A totally undetectable (FUD) malware obfuscation engine named BatCloak is remaining made use of to deploy a variety of malware strains since September 2022, though persistently evading antivirus detection.
The samples grant “risk actors the means to load a lot of malware family members and exploits with simplicity through remarkably obfuscated batch data files,” Trend Micro researchers reported.
About 79.6% of the overall 784 artifacts unearthed have no-detection throughout all security options, the cybersecurity organization additional, highlighting BatCloak’s skill to circumvent traditional detection mechanisms.

The BatCloak motor forms the crux of an off-the-shelf batch file builder software referred to as Jlaive, which arrives with abilities to bypass Antimalware Scan Interface (AMSI) as well as compress and encrypt the principal payload to obtain heightened security evasion.
The open up-resource software, whilst taken down because it was designed obtainable by using GitHub and GitLab in September 2022 by a developer named ch2sh, has been marketed as an “EXE to BAT crypter.” It has considering that been cloned and modified by other actors and ported to languages this kind of as Rust.
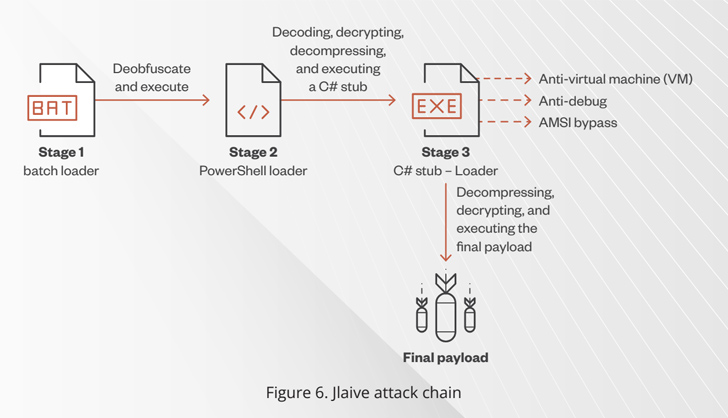
The remaining payload is encapsulated working with a few loader layers – a C# loader, a PowerShell loader, and a batch loader – the final of which functions as a starting stage to decode and unpack every single stage and finally detonate the hid malware.
“The batch loader contains an obfuscated PowerShell loader and an encrypted C# stub binary,” researchers Peter Girnus and Aliakbar Zahravi mentioned. “In the stop, Jlaive makes use of BatCloak as a file obfuscation motor to obfuscate the batch loader and save it on a disk.”
BatCloak is said to have obtained many updates and diversifications given that its emergence in the wild, its most new variation remaining ScrubCrypt, which was initially highlighted by Fortinet FortiGuard Labs in link with a cryptojacking operation mounted by the 8220 Gang.
Upcoming WEBINAR🔐 Mastering API Security: Understanding Your Accurate Attack Surface area
Uncover the untapped vulnerabilities in your API ecosystem and take proactive methods towards ironclad security. Be a part of our insightful webinar!
Be part of the Session.wn-button,.wn-label,.wn-label:immediately afterexhibit:inline-block.check_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px good #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-leading-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-suitable-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-fat:600letter-spacing:.6pxcolor:#596cec.wn-label:afterwidth:50pxheight:6pxcontent:”border-top:2px reliable #d9deffmargin: 8px.wn-titlefont-dimensions:21pxpadding:10px 0font-fat:900textual content-align:leftline-peak:33px.wn-descriptiontext-align:leftfont-sizing:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-measurement:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-excess weight:500letter-spacing:.2px
“The decision to changeover from an open up-resource framework to a closed-source design, taken by the developer of ScrubCrypt, can be attributed to the achievements of prior assignments these as Jlaive, as properly as the wish to monetize the job and safeguard it against unauthorized replication,” the scientists reported.
What is far more, ScrubCrypt is intended to be interoperable with many perfectly-acknowledged malware people like Amadey, AsyncRAT, DarkCrystal RAT, Pure Miner, Quasar RAT, RedLine Stealer, Remcos RAT, SmokeLoader, VenomRAT, and Warzone RAT.
“The evolution of BatCloak underscores the adaptability and adaptability of this engine and highlights the enhancement of FUD batch obfuscators,” the scientists concluded. “This showcases the presence of this system throughout the modern risk landscape.”
Observed this report fascinating? Observe us on Twitter and LinkedIn to browse much more exceptional information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Hackers Impersonate Journalists to Steal Millions via Twitter and Discord
Hackers Impersonate Journalists to Steal Millions via Twitter and Discord