3CX claimed it can be operating on a software package update for its desktop app right after several cybersecurity distributors sounded the alarm on what seems to be an lively offer chain attack that is making use of digitally signed and rigged installers of the popular voice and movie conferencing software to focus on downstream buyers.
“The trojanized 3CX desktop app is the to start with phase in a multi-phase attack chain that pulls ICO files appended with Foundation64 knowledge from GitHub and ultimately prospects to a third-stage infostealer DLL,” SentinelOne researchers stated.
The cybersecurity business is monitoring the action less than the name SmoothOperator, stating the risk actor registered a massive attack infrastructure as significantly back as February 2022.
3CX, the company guiding 3CXDesktopApp, claims to have additional than 600,000 buyers and 12 million end users in 190 countries, some of which include nicely-regarded names like American Specific, BMW, Honda, Ikea, Pepsi, and Toyota, among many others.
Even though the 3CX PBX consumer is available for various platforms, Sophos, citing telemetry facts, pointed out that the attacks noticed so considerably are confined to the Windows Electron shopper of the PBX phone method.
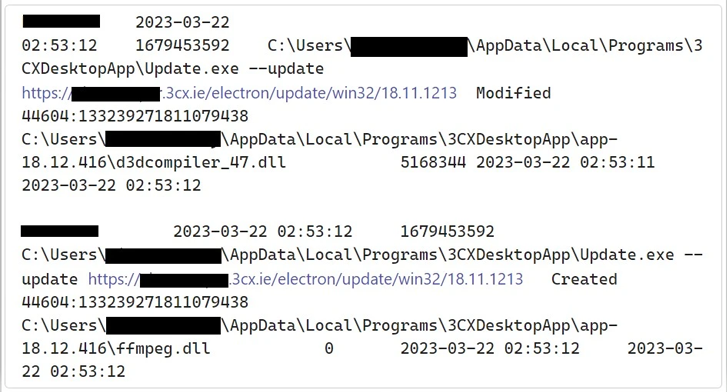
The infection chain, in a nutshell, will take gain of the DLL side-loading method to load a rogue DLL (ffmpeg.dll) that is built to retrieve an icon file (ICO) payload. The GitHub repository hosting the file has considering the fact that been taken down.
The info stealer is capable of gathering method information and facts and delicate information saved in Google Chrome, Microsoft Edge, Courageous, and Mozilla Firefox browsers.
Cybersecurity company CrowdStrike reported it suspects the attack to be joined to a North Korean country-condition actor it tracks as Labyrinth Chollima (aka Nickel Academy), a sub-cluster in just the infamous Lazarus Group.
WEBINARDiscover the Concealed Dangers of 3rd-Social gathering SaaS Applications
Are you mindful of the hazards connected with 3rd-celebration application entry to your firm’s SaaS apps? Be part of our webinar to study about the styles of permissions staying granted and how to minimize risk.
RESERVE YOUR SEAT
“The destructive activity involves beaconing to actor-managed infrastructure, deployment of second-phase payloads, and, in a small quantity of scenarios, hands-on-keyboard activity,” CrowdStrike extra.
In a discussion board article, 3CX’s CEO Nick Galea said it is in the procedure of issuing a new develop around the subsequent couple hours, and famous that Android and iOS variations are not impacted. “Regrettably this took place for the reason that of an upstream library we use grew to become contaminated,” Galea stated, devoid of specifying a lot more particulars.
In the interim, the firm is urging its clients to uninstall the app and set up it again, or alternatively use the PWA consumer.
Observed this short article exciting? Adhere to us on Twitter and LinkedIn to read through far more exclusive articles we publish.
Some parts of this article are sourced from:
thehackernews.com


 AI ‘brain’ created from core materials for OLED TVs
AI ‘brain’ created from core materials for OLED TVs