Cybersecurity researchers have shared information about a now-patched security flaw in Windows MSHTML platform that could be abused to bypass integrity protections on specific machines.
The vulnerability, tracked as CVE-2023-29324 (CVSS rating: 6.5), has been described as a security function bypass. It was tackled by Microsoft as portion of its Patch Tuesday updates for Might 2023.
Akamai security researcher Ben Barnea, who discovered and reported the bug, pointed out that all Windows versions are impacted, but pointed out Microsoft, Trade
servers with the March update omit the vulnerable feature.

“An unauthenticated attacker on the internet could use the vulnerability to coerce an Outlook customer to join to an attacker-managed server,” Barnea mentioned in a report shared with The Hacker News.
“This benefits in NTLM credentials theft. It is a zero-click on vulnerability, that means it can be brought on with no user interaction.”
It is really also really worth noting that CVE-2023-29324 is a bypass for a deal with Microsoft put in area in March 2023 to resolve CVE-2023-23397, a critical privilege escalation flaw in Outlook that the firm explained has been exploited by Russian threat actors in attacks aimed at European entities due to the fact April 2022.
Future WEBINARLearn to Prevent Ransomware with Genuine-Time Security
Be a part of our webinar and study how to stop ransomware assaults in their tracks with true-time MFA and company account defense.
Help save My Seat!
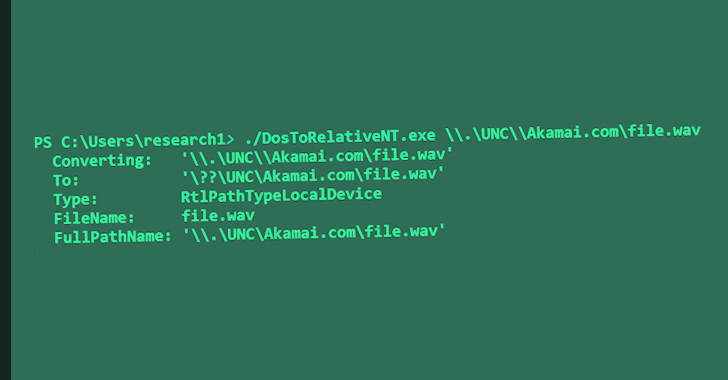
Akamai reported the issue stems from intricate managing of paths in Windows, therefore allowing a danger actor to craft a malicious URL that can sidestep internet security zone checks.
“This vulnerability is nonetheless a different illustration of patch scrutinizing foremost to new vulnerabilities and bypasses,” Barnea mentioned. “It is a zero-click media parsing attack area that could perhaps contain critical memory corruption vulnerabilities.”
In order to remain absolutely shielded, Microsoft is further recommending consumers to install Internet Explorer Cumulative updates to handle vulnerabilities in the MSHTML system and scripting engine.
Found this write-up interesting? Follow us on Twitter and LinkedIn to study a lot more exceptional written content we article.
Some parts of this article are sourced from:
thehackernews.com

 Sophisticated DownEx Malware Campaign Targeting Central Asian Governments
Sophisticated DownEx Malware Campaign Targeting Central Asian Governments