Digital content is a double-edged sword, providing vast benefits while simultaneously posing significant threats to organizations across the globe. The sharing of digital content has increased significantly in recent years, mainly via email, digital documents, and chat. In turn, this has created an expansive attack surface and has made ‘digital content’ the preferred carrier for cybercriminals and nation-state threat actors. Digital content is the easy way in for attackers, whether it be to launch sophisticated attacks, malware distribution and phishing or ransomware attacks.
Governments and highly regulated industries are particularly vulnerable due to the notoriety attackers can receive and the “prize” or impact that can come in compromising their networks. For Governments and defense agencies, this could mean losing access to sensitive and classified information. For critical infrastructure and highly regulated industries that could mean disruption to services or physical damage. Both have real-world consequences for organizations and civilians.
A Game of Digital Cat and Mouse
Cybersecurity is a relentless digital game of cat and mouse. Where threat actors consistently outpace defenses with ever-evolving approaches and tools. History has shown us an “arms race” where attackers have the upper hand.
From the earliest computer viruses to today’s sophisticated attacks and advanced persistent threats. From the creation of anti-virus came polymorphic viruses designed to evade detection.
Polymorphic viruses evade detection by changing their signature so that existing databases of malware signatures do not flag it as suspicious.
To sandboxing, designed to bolster detection technologies, which ultimately fell to evasion techniques quickly developed by attackers.
Malware can evade detection in sandbox environments by lying dormant for a pre-determined length of time before detonating or by requiring a form of user input before detonation.
Cybercriminals have continuously adapted to exploit new vulnerabilities, pushing cybersecurity experts to develop more advanced and proactive solutions in a never-ending struggle to safeguard digital content.
Despite advances in cybersecurity technologies, detection products are increasingly struggling to keep up with evolving threats. The sheer volume of digital content generated daily can overwhelm systems leading to delayed responses and missed threats. This gap between threat evolution and detection capabilities highlights the urgent need for more advanced, proactive cybersecurity measures to protect against the next generation of digital threats.
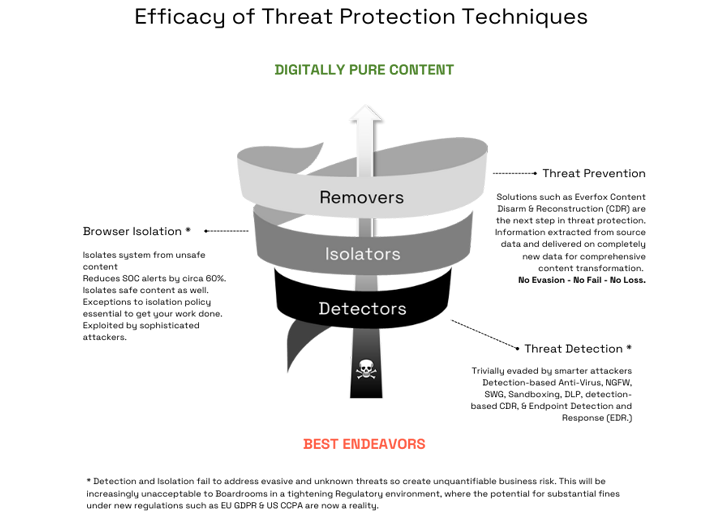
The Path to Secure Content
Securing digital content requires a shift to prevention-based approaches. Stopping potential breaches before they occur, rather than relying on detecting only known attacks, or attacks that have already infiltrated systems. Leveraging proactive strategies such as threat prevention solutions, threat intelligence or AI and behavioral analysis, enhances organizational security postures and minimizes the likelihood of costly data breaches and operational disruptions.
“Too often, organizations wait until disaster strikes to prioritize cyber defenses. As cyber threats rise in frequency and magnitude, a decisive shift toward prevention is crucial. By proactively identifying and mitigating risks, Everfox is building stronger, more resilient defenses for our customers worldwide.”
Shaun Bierweiler, Chief Revenue & Operating Officer, Everfox
The Next Step in Digital Security
Techniques such as traditional detection-based Content Disarm and Reconstruction (CDR) work by removing code and fixing any data that is not conformant with the file format specification. Relying on accurate knowledge of what constitutes code and assumes that applications can always handle complete data safely if it conforms with a specification. However, these are NOT safe assumptions and can lead to fatal flaws due to the heavy reliance on detection. This is why Everfox has innovated beyond detection-based CDR.
Rather than trying to detect malware, Everfox Threat Protection Solutions utilizes a unique transformation-based CDR which assumes that no data can be trusted.
It works by following this simple process:
The new data completely replicates the original file, is fully revisable and delivered in near real-time but without the threat of embedded malware.
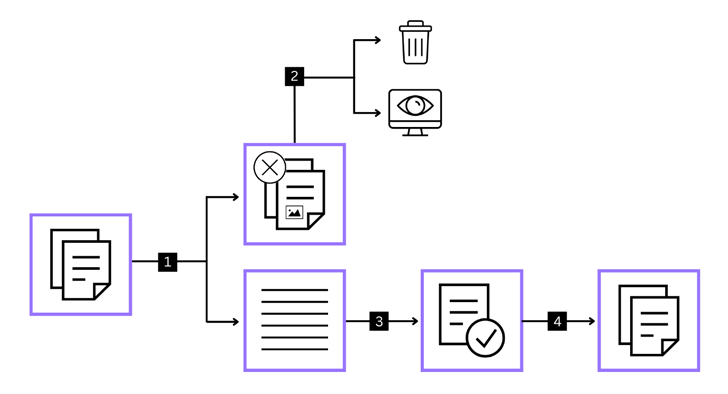
That’s why Everfox CDR is a gamechanger for mitigating the threat of even the most advanced zero-day attacks and exploits. Pivoting from detection to prevention in this way means it doesn’t require constant updating with the signatures of the latest new and zero-day malware as they become available, so the defense is always up to date. It’s a true zero-trust approach to digital security. Trust nothing, verify everything.
Why Government Organizations and Critical Industries are Choosing Everfox CDR:
- No reliance on detection technologies.
- No false positives for SOC teams to investigate – reducing the cost of expensive cyber security resources.
- Defeats advanced threats and zero-days.
- Overcomes the efficacy, usability, scaling and integration flaws inherent within traditional detection-based CDR.
- Stops stegware, polymorphic and fileless threats.
- Native content transforms into pixel perfect digital content that has little to no impact on user experience.
- Can be deployed on-prem, in cloud or as a service via an API.

As cyber threats continue to evolve in sophistication and frequency, relying solely on detection is becoming an increasingly inadequate defense. Now more than ever Governments and regulated industries need to embrace more proactive measures to cybersecurity. Pivoting towards prevention-based cyber threat solutions is paramount to safeguarding national security, public safety, and economic stability.
Resulting in a safer and more secure digital future for all.
Note: This expertly contributed article is written by Daniel Turner, Vice President of Everfox International, renowned for pioneering zero trust anti-malware solutions and building cybersecurity services.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com


 Russian Hackers Target Europe with HeadLace Malware and Credential Harvesting
Russian Hackers Target Europe with HeadLace Malware and Credential Harvesting