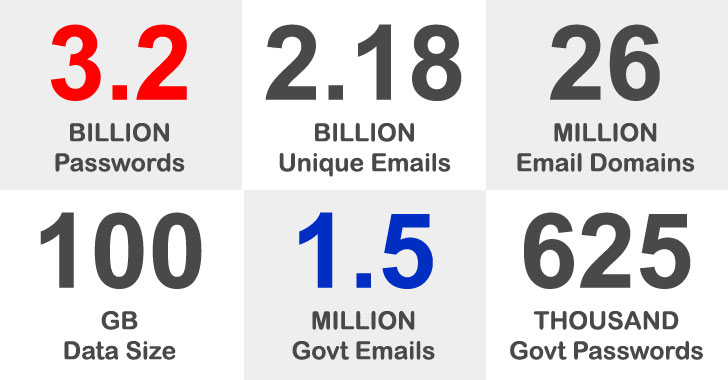
A staggering amount of 3.28 billion passwords joined to 2.18 billion exceptional email addresses had been exposed in what’s a person of the greatest details dumps of breached usernames and passwords.
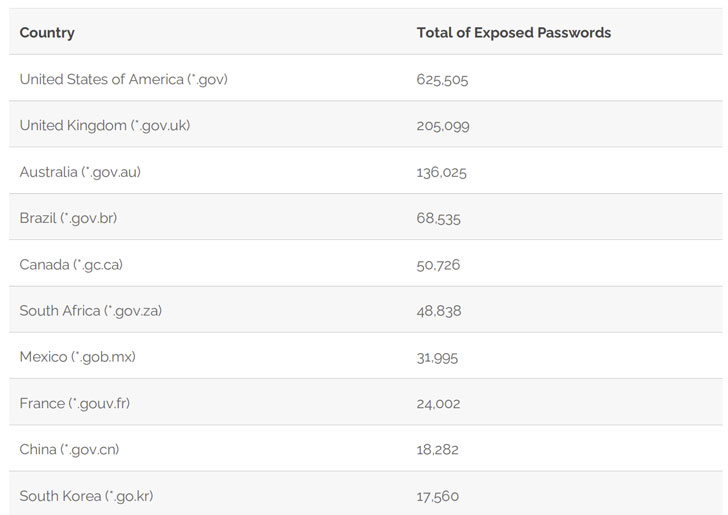
In addition, the leak involves 1,502,909 passwords associated with email addresses from governing administration domains across the globe, with the U.S. government by itself having up 625,505 of the exposed passwords, followed by the U.K (205,099), Australia (136,025), Brazil (68,535), and Canada (50,726).
The findings occur from an investigation of a significant 100GB details established identified as “COMB21” — aka Compilation of Numerous Breaches — that was released for no cost in an on-line cybercrime forum previously this February by putting together facts from numerous leaks in various companies and corporations that happened over the years.

It’s really worth noting that a leak doesn’t indicate a breach of general public administration programs. The passwords are stated to have been received via strategies these kinds of as password hash cracking just after remaining stolen or by way of phishing assaults and eavesdropping on insecure, plaintext connections.
The top rated 10 U.S. federal government domains afflicted by the leak are as follows:
- State Office – point out.gov (29,144)
- Veterans Affairs Division – va.gov (28,937)
- Office of Homeland Security – dhs.gov (21,575)
- National Aeronautics and Space Administration – nasa.gov (15,665)
- Interior Earnings Services – irs.gov (10,480)
- Middle for Disorder Control and Prevention – cdc.gov (8,904)
- Office of Justice – usdoj.gov (8,857)
- Social Security Administration – ssa.gov (8,747)
- U.S. Postal Company – usps.gov (8,205), and
- Environmental Safety Company – epa.gov (7,986)
Apparently, this leak also includes 13 credentials connected to emails of the Oldsmar drinking water plant in Florida, as earlier documented by CyberNews. Nevertheless, there’s no evidence that the breached passwords have been to have out the cyberattack in February. In contrast, only 18,282 passwords connected to Chinese governing administration domains and 1,964 passwords from individuals related to Russia were being laid bare.

“It is an indication that the passwords in these nations, created up of regional alphabets, are considerably less targeted by hackers. It is an unpredicted layer of defense in relation to the Roman alphabet,” stated Syhunt Founder and Main Visionary Officer (CVO) Felipe Daragon.

On a similar take note, a notorious danger actor named ShinyHunters has posted an alleged databases consisting of 20 million BigBasket buyers for totally free, nearly five months following the Indian on the internet grocery supply startup verified a details breach. In accordance to Below the Breach’s Alon Gal, the databases contains users’ email addresses, phone figures, residential addresses, hashed passwords, dates of beginning, and buy histories.
In the previous, ShinyHunters has been linked to the sale of private facts from several firms, such as Zoosk, SocialShare, Tokopedia, TeeSpring, Conscious, Minted, Chatbooks, Dave, Promo, Mathway, Wattpad, MeetMindful.com, and StarTribune.
Users who have experienced their info uncovered are strongly encouraged to alter their present passwords.
Discovered this report exciting? Observe THN on Fb, Twitter and LinkedIn to read through much more unique articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 California plans to end oil extraction by 2045
California plans to end oil extraction by 2045