The Personal computer Unexpected emergency Response Crew of Ukraine (CERT-UA) has warned of cyber attacks focusing on point out bodies in the state as section of an espionage campaign.
The intrusion established, attributed to a threat actor tracked by the authority as UAC-0063 due to the fact 2021, leverages phishing lures to deploy a variety of malicious equipment on contaminated techniques. The origins of the hacking crew are presently unidentified.
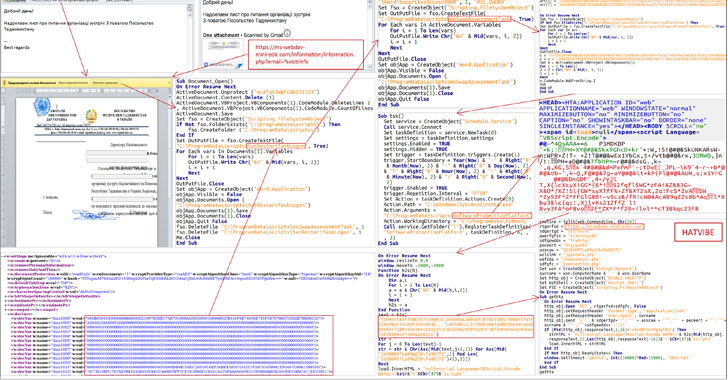
In the attack chain explained by the agency, the emails targeted an unspecified ministry and purported to be from the Embassy of Tajikistan in Ukraine. It can be suspected that the messages had been despatched from a previously compromised mailbox.
The emails arrive attached with a Microsoft Phrase doc that, on enabling macros, launches an encoded VBScript referred to as HATVIBE, which is then made use of to fall extra malware.
This incorporates a keylogger (LOGPIE), a Python-dependent backdoor able of operating instructions sent from a distant server (CHERRYSPY), and a resource centered on exfiltrating files with certain extensions (STILLARCH or DownEx).
It is truly worth noting that DownEx was a short while ago documented by Bitdefender as getting applied by an not known actor in very qualified assaults aimed at authorities entities in Kazakhstan and Afghanistan.
“Extra review of the infrastructure and connected data files created it possible to conclude that amid the objects of curiosity of the team are companies from Mongolia, Kazakhstan, Kyrgyzstan, Israel, [and] India,” CERT-UA explained.
The findings present that some risk actors are nonetheless utilizing macro-primarily based malware even with Microsoft disabling the element by default in Business documents downloaded from the web.
That mentioned, Microsoft’s constraints have led many attack groups to experiment and adapt their attack chains and payload delivery mechanisms to include unusual file sorts (CHM, ISO, LNK, VHD, XLL, and WSF) and strategies like HTML smuggling.
Approaching WEBINARZero Believe in + Deception: Master How to Outsmart Attackers!
Find how Deception can detect state-of-the-art threats, quit lateral motion, and enhance your Zero Trust technique. Be part of our insightful webinar!
Help you save My Seat!
Enterprise security firm Proofpoint stated it observed several original entry brokers (IABs) – actors who infiltrate significant targets and then promote that access to other cybercriminals for profit – applying PDF and OneNote data files starting off in December 2022.
“The experimentation with and regular pivoting to new payload supply strategies by tracked danger actors, specifically IABs, is vastly diverse from attack chains observed prior to 2022 and heralds a new normal of menace action,” the company mentioned.
“No for a longer time are the most skilled cybercriminal actors relying on 1 or a several techniques, but fairly are frequently establishing and iterating new TTPs. The swift charge of adjust for numerous menace actors implies they have the time, capacity, and understanding of the risk landscape to speedily establish and execute new tactics.”
Discovered this report exciting? Adhere to us on Twitter and LinkedIn to read additional exclusive articles we post.
Some parts of this article are sourced from:
thehackernews.com

 Fata Morgana Watering Hole Attack Targets Shipping, Logistics Firms
Fata Morgana Watering Hole Attack Targets Shipping, Logistics Firms