The Ragnar Locker operators produced a stolen deal amongst Wild Turkey and actor Matthew McConaughey, as evidence of compromise.
Italian spirits brand Campari has restored its enterprise internet site following a the latest ransomware attack. According to the ransom take note, the team driving the breach employed Ragnar Locker to encrypt most of Campari’s servers and was holding the facts hostage for $15 million in Bitcoin.
Campari Team is behind liquor models Aperol, SKYY, Grand Marnier and Wild Turkey. The firm announced on Nov. 3 it was the target of a Nov. 1 malware attack.
“The group’s IT division, with the assist of IT security gurus, instantly took motion to restrict the distribute of malware in info and programs,” the Campari Group statement said. “Therefore, the corporation has implemented a short-term suspension of IT solutions, as some techniques have been isolated in order to allow their sanitation and progressive restart in safe situations for a well timed restoration of everyday functions. At the very same time, an investigation into the attack was launched, which is still ongoing. It is considered that the non permanent suspension of the IT systems are not able to have any important effect on the Group’s outcomes.”
The Ransom Take note
Malware researcher Pancak3 shared a duplicate of the ransom observe with Threatpost.
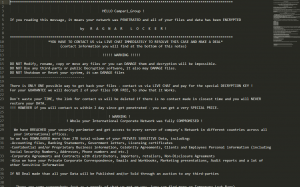
The ransom be aware. Source: Pancak3.
“We have BREACHED your security perimeter and get [sic] accessibility to just about every server of the company’s network in unique international locations across all your international offices,” the be aware reads, in element. It goes on to element the sorts of details compromised, which includes accounting data files, lender statements, staff particular facts and additional. The observe mentioned the scammers were ready to steal a complete of 2TB of data.
“If no offer is built than [sic] all your info with be printed and/or sold as a result of an auction to any 3rd functions,” the be aware threatens.
Compromised files posted on a leak web site for the team incorporated a agreement in between Wild Turkey and actor Matthew McConaughey, in accordance to ZDNet, as proof they had the goods.
Campari Group has not responded to Threatpost’s ask for for remark.
Increase of Ragnar Locker Ransomware
“The operators are specialists,” Pancak3 informed Threatpost. “They have fantastic expertise of penetration ways that allow them to get original entry, complete recon, and steal data prior to deploying their ransomware. Back in April they initially started out their community shaming internet site, “WALL OF Shame,” to put up aspects of non-paying out victims. It is believed that Ragnar Locker partnered with Maze operators previously this calendar year.”
Ragnar Locker ransomware, Pancak3 extra, is a reasonably new malware prepared in C and C++.
“(It was) initially was observed in late 2019,” Pancak3 discussed. “Ragnar Locker allows operators to personalize the way it behaves on the contaminated host.”
The Capari compromise appears to be like just about identical to the Capcom Ragnar Locker attack, in accordance to Pancak3.
In that attack, Ragnar Locker was also reportedly made use of this week to attack Japanese gaming juggernaut Capcom, to steal facts from networks in the U.S., Japan and Canada. And Pancak3 found some similarities amongst the two assaults.
“The executables for each Capcom and Campari are signed with the similar cert.,” he advised Threatpost. Introducing, it demonstrates that the group is obtaining a little bit complacent.
“I feel it exhibits that they are assured in their intrusion approaches,” Pancak3 stated.
Ransomware assaults have been on the rise considering that the commencing of the pandemic very last spring. Very last July, SonicWall’s 2020 Cyber Danger Report mentioned ransomware attacks have a lot more than doubled around very last 12 months.
“As we have seen with Campari and lots of other folks, ransomware continues to be a considerable menace to businesses large and little,” Wade Lance, CTO at Illusive Networks mentioned through email. “Cybercriminals only have to have to get lucky after when they attack with ransomware to be profitable. On the other hand, big companies need to cease every single attempted cyberattack aimed at them, and if they are erroneous even the moment the repercussions are catastrophic.”
Hackers Put Bullseye on Healthcare: On Nov. 18 at 2 p.m. EDT find out why hospitals are receiving hammered by ransomware assaults in 2020. Save your spot for this Absolutely free webinar on health care cybersecurity priorities and hear from primary security voices on how info security, ransomware and patching need to be a priority for every sector, and why. Join us Wed., Nov. 18, 2-3 p.m. EDT for this LIVE, minimal-engagement webinar.
Some parts of this article are sourced from:
threatpost.com


 #COVID19 Themed Attacks Surge by 605% in Q2
#COVID19 Themed Attacks Surge by 605% in Q2