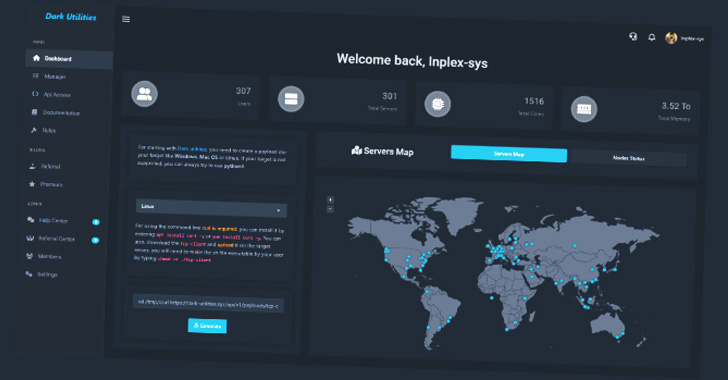
A nascent support called Dark Utilities has currently attracted 3,000 buyers for its skill to provide command-and-handle (C2) solutions with the goal of commandeering compromised units.
“It is marketed as a suggests to enable remote obtain, command execution, dispersed denial-of-services (DDoS) attacks and cryptocurrency mining functions on infected units,” Cisco Talos said in a report shared with The Hacker Information.
Dark Utilities, which emerged in early 2022, is advertised as a “C2-as-a-Company” (C2aaS), supplying obtain to infrastructure hosted on the clearnet as perfectly as the TOR network and affiliated payloads with aid for Windows, Linux, and Python-primarily based implementations for a mere €9.99.

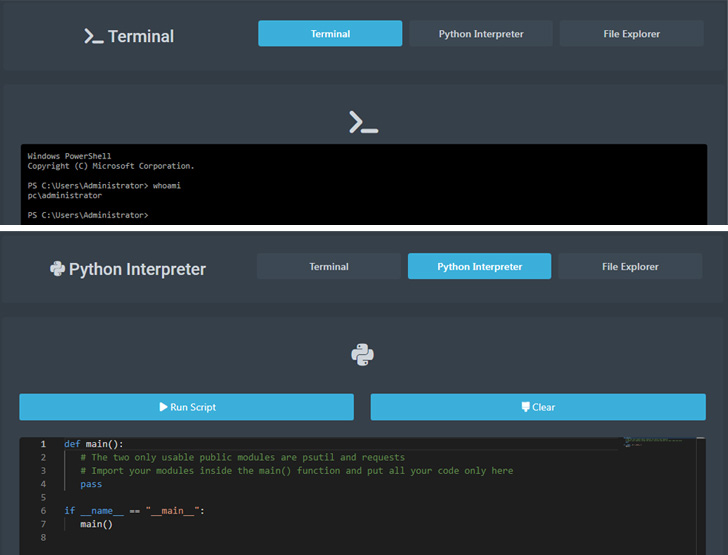
Authenticated people on the system are presented with a dashboard that makes it doable to generate new payloads tailored to a distinct operating technique that can then be deployed and executed on target hosts.
In addition, buyers are presented an administrative panel to run instructions on the equipment underneath their command on setting up an energetic C2 channel, efficiently granting the attacker total obtain to the devices.
The notion is to enable threat actors to target several architectures devoid of necessitating considerable improvement efforts. Also extended to its buyers are specialized assist and assistance via Discord and Telegram.
“Presented the fairly very low expense in comparison to the sum of functionality the system delivers, it is possible beautiful to adversaries attempting to compromise methods without having necessitating them to build their possess C2 implementation within just their malware payloads,” the scientists pointed out.
To insert gas to the fireplace, the malware artifacts are hosted within just the decentralized InterPlanetary File Process (IPFS) remedy, generating them resilient to written content moderation or law enforcement intervention in a manner very similar to “bulletproof hosting.”
“IPFS is at present staying abused by a wide variety of threat actors who are applying it to host destructive contents as section of phishing and malware distribution campaigns,” Talos researcher Edmund Brumaghin instructed The Hacker Information.
“[The IPFS gateway] allows pcs on the internet to entry contents hosted inside of the IPFS network with no the need for a shopper software package set up, similar to how Tor2Web gateways deliver that features for content hosted inside of the Tor network.”
Dark Utilities is considered to be the handiwork of a risk actor who goes by the moniker Inplex-sys in the cybercriminal underground house, with Talos figuring out some sort of a “collaborative relationship” involving Inplex-sys and just one of the operators of a botnet company called Sensible Bot.
“Platforms like Dark Utilities reduced the barrier to entry for cybercriminals getting into the risk landscape by enabling them to speedily launch attacks targeting a wide variety of running methods,” the scientists reported.
“They also provide various methods that can be used to more monetize entry obtained to techniques in corporate environments and could lead to additional deployment of malware in the environment when preliminary obtain has been obtained.”
Located this posting intriguing? Comply with THN on Fb, Twitter and LinkedIn to read through much more special written content we put up.
Some parts of this article are sourced from:
thehackernews.com

 UK Branded Europe’s “Capital of Card Fraud”
UK Branded Europe’s “Capital of Card Fraud”