A new phishing-as-a-company (PhaaS or PaaS) platform named Greatness has been leveraged by cybercriminals to goal small business end users of the Microsoft 365 cloud services given that at the very least mid-2022, proficiently reducing the bar to entry for phishing assaults.
“Greatness, for now, is only focused on Microsoft 365 phishing internet pages, giving its affiliates with an attachment and connection builder that creates remarkably convincing decoy and login internet pages,” Cisco Talos researcher Tiago Pereira said.
“It contains characteristics this sort of as possessing the victim’s email tackle pre-filled and exhibiting their suitable business symbol and background picture, extracted from the goal organization’s genuine Microsoft 365 login web page.”
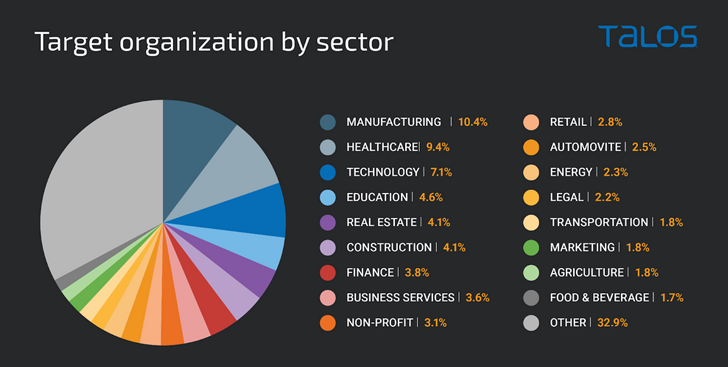
Strategies involving Greatness have primarily manufacturing, overall health care, and technology entities found in the U.S., the U.K., Australia, South Africa, and Canada, with a spike in action detected in December 2022 and March 2023.

Phishing kits like Greatness offer menace actors, rookies or usually, a price-successful and scalable one particular-quit shop, building it possible to design convincing login web pages affiliated with a variety of on the internet providers and bypass two-variable authentication (2FA) protections.
Specially, the genuine-hunting decoy pages function as a reverse proxy to harvest credentials and time-dependent a single-time passwords (TOTPs) entered by the victims.
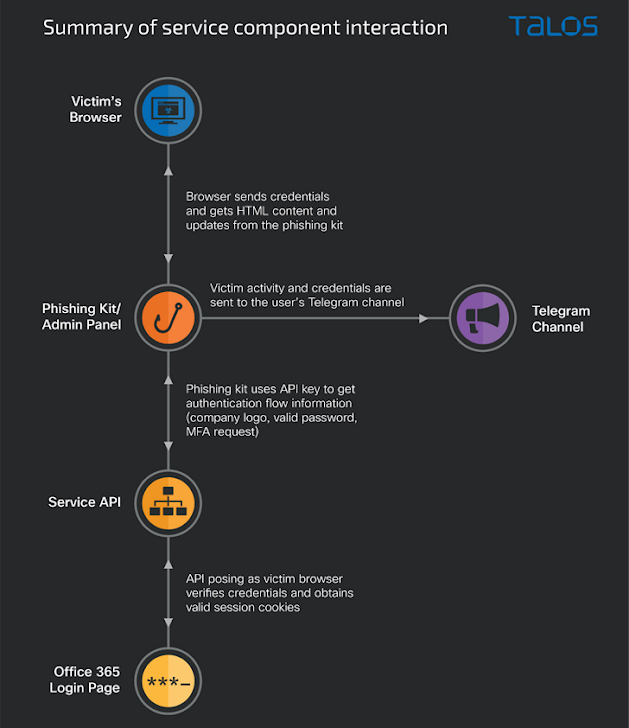
Attack chains start with malicious e-mail made up of an HTML attachment, which, upon opening, executes obfuscated JavaScript code that redirects the consumer to a landing web page with the recipient’s email tackle now pre-filled and prompts for their password and MFA code.
The entered credentials and tokens are subsequently forwarded to the affiliate’s Telegram channel for getting unauthorized entry to the accounts in question.
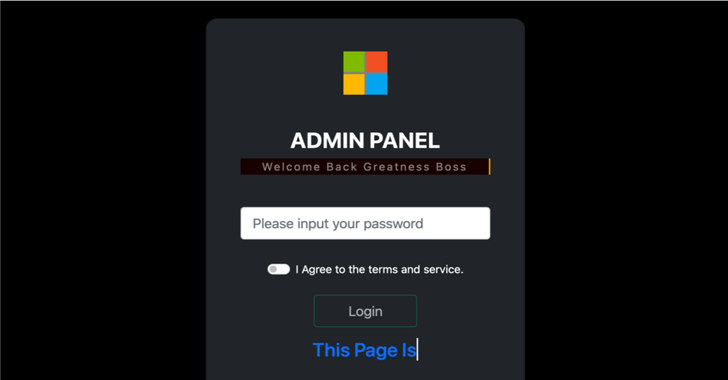
The AiTM phishing kit also will come with an administration panel that allows the affiliate to configure the Telegram bot, maintain observe of stolen information, and even establish booby-trapped attachments or hyperlinks.
Impending WEBINARLearn to Quit Ransomware with Genuine-Time Security
Be part of our webinar and learn how to end ransomware assaults in their tracks with real-time MFA and assistance account defense.
Conserve My Seat!
What is actually more, just about every affiliate is expected to have a legitimate API essential in purchase to be able to load the phishing page. The API key also prevents undesired IP addresses from viewing the phishing webpage and facilitates behind-the-scenes conversation with the precise Microsoft 365 login webpage by posing as the sufferer.
“Doing the job together, the phishing package and the API carry out a ‘man-in-the-middle’ attack, requesting information from the sufferer that the API will then post to the reputable login web page in serious time,” Pereira mentioned.
“This makes it possible for the PaaS affiliate to steal usernames and passwords, along with the authenticated session cookies if the target works by using MFA.”
The results appear as Microsoft has begun imposing number matching in Microsoft Authenticator thrust notifications as of Could 8, 2023, to improve 2FA protections and fend off prompt bombing assaults.
Uncovered this post fascinating? Stick to us on Twitter and LinkedIn to read additional distinctive information we put up.
Some parts of this article are sourced from:
thehackernews.com

 XWorm Malware Exploits Follina Vulnerability in New Wave of Attacks
XWorm Malware Exploits Follina Vulnerability in New Wave of Attacks