A nascent botnet identified as Andoryu has been uncovered to exploit a now-patched critical security flaw in the Ruckus Wi-fi Admin panel to break into susceptible devices.
The flaw, tracked as CVE-2023-25717 (CVSS score: 9.8), stems from inappropriate managing of HTTP requests, primary to unauthenticated remote code execution and a entire compromise of wi-fi Entry Level (AP) tools.
Andoryu was initial documented by Chinese cybersecurity agency QiAnXin before this February, detailing its capability to connect with command-and-control (C2) servers utilizing the SOCKS5 protocol.

When the malware is regarded to weaponize distant code execution flaws in GitLab (CVE-2021-22205) and Lilin DVR for propagation, the addition of CVE-2023-25717 exhibits that Andoryu is actively increasing its exploit arsenal to ensnare more devices into the botnet.
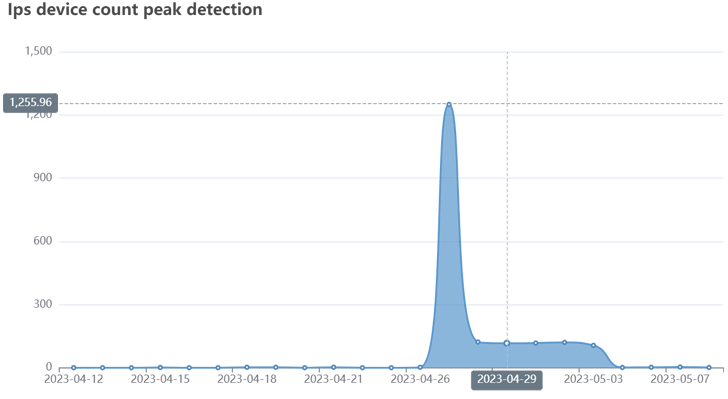
“It is made up of DDoS attack modules for distinctive protocols and communicates with its command-and-manage server using SOCKS5 proxies,” Fortinet FortiGuard Labs researcher Cara Lin claimed, adding the newest campaign commenced in late April 2023.
Further investigation of the attack chain has unveiled that when the Ruckus flaw is used to attain accessibility to a product, a script from a remote server is dropped onto the contaminated device for proliferation.
The malware, for its aspect, also establishes get in touch with with a C2 server and awaits even further guidance to launch a DDoS attack from targets of curiosity using protocols like ICMP, TCP, and UDP.
The charge related with mounting this kind of attacks is advertised by using a listing on the seller’s Telegram channel, with month-to-month plans ranging from $90 to $115 based on the duration.
RapperBot Botnet Provides Crypto Mining to its Checklist of Capabilities
The warn follows the discovery of new versions of the RapperBot DDoS botnet that incorporate cryptojacking operation to profit off compromised Intel x64 programs by dropping a Monero crypto miner.
RapperBot strategies have principally targeted on brute-forcing IoT devices with weak or default SSH or Telnet qualifications to grow the botnet’s footprint for launching DDoS assaults.
Approaching WEBINARLearn to Prevent Ransomware with True-Time Safety
Be part of our webinar and find out how to cease ransomware attacks in their tracks with authentic-time MFA and support account protection.
Help you save My Seat!
Fortinet stated it detected the most up-to-date iteration of the RapperBot miner activity in January 2023, with the assaults providing a Bash shell script that, in turn, is capable of downloading and executing separate XMRig crypto miners and RapperBot binaries.
Subsequent updates to the malware have merged the two disparate features into a solitary bot customer with mining capabilities, whilst also using steps to terminate competing miner processes.

Apparently, none of the new RapperBot samples with the integrated XMRig miner incorporate self-propagation capabilities, increasing the probability of an alternate distribution mechanism.
“This suggests the feasible availability of an external loader operated by the menace actor that abuses the credentials gathered by other RapperBot samples with brute forcing capabilities and infects only x64 devices with the put together bot/miner,” Fortinet theorized.
RapperBot’s expansion to cryptojacking is however yet another indication that monetarily enthusiastic risk operators leave no stone unturned to “extract the utmost benefit from machines contaminated by their botnets.”
The twin developments also arrive as the U.S. Justice Department declared the seizure of 13 internet domains linked with DDoS-for-seek the services of providers.
Observed this post exciting? Adhere to us on Twitter and LinkedIn to study much more special material we post.
Some parts of this article are sourced from:
thehackernews.com

 Twitter Finally Rolling Out Encrypted Direct Messages — Starting with Verified Users
Twitter Finally Rolling Out Encrypted Direct Messages — Starting with Verified Users