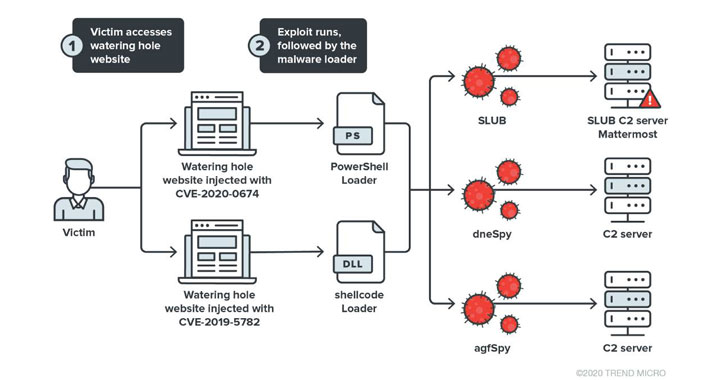
Cybersecurity scientists have disclosed particulars about a new watering gap attack concentrating on the Korean diaspora that exploits vulnerabilities in web browsers these kinds of as Google Chrome and Internet Explorer to deploy malware for espionage purposes.
Dubbed “Operation Earth Kitsune” by Trend Micro, the campaign entails the use of SLUB (for SLack and githUB) malware and two new backdoors — dneSpy and agfSpy — to exfiltrate method info and get added manage of the compromised device.
The attacks have been observed all through the months of March, May well, and September, in accordance to the cybersecurity organization.
Watering hole attacks enable a undesirable actor to compromise a targeted enterprise by compromising a cautiously chosen website by inserting an exploit with an intention to attain entry to the victim’s product and infect it with malware.
Procedure Earth Kitsune is stated to have deployed the adware samples on internet websites connected with North Korea, even though obtain to these internet sites is blocked for people originating from South Korean IP addresses.
A Diversified Campaign
While former operations involving SLUB utilized the GitHub repository platform to down load malicious code snippets on to the Windows process and submit the effects of the execution to an attacker-controlled personal Slack channel, the latest iteration of the malware has specific Mattermost, a Slack-like open-supply collaborative messaging procedure.
“The marketing campaign is incredibly diversified, deploying many samples to the sufferer devices and working with various command-and-manage (C&C) servers during this procedure,” Trend Micro claimed. “In overall, we located the campaign employing 5 C&C servers, seven samples, and exploits for 4 N-day bugs.”

Made to skip units that have security software mounted on them as a suggests to thwart detection, the attack weaponizes an presently patched Chrome vulnerability (CVE-2019-5782) that will allow an attacker to execute arbitrary code inside of a sandbox by using a specifically-crafted HTML page.
Independently, a vulnerability in Internet Explorer (CVE-2020-0674) was also used to supply malware by using the compromised websites.
dneSpy and agfSpy — Thoroughly Useful Espionage Backdoors
The difference in the an infection vector notwithstanding, the exploit chain proceeds as a result of the exact same sequence of methods — initiate a relationship with the C&C server, acquire the dropper, which then checks for the existence of anti-malware answers on the target program before proceeding to download the 3 backdoor samples (in “.jpg” format) and executing them.
What is adjusted this time close to is the use of Mattermost server to hold keep track of of the deployment throughout multiple infected equipment, in addition to building an unique channel for each device to retrieve the collected info from the contaminated host.
Of the other two backdoors, dneSpy, and agfSpy, the former is engineered to amass process info, seize screenshots, and obtain and execute malicious instructions obtained from the C&C server, the success of which are zipped, encrypted, and exfiltrated to the server.
“A single appealing facet of dneSpy’s style and design is its C&C pivoting habits,” Pattern Micro scientists reported. “The central C&C server’s response is really the following-phase C&C server’s domain/IP, which dneSpy has to converse with to obtain even more guidelines.”
agfSpy, dneSpy’s counterpart, arrives with its individual C&C server mechanism that it works by using to fetch shell commands and deliver the execution effects back again. Chief among the its functions include things like the functionality to enumerate directories and list, add, download, and execute files.
“Procedure Earth Kitsune turned out to be intricate and prolific, many thanks to the assortment of parts it makes use of and the interactions amongst them,” the researchers concluded. “The campaign’s use of new samples to keep away from detection by security products is also quite notable.”
“From the Chrome exploit shellcode to the agfSpy, aspects in the operation are customized coded, indicating that there is a group behind this operation. This group looks to be very energetic this 12 months, and we forecast that they will continue on going in this path for some time.”
Discovered this short article fascinating? Abide by THN on Facebook, Twitter and LinkedIn to browse far more exceptional articles we article.
Some parts of this article are sourced from:
thehackernews.com

 Canalys: Samsung lead smartphone market in Q3, Xiaomi overtook Apple
Canalys: Samsung lead smartphone market in Q3, Xiaomi overtook Apple