Email phishing attacks have been on the rise in the course of the COVID-19 pandemic this 12 months. Today’s columnist, Kevin O’Brien of GreatHorn, offers a four-step email security technique. (Credit rating: GreatHorn)
Companies of all dimensions face the similar extremely challenging obstacle: the undesirable fellas will usually test to attack email.
End users functioning on any email platform have to communicate correctly and securely when supporting their group fight from phishing, account takeovers, info breaches, and business email compromises. Corporations can do this by creating a multi-layered technique to security that absolutely everyone understands and understands like a next language.
All those who never benefit email security are very likely missing out on alternatives to shield the business and educate workers on how to do the same. Our 2020 Phishing Attack Landscape report located that 38 per cent of organizations claimed in the past yr, anyone in their firm experienced fallen sufferer to a phishing attack. And 53 p.c of corporations mentioned they experienced viewed an uptick in email phishing assaults throughout the COVID-19 pandemic.
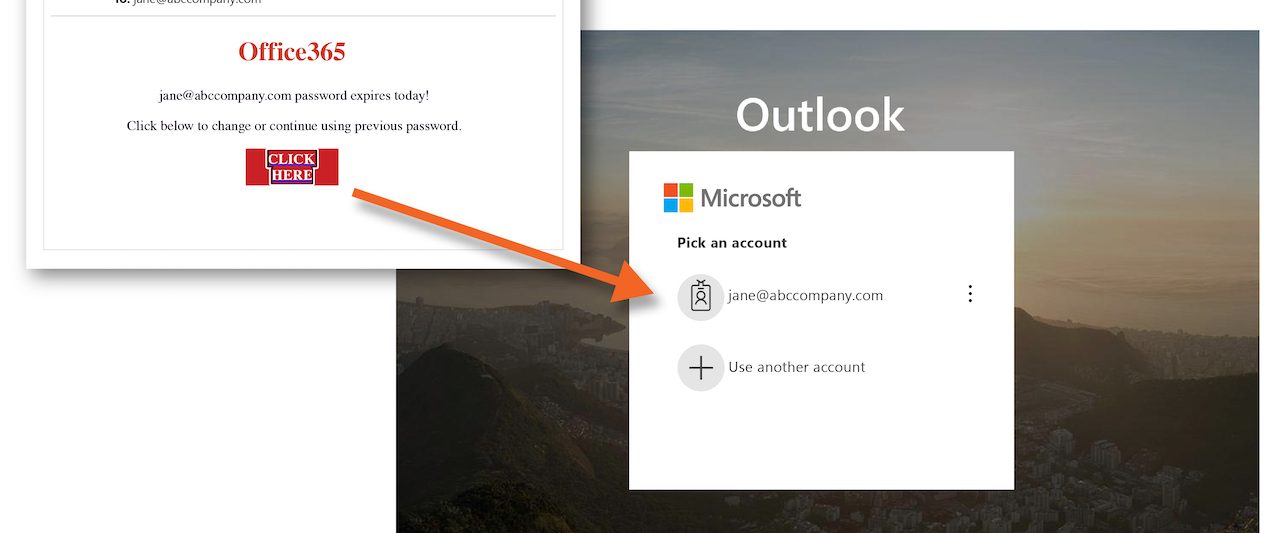
Though email compromise methods stay the exact – stealing credentials, pretending to be an individual actual, and impersonating domains/organizations – the charge at which they are going on raises. When a threat gets delivered by way of email, security teams will have to react rapidly to mitigate that attack prior to it will cause hurt that usually takes time and methods to comprise and get less than regulate. Automating the reaction and guaranteeing workforce know how to realize and do this at a moment’s see can enable mitigate threats at scale.
But what makes an email security product helpful? It revolves arounds 4 essential tenets: assess, detect, guard, and respond.
Analyze
Commence by establishing a deep knowledge of the organization’s natural environment. This consists of consumers, conversation styles, romance toughness concerning senders and recipients, assets, individual person risk profiles, and articles. Security groups ought to get complete visibility of these factual features and how, the place and to whom they hook up.
Acquiring the most reality-centered facts out there helps to review and make informed selections close to related behaviors. Without having very clear visibility, it gets additional tricky to detect and identify what steps to acquire. Numerous vendors make a “black box” of their guidelines. This would make it even a lot more difficult for organizations to have full visibility. This lack of transparency eliminates the capacity for organizations to refine guidelines, based mostly on granular risk elements, to make the very best detection for their corporation.
Detect
Security teams will have to detect an attack promptly and also evaluate it to prevent other such attacks and quarantine attacks promptly, blocking them right before they get to the conclusion user. As an illustration, adaptive threat analytics units include machine mastering and knowledge science to understand the most frequent communication styles exceptional to every single receiver and sender. When security groups do this, it is considerably much easier to detect email anomalies and suspicious material. It’s critical to catch and halt events in serious-time and avoid them from turning into even worse.
Guard
Security teams also need to have to acquire and employ devices and processes to help restrict accesses and mitigate possible incidents. This commences with in-the-minute training, and lessening attack engagement by warning users of probable threats in the course of the attack. Evaluation will become significant right here and publish-shipping to assist end users recognize what the attack, how to report phishing attempts, and how to stop it in the future.
In the protect section, security professionals keep track of network obtain and established up processes to ensure the appropriate email network configurations are in spot for the general protection of the firm. Recognition schooling or person education plays a especially major purpose below because when it will come to a phishing attack and spoofing email, we do not know what we do not know. Personnel are typically the most critical asset to defending the firm if they are trained effectively.
React
In the occasion of an email attack, the organization ought to answer swiftly to mitigate these threats. Security pros do this by automating incident reaction and remediation procedures. Having this variety of plan in position places the business in a better situation to act quickly in the celebration of an attack and limit the effects. Supplied the style of assaults, attackers can launch in a make a difference of minutes, security teams never have substantially time to manually mitigate threats.
Create a reaction plan that identifies the most handy info immediately and carry out all subsequent functions in a way that eliminates any negative consequences and assures lessons are acquired and principles applied into the long term reaction plan.
This 4-period process can aid security teams create an productive email security system. The ability to assess, detect, safeguard and react at the moment of risk aids security groups follow a truth-based mostly solution to email security. Guaranteeing the crew has a deep being familiar with of the company’s risk profile and is aware the company’s all round security posture can assist the security group join to company processes that decrease risk.
Kevin O’Brien, co-founder and CEO, GreatHorn
Some parts of this article are sourced from:
www.scmagazine.com

 How to choose a next-gen game console
How to choose a next-gen game console