“Dozens” of businesses across the globe have been targeted as component of a wide business enterprise email compromise (BEC) marketing campaign that involved the use of adversary-in-the-middle (AitM) methods to carry out the assaults.
“Pursuing a effective phishing endeavor, the danger actor obtained first entry to 1 of the target employee’s account and executed an ‘adversary-in-the-middle’ attack to bypass Office environment365 authentication and gain persistence accessibility to that account,” Sygnia researchers mentioned in a report shared with The Hacker News.
“After gaining persistence, the risk actor exfiltrated data from the compromised account and applied his entry to distribute the phishing assaults towards other victim’s staff members together with numerous exterior specific organizations.”

The results appear fewer than a week right after Microsoft specific a identical combination of an AitM phishing and a BEC attack aimed at banking and fiscal companies organizations.
BEC cons generally entail tricking a target around email into sending dollars or divulging private company facts. In addition to personalizing the emails to the supposed sufferer, the attacker can also impersonate a dependable figure to accomplish their targets.
This, in flip, can be achieved by seizing management of the account by way of an elaborate social engineering scheme, following which the scammer emails the company’s shoppers or suppliers fake invoices that ask for payment to a fraudulent financial institution account.
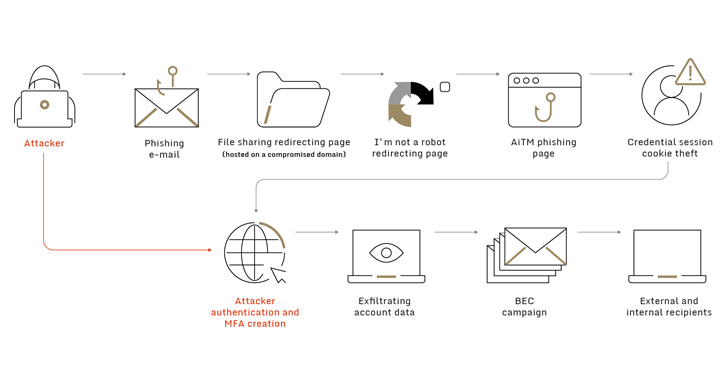
In the attack chain documented by Sygnia, the attacker was observed sending a phishing email made up of a backlink to a purported “shared document” that eventually redirected the sufferer to an AitM phishing site developed to harvest the entered qualifications and a single-time passwords.
Forthcoming WEBINAR🔐 Mastering API Security: Being familiar with Your Genuine Attack Surface
Find the untapped vulnerabilities in your API ecosystem and acquire proactive actions toward ironclad security. Be a part of our insightful webinar!
Be a part of the Session.wn-button,.wn-label,.wn-label:afterexhibit:inline-block.check_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-ideal-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimensions:13pxmargin:20px 0font-bodyweight:600letter-spacing:.6pxcolor:#596cec.wn-label:soon afterwidth:50pxheight:6pxcontent:”border-major:2px strong #d9deffmargin: 8px.wn-titlefont-size:21pxpadding:10px 0font-excess weight:900text-align:leftline-peak:33px.wn-descriptiontext-align:leftfont-dimensions:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
What is actually far more, the menace actors are said to have abused the short term accessibility to the compromised account to sign up a new multi-issue authentication (MFA) unit in get to get a persistent distant foothold from a diverse IP tackle located in Australia.
“In addition to exfiltration of sensitive information from the victim’s account, the danger actor made use of this entry to ship new phishing email messages made up of the new destructive backlink to dozens of the client’s personnel as properly as additional specific organizations,” Sygnia scientists stated.
The Israeli cybersecurity enterprise further claimed the phishing mails unfold in a “worm-like manner” from just one focused firm to the other and amid workforce within just the same business. The specific scale of the campaign is at this time unfamiliar.
Discovered this article appealing? Stick to us on Twitter and LinkedIn to go through a lot more unique content material we submit.
Some parts of this article are sourced from:
thehackernews.com

 #InfosecurityEurope: What TechUK’s New Plan Means for Cybersecurity
#InfosecurityEurope: What TechUK’s New Plan Means for Cybersecurity