Emotet is a single of the most harmful and widespread malware threats energetic today.
Ever considering that its discovery in 2014—when Emotet was a regular credential stealer and banking Trojan, the malware has advanced into a modular, polymorphic platform for distributing other sorts of pc viruses.
Currently being frequently beneath growth, Emotet updates by itself regularly to increase stealthiness, persistence, and incorporate new spying abilities.
This notorious Trojan is one of the most commonly destructive plans observed in the wild. Generally, it is a component of a phishing attack, email spam that infects PCs with malware and spreads among other computer systems in the network.
If you would like to locate out more about the malware, collect IOCs, and get fresh new samples, check out the subsequent posting in the Malware developments tracker, the assistance with dynamic articles.
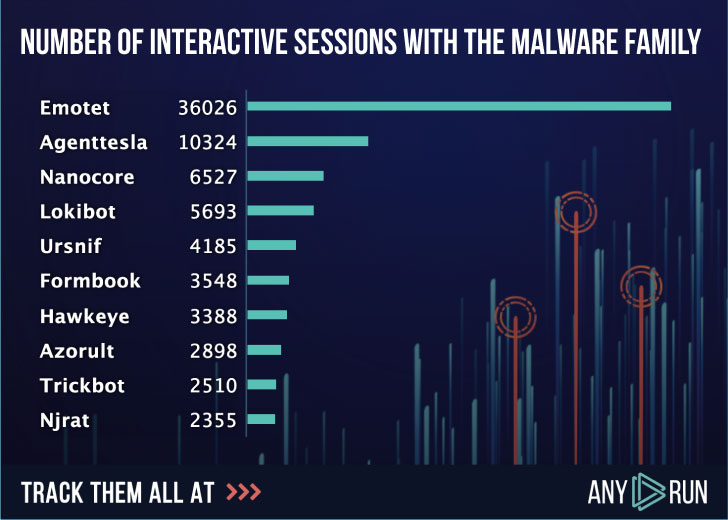
Emotet is the most uploaded malware all through the earlier few decades. Right here underneath is the rating of uploads to ANY.Operate support in 2019, where by buyers ran about 36000 interactive periods of Emotet malware examination on line.
The malware has adjusted a large amount above time, and with just about every new variation, it gets much more and extra threatening for victims. Let us have a nearer search at how it progressed.
When it was just like any other normal banking Trojan, the malware’s most important intention was to steal smaller companies’ qualifications, generally in Germany and Austria. By faking invoices or other fiscal files, it manufactured consumers click on on the one-way links and allow the malware in.
Afterwards that 12 months, it acquired a diverse modular architecture, whose most important focuses have been downloading a malware payload, spreading on to as numerous machines as doable, and sending malicious e-mail to infect other corporations.
In early 2015 immediately after a small crack, Emotet confirmed up again. The community RSA critical, new deal with lists, RC4 encryption had been among the the new options of Trojan. From this stage, the victims’ variety begun to improve — Swiss banks joined it. And all round, evasion techniques have been enhanced a large amount.
In latest variations, a major transform in the method has transpired. Emotet has turned into polymorphic malware, downloading other destructive plans to the infected pc and the full network as nicely. It steals info, adapts to various detection devices, rents the contaminated hosts to other cybercriminals as a Malware-as-a-Service design.
Given that Emotet takes advantage of stolen emails to obtain victims’ trust, spam has persistently remained the most important shipping and delivery process for Emotet—making it convincing, extremely prosperous, and dangerous.
For instance, in 2018, the governing administration process endured an Emotet infection in Allentown, a town in japanese Pennsylvania, which cost them $1 million for recovery.
The complete city of Frankfurt had to shut down the network due to the fact of Emotet in 2019. Unique forms of companies, from the govt to little businesses, all public expert services had been pressured to halt their function through IT.
According to the hottest exploration, Emotet is a throughout the world menace that has an effect on all kinds of spheres. Just seem at the next map, Italy, Spain, and the United Arab Emirates are the top rated nations with the most attacked users.
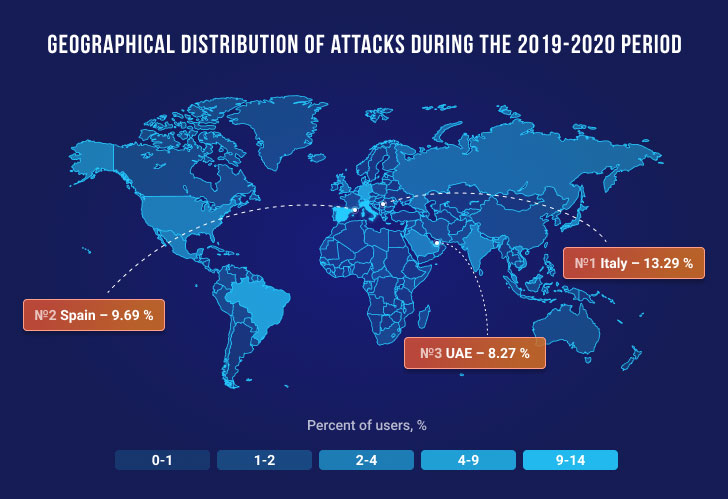
A short while ago France, Japan, and New Zealand’s cybersecurity businesses have declared a rise in Emotet assaults targeting their international locations.
Emotet then and now
According to a graph of the Emotet samples uploaded to ANY.Operate company, you can see the behavior of the malware in 2019 and 2020.
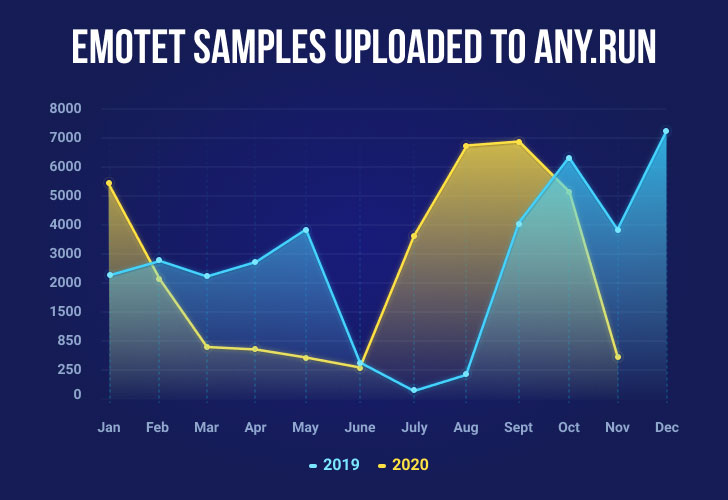
We can recognize some similarities in its activity. For illustration, in June, Emotet tends to be on the decrease. Even so, it seems to clearly show an escalating development from August until October. In 2019 the end of the year was incredibly lively for this variety of attack, so we can expect it to be on the increase this yr as very well.
Emotet has remained a threat for several years as it alterations forever. Early variations differ from the existing one, even by its intentions — Emotet has designed from the banking Trojan to the loader. When it arrives to execution evolution and document templates, we will explain only versions that occur immediately after 2018. There had been modifications even around these two several years, but the only point that remains unchanged is shipping.
For distribution and consumer execution, Emotet is using malicious spam and files with VBA macros. After a goal downloads the connected malicious files from an email and opens it, the Business document tips the person into enabling the macro. Just after that, the embedded macro starts its execution, and subsequent situations may vary. The most common variant more than the earlier a long time is that macros commence a Base64 encoded Powershell script that later on downloads an executable. But at this position, Emotet provides a large amount of various executions.
Several variants appear to its lifetime when we discuss about the first techniques after a maldoc was opened. VBA macro in Place of work files can begin cmd, Powershell, WScript, and, recently, for the very first time, Сertutil was utilized by the Emotet’s execution chain.
Other changes in the execution course of action happened in the chain involving malicious documents and dropped/downloaded executable data files.
Not only has the execution chain reworked above time, but also the Emotet’s executable file alone — registry keys, files, and boy or girl procedures in the file system. For case in point, in the 2018-2019 yrs, Emotet dropped its executable at the folder beneath a unique route and created a filename and the name of a folder working with a specific algorithm.
It transformed the file name era algorithm, method tree, and path era algorithm for C2 interaction.
Another large aspect that characterizes this malware loved ones is the maldocs’ templates it uses. They are frequently altering, and most of the time, Emotet takes advantage of its individual ones. But concerning them can also be observed templates that earlier have been used to distribute other malware family members these as Valak and Icedid.
Emotet from the ANY.RUN’s perspective
Of system, the key problem with Emotet is to come across a way to determine it and comprehend its conduct, so right after that, you could strengthen the weak factors in security.
There is a resource that can give you a hand with that. ANY.Operate is an interactive online sandbox that detects, analyzes, and displays cybersecurity threats, needed if you deal with Emotet.
Also, ANY.Operate has a particular device — the analysis of community submissions. It is a huge databases where consumers share their investigations. And fairly normally, Emotet gets the “hero” of the day: it has a major placement of the most downloaded samples into ANY.Run. Which is why ANY.RUN’s working experience with the malware is appealing.
The initial step of safeguarding your infrastructure from Emotet an infection is — detecting the malware. ANY.Operate sandbox has remarkable tools for Emotet detection and evaluation.
The on the net company specials with Emotet regularly. So, let us attempt the interactive tactic for Emotet detection and investigate one of the samples jointly:
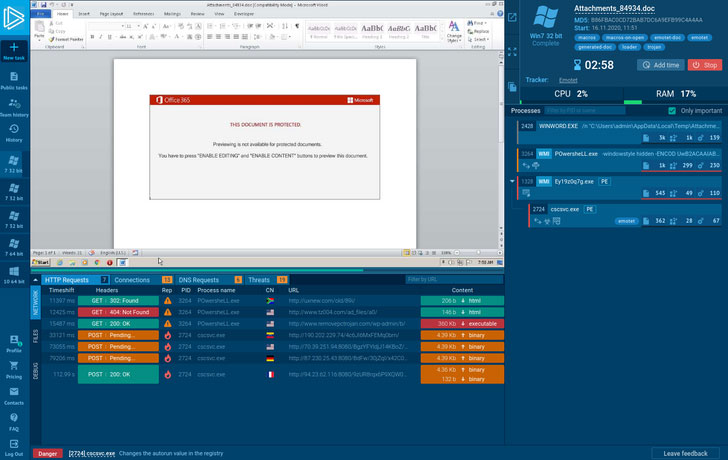
Right here is a destructive attachment from the phishing email that we uploaded to ANY.Operate and straight away get the 1st outcomes. The approach tree on the appropriate reflects all functions that have been created.
As revealed, the 1st method commences to develop new information in the user listing. Then POwersheLL.exe connects to the network and downloads executable data files from the Internet. The last just one, winhttp.exe alterations the autorun price in the registry and connects to the command-and-manage server, both of those to retrieve directions for subsequent malicious activities and exfiltrate stolen details.
And ultimately, Emotet was detected by network exercise. New Suricata rulesets from quality vendors these kinds of as Proofpoint (Rising Threats) and Favourable Technologies are a large component of the detection system.
In addition, ANY.Operate offers a beneficial Fake Net function. When turned on, it returns a 404 mistake that forces malware to reveal its C2 links that assist obtain Emotet’s IOCs extra proficiently. That helps malware analysts optimize their time as there is no require to deobfuscate it manually.
Apparently, a set of malicious files with the identical template can have embedded VBA macro, leading to generating various execution chains. All of them have the main target to trick a person who opened this maldoc to permit VBA macro.

If you’d like to take a seem at all of all those templates, just research by tag “emotet-doc” in ANY. RUN’s general public submissions — these maldocs are clustered by content material similarity.
Conclusion
This form of tendency proves that Emotet is just not likely to give up or lose the ground. Its evolution showed that the malware develops really quickly and adapts to almost everything.
If your business is related to the Internet, the risks may well be broader and deeper than you realize. Which is why it is genuine that combating subtle threats like Emotet requires a concerted effort from each people today and companies.
Also, the aim of solutions like ANY.Operate is to be informed of this kind of opportunity threats and assistance businesses figure out malware early and stay away from bacterial infections at any price tag.
Analysis and detection with ANY.Run is simple, and anybody can examine a bunch of fresh new samples every single working day.
What’s additional, the assistance is free to use and for downloading samples, and there is no doubt you can make use of ANY.Operate — just give it a check out!
Located this write-up appealing? Observe THN on Fb, Twitter and LinkedIn to read through additional distinctive information we submit.
Some parts of this article are sourced from:
thehackernews.com

 YouTube has updated its terms of service, here’s what it means for you and the content creators
YouTube has updated its terms of service, here’s what it means for you and the content creators