes that whoever is sending the relationship will have to perception it, taking into consideration that it will be the sender’s application that will have to open up the url,” the researchers said.
In contrast, backlink previews manufactured on the receiver side opens the doorway to new pitfalls that permits a horrible actor to gauge their approximate website without obtaining any action taken by the receiver by merely just sending a hyperlink to a server underneath their handle.
This will take position due to the simple fact the messaging software, on getting a information with a link, opens the URL mechanically to create the preview by disclosing the phone’s IP tackle in the talk to for sent to the server.
Reddit Chat and an undisclosed app, which is “in the method of fixing the issue,” were being situated to comply with this tactic, for each individual the scientists.
Building use of an Exterior Server to Supply Url Previews
And finally, the use of an external server to provide previews, although protecting against the IP tackle leakage issue, outcomes in new issues: Does the server used to produce the preview retain a copy, and if so, for how extensive, and what do they use it for?
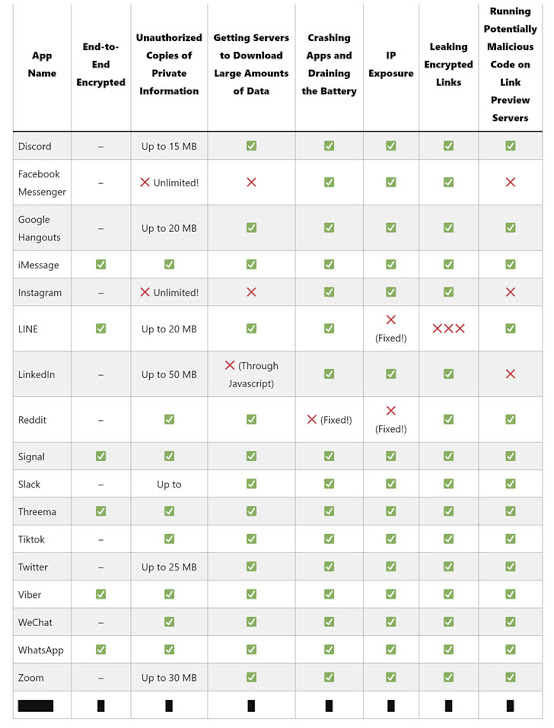
Rather a number of applications, counting Discord, Fb Messenger, Google Hangouts, Instagram, LINE, LinkedIn, Slack, Twitter, and Zoom, tumble into this group, with no indication to close people that “the servers are downloading whatsoever they come throughout in a hyperlink.”
Checks these programs learned that besides for Fb Messenger and Instagram, all other individuals imposed a 15-50 MB cap when it will appear to the data documents downloaded by their respective servers. Slack, for occasion, caches link previews for all close to 30 minutes.
The outliers, Fb Messenger and Instagram, ended up found to down load full information, even if they ran into gigabytes in measurement (this kind of as a 2.6GB file), which in accordance to Fb, is an intended function.
Even then, the scientists notify, this could be a “privacy nightmare” if the servers do keep a copy and “you can find ever a information breach of these servers.”
What’s extra, in spite of LINE’s close-to-end encryption (E2EE) factor developed to avert 3rd-activities from eavesdropping on conversations, the app’s reliance on an external server to produce website link previews allows “the LINE servers [to] know all about the inbound one-way links that are finding despatched as a result of the application, and who’s sharing which backlinks to whom.”
Backlink has mainly because up to date its FAQ to replicate that “in buy to crank out URL previews, back links shared in chats are also despatched to LINE’s servers.”
In a impartial circumstance, the researchers also identified it was possible to possible execute malicious code web-site website link preview servers, ensuing in a JavaScript code backlink shared on Instagram or LinkedIn to lead to their servers to run the code.
“We examined this by sending a backlink to a web web page on our server which contained JavaScript code that just designed a callback to our server,” they claimed. “We had been getting outfitted to validate that we experienced at least 20 seconds of execution time on these servers.”
Making an attempt to maintain in Intellect the Privacy and Security Implications
Bakry and Mysk have before uncovered flaws in TikTok that developed it attainable for attackers to exhibit display solid video clip clips, which include all those people from verified accounts, by redirecting the software to a phony server hosting a selection of forged videos. Formerly this March, the duo also uncovered a troubling privacy seize by much more than 4 dozen iOS programs that finished up noticed to accessibility users’ clipboards with out users’ express authorization.
The growth led Apple to introduce a new place in iOS 14 that alerts users just about every time an app makes an attempt to duplicate clipboard details, along with introducing new authorization that shields clipboard from unwarranted entry by 3rd-occasion apps.
“We assume you can find just one major takeaway in this write-up for builders: When you are developing a new element, generally continue to maintain in thoughts what sort of privacy and security implications it may effectively have, specifically if this purpose is likely to be used by numerous quantities or even hundreds of 1000’s of folks about the earth.”
“Backlink previews are great a attribute that purchasers frequently achieve from, but stated in this article and we’ve showcased the big array of complications this attribute can have when privateness and security fears are not thoroughly regarded.”
Found this report exciting? Abide by THN on Fb, Twitter and LinkedIn to read much more distinct details we post.
Some components of this report are sourced from:
thehackernews.com


 How Blockchain and IoT are Improving the Food Supply Chain
How Blockchain and IoT are Improving the Food Supply Chain