4 security vulnerabilities have been uncovered in the Sage X3 company useful resource scheduling (ERP) product, two of which could be chained alongside one another as section of an attack sequence to help adversaries to execute destructive commands and take manage of susceptible techniques.
These issues have been identified by scientists from Rapid7, who notified Sage Group of their results on Feb. 3, 2021. The vendor has considering that rolled out fixes in latest releases for Sage X3 Edition 9 (Syracuse 9.22.7.2), Sage X3 HR & Payroll Model 9 (Syracuse 9.24.1.3), Sage X3 Variation 11 (Syracuse 11.25.2.6), and Sage X3 Variation 12 (Syracuse 12.10.2.8) that ended up shipped in March.

The record of vulnerabilities is as follows –
- CVE-2020-7388 (CVSS score: 10.) – Sage X3 Unauthenticated Distant Command Execution (RCE) as Technique in AdxDSrv.exe element
- CVE-2020-7389 (CVSS rating” 5.5) – Program “CHAINE” Variable Script Command Injection (No repair planned)
- CVE-2020-7387 (CVSS score: 5.3) – Sage X3 Installation Pathname Disclosure
- CVE-2020-7390 (CVSS rating: 4.6) – Saved XSS Vulnerability on ‘Edit’ Web site of Person Profile
“When combining CVE-2020-7387 and CVE-2020-7388, an attacker can 1st understand the installation path of the influenced software program, then use that data to pass instructions to the host procedure to be run in the Process context,” the researchers said. “This can make it possible for an attacker to run arbitrary functioning method instructions to build Administrator stage people, put in destructive software program, and normally just take comprehensive command of the procedure for any purpose.”
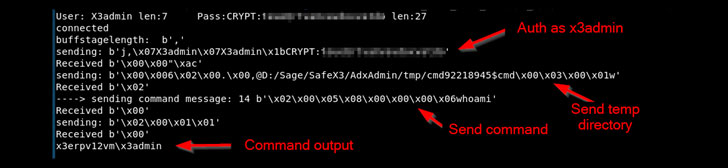
The most intense of the issues is CVE-2020-7388, which can take benefit of an administrative services that’s available over the internet to craft destructive requests with the purpose of working arbitrary instructions on the server as the “NT AUTHORITY/Method” consumer. The service in question is utilized for distant management of the Sage ERP option by means of the Sage X3 Console.

Separately, the ‘Edit’ web page linked with person profiles in the Sage X3 Syracuse web server ingredient is susceptible to a saved XSS attack (CVE-2020-7390), enabling the execution of arbitrary JavaScript code through ‘mouseOver’ occasions in the ‘First name’, ‘Last name’, and ‘Email’ fields.
“If profitable, even so, this vulnerability could allow a normal person of Sage X3 to execute privileged functions as a at the moment logged-in administrator or capture administrator session cookies for afterwards impersonation as a at the moment-logged-in administrator,” the researchers claimed.
Profitable exploitation of CVE-2020-7387, on the other hand, outcomes in the publicity of Sage X3 installation paths to an unauthorized user, when CVE-2020-7389 worries a lacking authentication in Syracuse enhancement environments that could be employed to achieve code execution by using command injection.
“Usually talking, Sage X3 installations need to not be exposed directly to the internet, and should really as a substitute be built accessible through a safe VPN relationship wherever needed,” the researchers mentioned in the disclosure. “Adhering to this operational tips properly mitigates all four vulnerabilities, nevertheless customers are continue to urged to update according to their regular patch cycle schedules.”
Uncovered this short article interesting? Comply with THN on Fb, Twitter and LinkedIn to read much more exceptional information we post.
Some parts of this article are sourced from:
thehackernews.com

 Google Meet gets fun filters and masks on iOS and Android
Google Meet gets fun filters and masks on iOS and Android