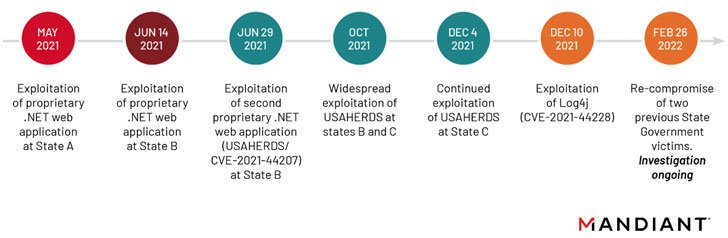
APT41, the condition-sponsored menace actor affiliated with China, breached at minimum 6 U.S. point out federal government networks involving May perhaps 2021 and February 2022 by retooling its attack vectors to get gain of susceptible internet-facing web applications.
The exploited vulnerabilities involved “a zero-day vulnerability in the USAHERDS application (CVE-2021-44207) as properly as the now notorious zero-working day in Log4j (CVE-2021-44228),” scientists from Mandiant stated in a report posted Tuesday, calling it a “deliberate campaign.”
In addition to web compromises, the persistent assaults also involved the weaponization of exploiting deserialization, SQL injection, and listing traversal vulnerabilities, the cybersecurity and incident response agency pointed out.
The prolific superior persistent menace, also regarded by the monikers Barium and Winnti, has a keep track of report of focusing on companies in both equally the public and personal sectors to orchestrate espionage action in parallel with fiscally inspired functions.

In early 2020, the group was joined to a world intrusion campaign that leveraged a variety of exploits involving Citrix NetScaler/ADC, Cisco routers, and Zoho ManageEngine Desktop Central to strike dozens of entities in 20 international locations with destructive payloads.
The newest disclosure carries on the development of APT41 immediately co-opting recently disclosed vulnerabilities this sort of as Log4Shell to gain initial obtain into goal networks of two U.S. condition governments together with insurance policy and telecom companies inside hrs of it turning into community expertise.
The intrusions ongoing well into February 2022 when the hacking crew re-compromised two U.S. condition governing administration victims that have been infiltrated for the to start with time in May well and June 2021, “demonstrating their unceasing drive to obtain state governing administration networks,” the scientists claimed.
What’s more, the foothold founded right after the exploitation of Log4Shell resulted in the deployment of a new variant of a modular C++ backdoor known as KEYPLUG on Linux techniques, but not in advance of performing comprehensive reconnaissance and credential harvesting of the focus on environments.
Also noticed during the attacks had been an in-memory dropper identified as DUSTPAN (aka StealthVector) which is orchestrated to execute the subsequent-stage payload, alongside innovative put up-compromise applications like DEADEYE, a malware loader which is dependable for launching the LOWKEY implant.
Main between the range of techniques, evasion solutions, and abilities made use of by APT41 concerned the “substantially greater” utilization of Cloudflare providers for command-and-command (C2) communications and data exfiltration, the researchers claimed.
While Mandiant famous it found evidence of the adversaries exfiltrating personally identifiable information and facts that’s ordinarily in line with an espionage procedure, the final intention of the campaign is at present unclear.
The results also mark the 2nd time a Chinese country-state team has abused security flaws in the ubiquitous Apache Log4j library to penetrate targets.
In January 2022, Microsoft in-depth an attack campaign mounted by Hafnium – the risk actor powering the prevalent exploitation of Trade Server flaws a yr in the past – that utilized the vulnerability to “attack virtualization infrastructure to lengthen their standard focusing on.”

If everything, the latest actions are however yet another sign of a consistently adapting adversary which is able of shifting its goalposts as properly as refine its malware arsenal to strike entities all over the planet that are of strategic desire.
APT41’s cyber functions towards healthcare, significant-tech, and telecommunications sectors above the decades have due to the fact caught the notice of the U.S. Justice Department, which issued charges versus five associates of the group in 2020, landing the hackers a area on the FBI’s cyber most required checklist.
“APT41 can quickly adapt their first access methods by re-compromising an natural environment as a result of a distinct vector, or by rapidly operationalizing a contemporary vulnerability,” the researchers mentioned. “The group also demonstrates a willingness to retool and deploy abilities by new attack vectors as opposed to keeping on to them for foreseeable future use.”
In a connected enhancement, Google’s Risk Evaluation Team claimed it took techniques to block a phishing marketing campaign staged by an additional Chinese state-backed group tracked as APT31 (aka Zirconium) final month that was aimed at “high profile Gmail users affiliated with the U.S. govt.”
Discovered this article interesting? Comply with THN on Facebook, Twitter and LinkedIn to browse a lot more exclusive information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Critical RCE Bugs Found in Pascom Cloud Phone System Used by Businesses
Critical RCE Bugs Found in Pascom Cloud Phone System Used by Businesses