A stealthy Unified Extensible Firmware Interface (UEFI) bootkit referred to as BlackLotus has turn into the very first publicly recognized malware able of bypassing Safe Boot defenses, generating it a powerful risk in the cyber landscape.
“This bootkit can operate even on absolutely up-to-date Windows 11 systems with UEFI Secure Boot enabled,” Slovak cybersecurity company ESET mentioned in a report shared with The Hacker News.
UEFI bootkits are deployed in the technique firmware and allow for total handle over the working process (OS) boot approach, thereby generating it doable to disable OS-stage security mechanisms and deploy arbitrary payloads all through startup with substantial privileges.
Offered for sale at $5,000 (and $200 for each new subsequent variation), the strong and persistent toolkit is programmed in Assembly and C and is 80 kilobytes in sizing. It also features geofencing capabilities to keep away from infecting computers in Armenia, Belarus, Kazakhstan, Moldova, Romania, Russia, and Ukraine.
Information about BlackLotus very first emerged in October 2022, with Kaspersky security researcher Sergey Lozhkin describing it as a complex crimeware solution.
“This represents a bit of a ‘leap’ forward, in conditions of simplicity of use, scalability, accessibility, and most importantly, the opportunity for considerably a lot more affect in the kinds of persistence, evasion, and/or destruction,” Eclypsium’s Scott Scheferman pointed out.
BlackLotus, in a nutshell, exploits a security flaw tracked as CVE-2022-21894 (aka Baton Fall) to get around UEFI Safe Boot protections and established up persistence. The vulnerability was addressed by Microsoft as section of its January 2022 Patch Tuesday update.
A effective exploitation of the flaw makes it possible for arbitrary code execution during early boot phases, allowing a menace actor to have out destructive actions on a method with UEFI Protected Boot enabled with out acquiring actual physical accessibility to it, ESET mentioned.
“This is the initial publicly recognized, in-the-wild abuse of this vulnerability,” ESET researcher Martin Smolár explained. “Its exploitation is even now attainable as the affected, validly signed binaries have however not been extra to the UEFI revocation list.”
“BlackLotus normally takes benefit of this, bringing its possess copies of legit – but susceptible – binaries to the system in purchase to exploit the vulnerability,” correctly paving the way for Provide Your Very own Vulnerable Driver (BYOVD) attacks.
Other than currently being outfitted to transform off security mechanisms like BitLocker, Hypervisor-secured Code Integrity (HVCI), and Windows Defender, it really is also engineered to drop a kernel driver and an HTTP downloader that communicates with a command-and-manage (C2) server to retrieve more user-manner or kernel-manner malware.
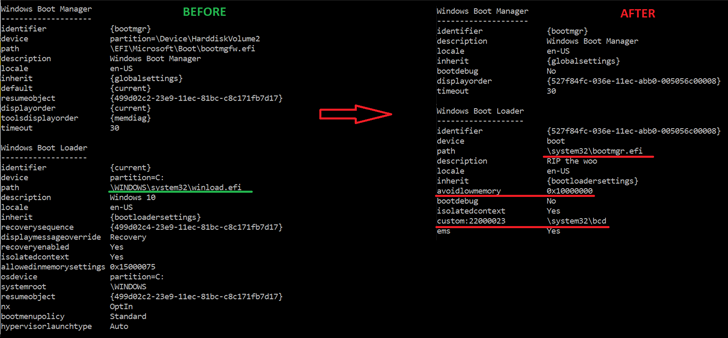
The precise modus operandi used to deploy the bootkit is unfamiliar as nevertheless, but it starts with an installer ingredient that’s dependable for creating the information to the EFI technique partition, disabling HVCI and BitLocker, and then rebooting the host.
The restart is adopted by the weaponization of CVE-2022-21894 to attain persistence and put in the bootkit, just after which it is routinely executed on every single process start off to deploy the kernel driver.
When the driver is tasked with launching the consumer-method HTTP downloader and running next-stage kernel-method payloads, the latter is able of executing commands received from the C2 server over HTTPS.
This incorporates downloading and executing a kernel driver, DLL, or a typical executable fetching bootkit updates, and even uninstalling the bootkit from the contaminated method.
“Quite a few critical vulnerabilities influencing security of UEFI units have been learned in the past number of decades,” Smolár claimed. “Unfortunately, thanks the complexity of the entire UEFI ecosystem and linked source-chain troubles, many of these vulnerabilities have still left several methods susceptible even a extensive time just after the vulnerabilities have been preset – or at minimum just after we were being informed they had been fastened.”
“It was just a matter of time in advance of someone would get edge of these failures and build a UEFI bootkit able of functioning on systems with UEFI Safe Boot enabled.”
Identified this posting fascinating? Follow us on Twitter and LinkedIn to browse a lot more exclusive information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 CISOs Are Stressed Out and It’s Putting Companies at Risk
CISOs Are Stressed Out and It’s Putting Companies at Risk