A suspected China-nexus threat actor dubbed UNC4841 has been joined to the exploitation of a recently patched zero-day flaw in Barracuda Email Security Gateway (ESG) appliances given that October 2022.
“UNC4841 is an espionage actor powering this huge-ranging campaign in support of the People’s Republic of China,” Google-owned Mandiant mentioned in a new report printed nowadays, describing the team as “intense and qualified.”
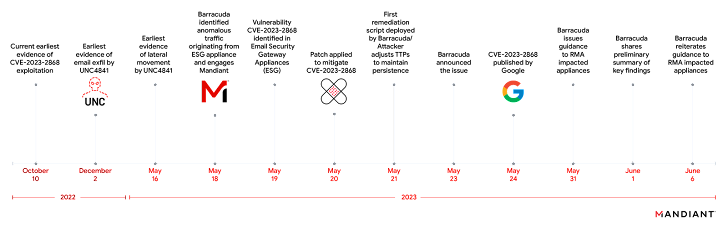
The flaw in problem is CVE-2023-2868 (CVSS rating: 9.8), which relates to a distant code injection influencing variations 5.1.3.001 via 9.2..006 that arises as a outcome of an incomplete validation of attachments contained in incoming e-mail.

Barracuda addressed the challenge on May possibly 20 and 21, 2023, but the enterprise has considering the fact that urged affected buyers to straight away swap the units “no matter of patch model stage.”
Now in accordance to the incident response and threat intelligence company, which was appointed to probe the hack, UNC4841 is stated to have sent e-mail to victim companies that contains destructive TAR file attachments that have been developed to exploit the bug as early as Oct 10, 2022.
These email messages contained generic lures with bad grammar and, in some cases, placeholder values, a tactic intentionally selected to disguise the communications as spam.
The intention, it noted, was to execute a reverse shell payload on the focused ESG units and deliver 3 different malware strains – SALTWATER, SEASIDE, and SEASPY – in buy to set up persistence and execute arbitrary commands, while masquerading them as legit Barracuda ESG modules or companies.
Also deployed by the adversary is a kernel rootkit named SANDBAR that’s configured to conceal processes that begin with a specified name as effectively as trojanized variations of two distinct valid Barracuda Lua modules –
- SEASPRAY – A launcher for screening incoming email attachments with a individual filename and runs an external C-centered utility dubbed WHIRLPOOL to make a TLS reverse shell
- SKIPJACK – A passive implant that listens for incoming email headers and subjects and executes the information current in “Material-ID” header field
Source code overlaps have been identified involving SEASPY and a publicly offered backdoor referred to as cd00r and also between SANDBAR and an open-resource rootkit, suggesting that the actor repurposed existing tools to orchestrate the intrusions.
Approaching WEBINAR🔐 Mastering API Security: Knowledge Your Genuine Attack Floor
Uncover the untapped vulnerabilities in your API ecosystem and get proactive actions in the direction of ironclad security. Be a part of our insightful webinar!
Sign up for the Session.wn-button,.wn-label,.wn-label:followingdisplay screen:inline-block.check out_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-top rated-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-right-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-measurement:13pxmargin:20px 0font-bodyweight:600letter-spacing:.6pxcolor:#596cec.wn-label:followingwidth:50pxheight:6pxcontent:”border-best:2px stable #d9deffmargin: 8px.wn-titlefont-dimensions:21pxpadding:10px 0font-excess weight:900text-align:leftline-peak:33px.wn-descriptiontextual content-align:leftfont-measurement:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
UNC4841 has all the hallmarks of a persistent actor, supplied its means to quickly alter its malware and employ extra persistence mechanisms as Barracuda initiated containment attempts soon after finding the exercise on May well 19, 2023.
In some scenarios, the risk actor was observed leveraging entry to a compromised ESG equipment to perform lateral movement into the sufferer network, or to send mail to other sufferer appliances. Details exfiltration entailed the seize of email related knowledge in a subset of scenarios.
The superior frequency attacks, Mandiant mentioned, focused an unspecified selection of private and public sector businesses positioned in at minimum 16 countries, with practically a 3rd being federal government entities. 55% of the impacted organizations are located in the Americas, followed by 24% in EMEA and 22% in the Asia-Pacific area.
“UNC4841 has shown to be remarkably responsive to defensive attempts and actively modifies TTPs to sustain their operations,” Mandiant reported, including it expects the actors to “change their TTPs and modify their toolkit.”
Located this post fascinating? Adhere to us on Twitter and LinkedIn to go through extra unique material we publish.
Some parts of this article are sourced from:
thehackernews.com


 #InfosecurityEurope: EMEA Retailers Experience Surge in Web Attacks, With Germany Heavily Targeted
#InfosecurityEurope: EMEA Retailers Experience Surge in Web Attacks, With Germany Heavily Targeted