Danger actors are leveraging manipulated research success and bogus Google advertisements that trick consumers who are looking to down load legitimate program these types of as WinSCP into putting in malware as a substitute.
Cybersecurity firm Securonix is tracking the ongoing activity underneath the name Website positioning#LURKER.
“The destructive advertisement directs the person to a compromised WordPress web site gameeweb[.]com, which redirects the person to an attacker-controlled phishing web site,” security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a report shared with The Hacker News.
The risk actors are thought to leverage Google’s Dynamic Look for Ads (DSAs), which mechanically generates adverts centered on a site’s material to provide the destructive advertisements that just take the victims to the contaminated web-site.

The top purpose of the elaborate multi-phase attack chain is to entice consumers into clicking on the fake, lookalike WinSCP site, winccp[.]net, and obtain the malware.
“Targeted traffic from the gaweeweb[.]com internet site to the phony winsccp[.]net web-site depends on a proper referrer header currently being set correctly,” the scientists claimed. “If the referrer is incorrect, the person is ‘Rickrolled’ and is despatched to the infamous Rick Astley YouTube video.”
The last payload can take the kind of a ZIP file (“WinSCP_v.6.1.zip”) that comes with a set up executable, which, when released, employs DLL side-loading to load and execute a DLL file named python311.dll that is present within just the archive.
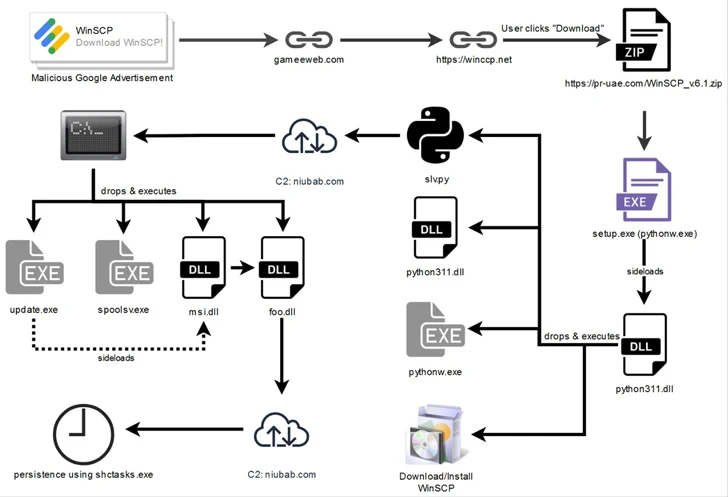
The DLL, for its section, downloads and executes a reputable WinSCP installer to keep up the ruse, while stealthily dropping Python scripts (“slv.py” and “wo15.py”) in the background to activate the malicious behavior. It can be also accountable for environment up persistence.
Equally the Python scripts are intended to create get hold of with a distant actor-controlled server to get further more guidance that make it possible for the attackers to run enumeration instructions on the host.
“Presented the reality that the attackers ended up leveraging Google Adverts to disperse malware, it can be believed that the targets are constrained to any individual searching for WinSCP software package,” the scientists claimed.
“The geoblocking made use of on the web-site hosting the malware implies that those in the U.S. are victims of this attack.”

This is not the first time Google’s Dynamic Lookup Adverts have been abused to distribute malware. Late previous month, Malwarebytes lifted the lid on a campaign that targets users hunting for PyCharm with backlinks to a hacked site hosting a rogue installer that paves the way for the deployment of facts-stealing malware.
Malvertising has developed in acceptance amongst cybercriminals in the previous few several years, with various malware strategies making use of the tactic for assaults in new months.
Previously this 7 days, Malwarebytes unveiled an uptick in credit rating card skimming campaigns in Oct 2023 that’s estimated to have compromised hundreds of e-commerce web sites with an purpose to steal economic details by injecting convincing counterfeit payment pages.
Located this posting interesting? Comply with us on Twitter and LinkedIn to go through more unique articles we submit.
Some parts of this article are sourced from:
thehackernews.com


 FCC Enforces Stronger Rules to Protect Customers Against SIM Swapping Attacks
FCC Enforces Stronger Rules to Protect Customers Against SIM Swapping Attacks