Nearly 1.3 million Android-based TV boxes running outdated versions of the operating system and belonging to users spanning 197 countries have been infected by a new malware dubbed Vo1d (aka Void).
“It is a backdoor that puts its components in the system storage area and, when commanded by attackers, is capable of secretly downloading and installing third-party software,” Russian antivirus vendor Doctor Web said in a report published today.
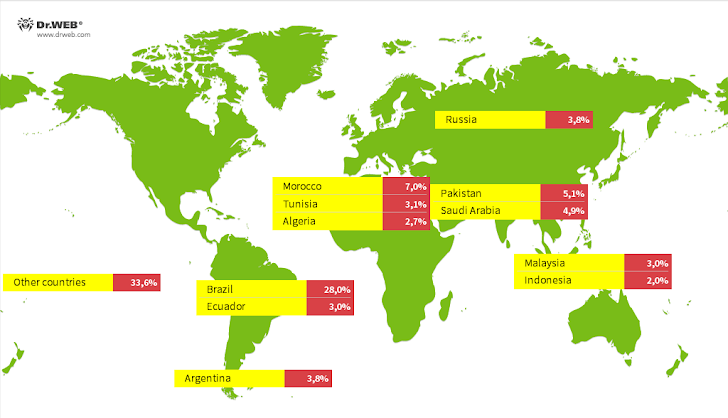
A majority of the infections have been detected in Brazil, Morocco, Pakistan, Saudi Arabia, Argentina, Russia, Tunisia, Ecuador, Malaysia, Algeria, and Indonesia.
It’s currently not known what the source of the infection is, although it’s suspected that it may have either involved an instance of prior compromise that allows for gaining root privileges or the use of unofficial firmware versions with built-in root access.
The following TV models have been targeted as part of the campaign –
- KJ-SMART4KVIP (Android 10.1; KJ-SMART4KVIP Build/NHG47K)
- R4 (Android 7.1.2; R4 Build/NHG47K)
- TV BOX (Android 12.1; TV BOX Build/NHG47K)
The attack entails the substitution of the “/system/bin/debuggerd” daemon file (with the original file moved to a backup file named “debuggerd_real”), as well as the introduction of two new files – “/system/xbin/vo1d” and “/system/xbin/wd” – which contain the malicious code and operate concurrently.
“Before Android 8.0, crashes were handled by the debuggerd and debuggerd64 daemons,” Google notes in its Android documentation. “In Android 8.0 and higher, crash_dump32 and crash_dump64 are spawned as needed.”
Two different files shipped as part of the Android operating system – install-recovery.sh and daemonsu – have been modified as part of the campaign to trigger the execution of the malware by starting the “wd” module.

“The trojan’s authors probably tried to disguise one if its components as the system program ‘/system/bin/vold,’ having called it by the similar-looking name ‘vo1d’ (substituting the lowercase letter ‘l’ with the number ‘1’),” Doctor Web said.
The “vo1d” payload, in turn, starts “wd” and ensures it’s persistently running, while also downloading and running executables when instructed by a command-and-control (C2) server. Furthermore, it keeps tabs on specified directories and installs the APK files that it finds in them.
“Unfortunately, it is not uncommon for budget device manufacturers to utilize older OS versions and pass them off as more up-to-date ones to make them more attractive,” the company said.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com


 Exposed Selenium Grid Servers Targeted for Crypto Mining and Proxyjacking
Exposed Selenium Grid Servers Targeted for Crypto Mining and Proxyjacking